Email continues to be the most exploited communication channel in enterprise environments. Despite heavy investment in technical controls, many organizations still experience incidents because governance has not kept pace with tooling.
A structured Email Security Policy closes that gap. It transforms email security from a collection of configurations into a defined risk management discipline. For CISOs and IT leaders, this policy becomes a formal mechanism for accountability, resilience, and regulatory alignment, and not just an IT document stored on an internal portal.
When properly designed and enforced, it reduces ambiguity, standardizes controls across business units, and aligns email protection with overall enterprise risk tolerance.
What Is Email Security Policy?
When executives ask what is email security policy, the answer should not be limited to acceptable use guidelines. Email security policies in cyber security represent a governance framework that defines how email systems are secured, monitored, accessed, and audited. It integrates technical safeguards, identity protection, behavioral standards, incident response requirements, and compliance mandates into one enforceable governance model.
In practical terms, email security policies in cyber security establish:
- The minimum security standards email systems must meet
- The responsibilities of users and administrators
- Monitoring and reporting expectations
- Regulatory and data protection alignment
- Escalation procedures during incidents
Without this structure, organizations rely heavily on default cloud configurations or fragmented controls. With policy, however, email becomes a governed asset with measurable oversight.
For broader context on aligning policy development to ensure governance do check out our Email Security Guide.
Why Email Security Policies are Strategic Imperative
Finance approvals, legal communications, executive directives, and customer interactions all flow through email. Any compromise can have immediate financial and reputational damage.
Consider a BEC attack targeting the finance department. Even if technical filters detect most malicious emails, an impersonation attempt may bypass defenses. Without a policy mandating MFA, transaction verification procedures, and escalation protocols, the organization remains exposed.
Effective policy reduces that exposure by standardizing:
- Authentication requirements
- Verification workflows for sensitive transactions
- Monitoring thresholds
- Incident response timelines
In this way, policy reduces both technical and procedural vulnerabilities. It ensures that security does not rely on individual discretion during high-pressure scenarios.
Common Weaknesses in Enterprise Email Security Policies
Many organizations have documented policies, yet enforcement gaps remain. These gaps often include:
- MFA exceptions for privileged accounts
- Lack of executive impersonation safeguards
- DMARC policies left unenforced
- No defined remediation timelines
- Absence of measurable KPIs
Such inconsistencies weaken governance and increase exposure, particularly during targeted attacks.
Defining Scope and Applicability
An effective Email Security Policy must clearly define its scope as ambiguity leads to inconsistent enforcement.
The policy should explicitly apply to:
- All employees, contractors, and third-party users
- All corporate email accounts, including shared and privileged mailboxes
- Cloud and on-premises email environments
- Integrated collaboration platforms where email workflows intersect
For multinational organizations, scope should also address cross-border data handling and regional regulatory differences. Without defined scope, enforcement becomes inconsistent. Clear applicability strengthens audit defensibility and operational clarity.
Roles and Responsibilities
A mature Email Security Policy should assign ownership explicitly. This typically includes:
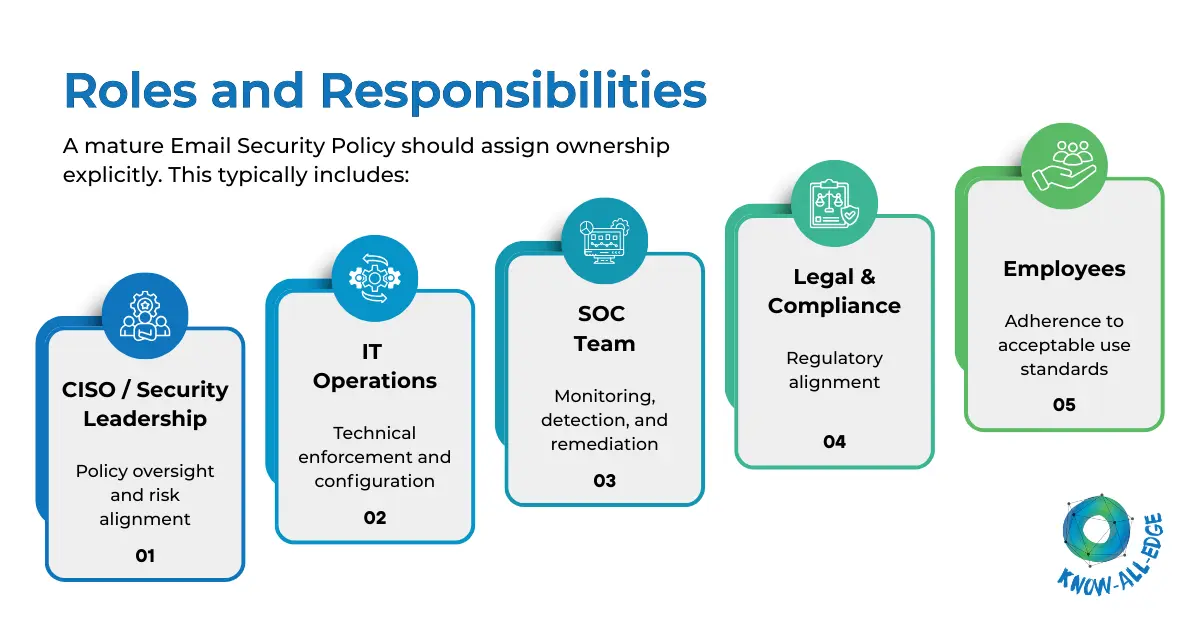
- CISO / Security Leadership – Policy oversight and risk alignment
- IT Operations – Technical enforcement and configuration
- SOC Team – Monitoring, detection, and remediation
- Legal & Compliance – Regulatory alignment
- Employees – Adherence to acceptable use standards
Clearly documented responsibilities reduce ambiguity during incidents and audits.
Core Areas Enterprise Email Security Policies Must Address
While policies vary by industry and risk appetite, mature enterprises consistently focus on several foundational domains.
(1) Identity and Access Governance
Compromised credentials remain one of the most common causes of enterprise breaches. An effective Email Security Policy establishes strict identity standards, including:
- Multi-factor authentication for all users
- Conditional access controls
- Role-based mailbox permissions
- Enhanced monitoring for privileged accounts
Executive and finance accounts should receive additional scrutiny, given their elevated risk profile. This ensures that access to email systems is controlled, monitored, and limited according to business necessity.
(2) Domain Protection and Anti-Spoofing Controls
Email spoofing and domain impersonation continue to drive financial fraud. A strong policy mandates the implementation and enforcement of SPF, DKIM, and DMARC standards. Importantly, it should define clear timelines for moving DMARC from monitoring mode to quarantine or reject.
Without enforced authentication, attackers can impersonate the organization externally, damaging brand trust and partner relationships.
(3) Threat Detection and Technical Standards
Policy must define the minimum level of technical protection required across the enterprise. This includes secure email gateway configurations, advanced phishing detection, sandboxing of suspicious attachments, and automated mailbox remediation capabilities.
(4) Executive and High-Risk User Protection
Attackers frequently target executives and senior leadership. A mature policy includes differentiated controls for high-risk roles, such as:
- Stricter conditional access rules
- Impersonation monitoring tuned for VIP accounts
- Mandatory secondary approval for high-value financial transactions
- Higher alert prioritization within SOC workflows
(5) Third-Party and Supply Chain Email Risk
Modern email attacks often exploit trusted vendor relationships. Effective policy should address communications involving partners and suppliers, including:
- Verification procedures for vendor payment changes
- Monitoring anomalies in external communication patterns
- Controls for shared mailboxes handling third-party interactions
(6) Outbound Data Protection and Encryption
Outbound exposure is frequently underestimated. Policies should clearly define how sensitive information is classified, monitored, and encrypted before leaving the organization.
This may include automated encryption triggers, restrictions on forwarding confidential information, and data loss prevention requirements. These safeguards protect regulatory posture and brand integrity.
(7) Monitoring, Metrics, and Incident Response
A policy without measurable oversight cannot demonstrate effectiveness. Mature organizations define clear monitoring expectations and incident response timelines within their policy.
This typically includes:
- Integration with SIEM and SOC workflows
- Defined remediation SLAs
- Enterprise-wide purge procedures for confirmed threats
- Regular reporting to executive leadership
Tracking metrics such as phishing click rates, reporting rates, and mean time to remediate provides leadership with tangible indicators of risk posture.
(8) Security Awareness and Behavioral Controls
Even advanced AI-based detection cannot eliminate human error. Therefore, email security best practices must be embedded into policy through continuous awareness initiatives.
This includes structured phishing simulations, role-based training for high-risk teams, and measurable reporting mechanisms. Over time, organizations should observe a decline in click rates and an increase in proactive reporting behavior.
Aligning Email Security Policy with Compliance Requirements
Email often contains regulated data, including personal information, financial records, and intellectual property. Effective policy must therefore align with regulatory frameworks such as GDPR, HIPAA, or PCI-DSS.
This alignment may require defined retention schedules, archiving standards, encryption enforcement, and audit logging requirements. When policy and compliance are integrated, organizations reduce audit friction and demonstrate proactive governance.
Enterprises frequently align their policy development with industry-recognized email security best practices to ensure that compliance and operational security remain synchronized.
Addressing AI-Driven Email Threats
Attackers increasingly leverage AI to generate convincing phishing emails, automate impersonation, and bypass traditional signature-based controls.
An effective policy must anticipate these evolving threats by requiring:
- Behavioral analysis-based detection capabilities
- Enhanced impersonation monitoring
- Strict verification protocols for sensitive requests
Due to these rapidly evolving AI-driven phishing, deepfake impersonation, and evolving malware tactics. The Email Security Policy should define:
- Annual formal review cycles
- Trigger events requiring immediate updates (e.g., major incidents)
- Alignment with emerging threat intelligence
- Documentation version control
This forward-looking approach ensures policy remains aligned with emerging risk patterns.
Email Security Policy Maturity Model
Enterprises typically progress through stages of policy maturity:
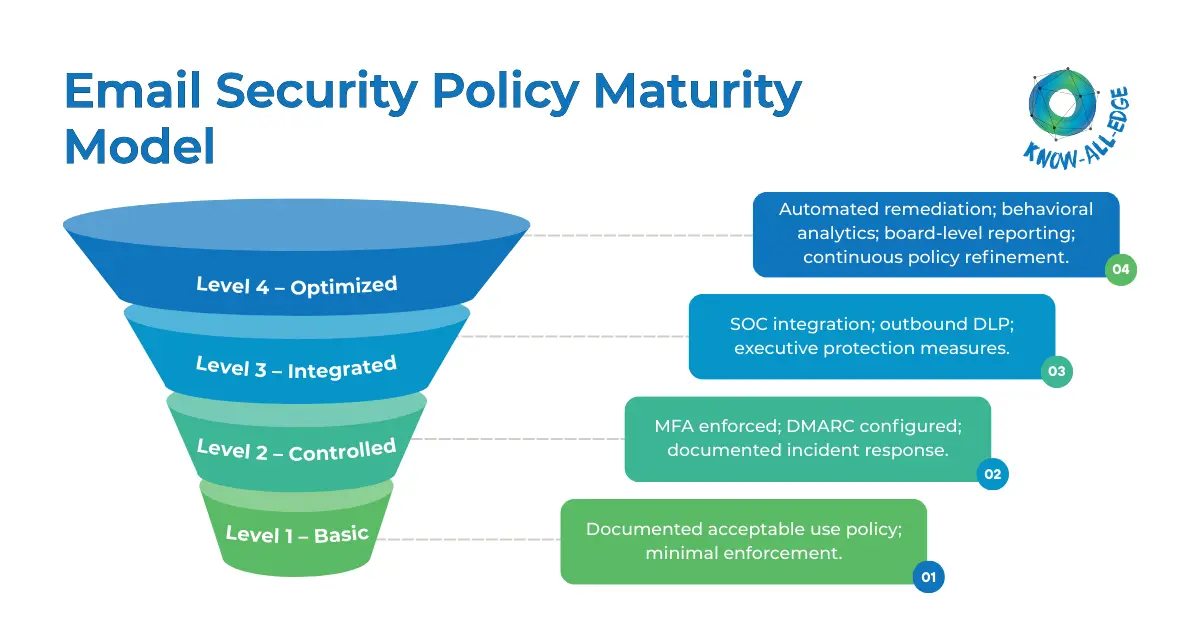
Level 1 – Basic:
Documented acceptable use policy; minimal enforcement.
Level 2 – Controlled:
MFA enforced; DMARC configured; documented incident response.
Level 3 – Integrated:
SOC integration; outbound DLP; executive protection measures.
Level 4 – Optimized:
Automated remediation; behavioral analytics; board-level reporting; continuous policy refinement.
This model helps leadership benchmark progress and prioritize investment.
A Practical Roadmap for CISOs
For organizations formalizing or modernizing their Email Security Policy, a phased approach provides structure.
First, assess risk. Review historical incidents, authentication posture, and compliance exposure.
Second, define enforceable standards. Policies should be specific enough to drive action but not so technical that they become operational manuals.
Third, align tools with policy. Ensure technical controls directly map to policy requirements.
Finally, establish continuous review cycles. Threat patterns evolve rapidly, and policies should be evaluated at least annually, if not quarterly.
This disciplined approach ensures the policy remains a living governance instrument rather than a static document.
Conclusion
Email will remain a primary attack surface for the foreseeable future. Technology reduces exposure, but governance sustains protection.
A well-defined Email Security Policy ensures that email security is not reactive, fragmented, or tool-dependent. Instead, it becomes a structured, measurable, and enforceable risk management discipline embedded into enterprise operations.
We at Know All Edge assist enterprises in designing, reviewing, and operationalizing Email Security Policy frameworks aligned with business risk and regulatory obligations. We remain vendor-neutral, focusing on sustainable protection models tailored to your infrastructure and operational maturity.
FAQs: Email Security Policy
What is email security policies in cyber security?
These are governance frameworks that defines how email systems are protected, accessed, monitored, and aligned with business risk and compliance requirements.
How detailed should an Email Security Policy be?
It should clearly define enforceable standards and responsibilities while leaving technical configuration specifics to operational procedures.
Who should approve the policy?
Executive leadership, typically including the CISO, CIO, legal, and compliance stakeholders, should formally approve the document.
How does an Email Security Policy support compliance?
It establishes documented controls for encryption, retention, authentication, and monitoring—demonstrating structured oversight during audits.
Is policy still necessary if advanced security tools are deployed?
Yes. Tools enforce controls, but policy defines accountability, expectations, and governance.
