Many organizations today say they are “implementing Zero Trust.” In practice, what they often deploy is Zero Trust Network Access (ZTNA) to secure access to internal applications.
But implementing ZTNA is not simply installing a new security product. It requires understanding the components of ZTNA and how they work together to enforce identity-driven access control.
Security leaders evaluating ZTNA often ask questions like:
- What components are required in ZTNA architecture?
- How do identity, device posture, and policy enforcement interact?
- Where should ZTNA sit within the broader security stack?
Understanding the ZTNA components list helps organizations design architectures that actually enforce Zero Trust principles rather than simply replacing VPN connectivity.
What Are ZTNA Components?
ZTNA components are the technologies and control points that work together to verify users, evaluate device posture, enforce security policies, and securely broker access to applications.
Unlike traditional network security models that rely on perimeter defenses, ZTNA enforces security decisions at the moment a user attempts to access a resource.
A typical ZTNA components list includes:
- Identity provider
- Device trust verification
- Policy engine
- Policy enforcement point
- Secure application gateway
- Continuous monitoring and analytics
Each component performs a specific function, and the architecture only works effectively when these components operate together.
Identity Provider
Identity is the foundation of ZTNA.
Before any access decision can be made, the system must confirm who the user is.
ZTNA platforms typically integrate with enterprise identity providers such as:
- Microsoft Entra ID
- Okta
- Google Identity
- Active Directory
These systems provide authentication capabilities including:
- Single Sign-On (SSO)
- Multi-factor authentication (MFA)
- Identity federation
When a user requests access to an application, the identity provider verifies the user’s credentials and passes authentication signals to the ZTNA platform.
This ensures that access decisions are tied to identity rather than network location.
Device Trust Verification
In a Zero Trust environment, verifying identity alone is not enough.
Security teams must also evaluate the security posture of the device attempting to access applications.
Device trust verification checks whether endpoints meet organizational security requirements.
These checks may include:
- Endpoint protection status
- OS patch levels
- Device compliance policies
- Presence of EDR or security agents
If a device fails posture checks, the ZTNA platform can restrict access or require remediation.
This helps reduce the risk of compromised devices accessing sensitive resources.
Policy Engine
The policy engine is where access decisions are made.
Once identity and device posture information are collected, the policy engine evaluates the access request against predefined security policies.
Policies may include conditions such as:
- Only allow access from managed devices
- Require MFA for sensitive applications
- Restrict access from high-risk locations
- Limit access to specific user groups
This policy-driven approach ensures that security decisions are consistent and automated across the environment.
Policy Enforcement Point
The policy enforcement point (PEP) is responsible for implementing the decisions made by the policy engine.
When the policy engine approves an access request, the enforcement point allows the connection to proceed. If the request violates policy, access is blocked.
In most ZTNA deployments, enforcement occurs at the ZTNA access broker or gateway, which sits between users and applications.
This ensures that users never connect directly to internal resources.
Secure Application Gateway
The secure application gateway is the component that actually brokers the connection between users and applications.
Rather than exposing applications directly to the internet, the gateway creates a secure access path.
Key characteristics of this approach include:
- Applications remain hidden from the public internet
- Users connect through the ZTNA platform instead of directly to the network
- Access is limited to specific applications
This architecture significantly reduces the risk of unauthorized scanning, exploitation, or lateral movement within the network.
Continuous Monitoring
Zero Trust assumes that threats can emerge at any time.
That is why continuous monitoring is a critical component of ZTNA.
ZTNA platforms monitor:
- User behavior
- Device posture changes
- Access patterns
- Application usage
If suspicious activity is detected, the system can:
- Re-authenticate the user
- Restrict access
- Terminate active sessions
This allows organizations to detect threats in real time rather than relying solely on perimeter defenses.
How ZTNA Components Work Together
Individually, each component plays a role in securing access. But the real strength of ZTNA lies in how these components operate together.
A typical ZTNA access request follows this sequence:
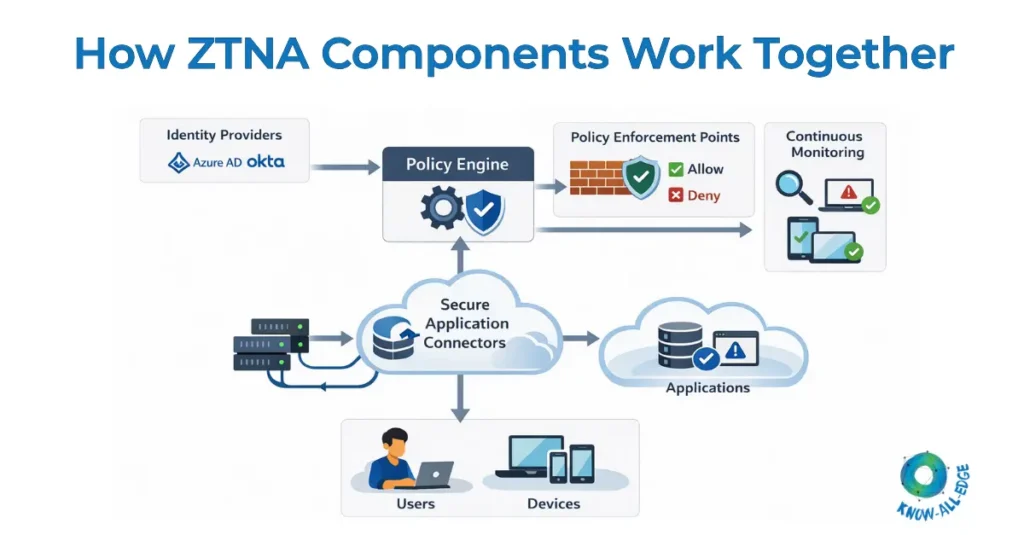
- A user attempts to access an application.
- The identity provider authenticates the user.
- Device posture is evaluated to verify trust.
- The policy engine evaluates the request.
- The policy enforcement point allows or denies access.
- The secure application gateway brokers the connection.
- Continuous monitoring evaluates user activity during the session.
This architecture ensures that access decisions are identity-driven, policy-based, and continuously evaluated.
For organizations implementing secure access strategies, understanding how these components interact is essential when designing ZTNA architecture.
Conclusion
ZTNA has become a critical technology for organizations implementing Zero Trust security models.
However, successful deployment depends on understanding the components of ZTNA and how they function together.
Identity verification, device posture checks, policy enforcement, and secure application gateways all play a role in enforcing secure access to applications.
When implemented correctly, these components enable organizations to move away from network-based trust models and adopt a more resilient approach to access security.
As hybrid work, SaaS adoption, and cloud infrastructure continue to expand, ZTNA architectures built on these components will play an increasingly important role in enterprise security strategies.
Looking to implement the right components for a Zero Trust environment?
Know All Edge helps enterprises integrate identity verification, device posture checks, and policy enforcement within scalable ZTNA solutions. Talk to our team to build your Zero Trust access framework.
Frequently Asked Questions
What are the main ZTNA components?
The main ZTNA components include identity providers, device trust verification systems, policy engines, policy enforcement points, secure application gateways, and monitoring tools.
Why are ZTNA components important?
ZTNA components work together to enforce identity-based access control, verify device trust, and secure application access without exposing internal networks.
How does the policy engine work in ZTNA?
The policy engine evaluates access requests using predefined security rules that consider identity, device posture, location, and application sensitivity.
What is the role of a secure application gateway in ZTNA?
A secure application gateway brokers connections between users and applications, ensuring that internal resources are not directly exposed to the internet.
Do ZTNA components replace VPN infrastructure?
In many cases, ZTNA components replace VPN-based remote access systems by providing application-level access instead of network-level connectivity.
Can ZTNA work with existing identity providers?
Yes. Most ZTNA solutions integrate with identity providers such as Microsoft Entra ID, Okta, and Active Directory.
