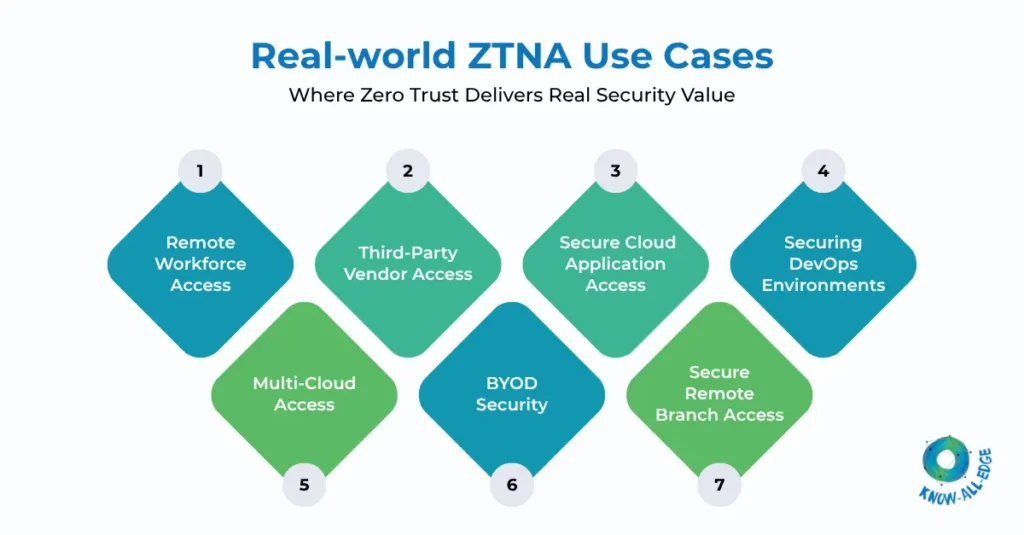
Most organizations today are not asking what Zero Trust is anymore. The real question has shifted to: “Where does Zero Trust actually deliver measurable security outcomes?”
This is where understanding ZTNA use cases becomes important.
Zero Trust Network Access (ZTNA) is often positioned as a replacement for VPN. But that’s only one part of the story. In practice, ZTNA enables organizations to solve a wide range of access-related security challenges across users, devices, applications, and environments.
From securing remote employees to controlling third-party access and protecting cloud workloads, ZTNA is increasingly becoming the access control layer for modern enterprises.
If you’re exploring how Zero Trust is implemented at a structural level, our guide on Zero Trust architecture explains how identity and policy-driven access replace traditional network-based trust.
Let us explore the real-world ZTNA Use Cases.
(1) ZTNA for Remote Workforce Access
The shift to hybrid and remote work exposed one of the biggest limitations of traditional security models. VPN-based access extends the corporate network to user devices, increasing the attack surface. A compromised device connected through VPN can potentially access multiple internal systems.
ZTNA takes a different approach.
Instead of connecting users to the network, it connects them only to specific applications after verifying identity and device posture.
What changes with ZTNA?
- No network-level exposure
- Application-level access only
- Continuous verification of users and devices
For organizations with distributed teams, this is often the first and most immediate ZTNA use case.
(2) ZTNA for Third-Party Vendor Access
Vendors, contractors, and partners often require access to internal applications.
Traditionally, organizations provide VPN access to these external users—sometimes with limited controls. This creates significant risk because:
- Vendors may use unmanaged devices
- Access is often broader than required
- Visibility into activity is limited
ZTNA enables granular, application-specific access for third-party users without exposing the internal network.
Key advantages:
- No network access for external users
- Access limited to specific applications
- Identity and policy-based enforcement
This is particularly relevant for industries dealing with sensitive data or strict compliance requirements.
(3) ZTNA for Secure Cloud Application Access
As organizations adopt SaaS and cloud platforms, the concept of a corporate network perimeter becomes less relevant.
Users need secure access to:
- SaaS applications (Microsoft 365, Salesforce, etc.)
- Cloud-hosted applications
- Internal apps exposed via cloud infrastructure
ZTNA allows organizations to enforce consistent access policies across cloud environments without relying on network-based controls.
Why this matters:
- Applications are not exposed to the internet
- Access is controlled based on identity and context
- Security policies are consistent across environments
This is one of the most important zero trust use cases for cloud-first organizations.
(4) ZTNA for Multi-Cloud Access
Modern enterprises rarely operate in a single environment.
Applications are distributed across:
- Public cloud providers
- Private cloud environments
- On-premise data centers
Managing access across these environments using traditional network-based controls is complex and difficult to scale.
ZTNA simplifies this by acting as a central access control layer.
What ZTNA enables:
- Unified access policies across environments
- Secure access without network backhauling
- Consistent identity-based enforcement
For organizations with multi-cloud strategies, ZTNA becomes a critical component of access security.
(5) ZTNA for BYOD Security
Bring Your Own Device (BYOD) is another area where traditional security models struggle.
Allowing personal devices to connect to corporate networks via VPN introduces risk because:
- Devices may not meet security standards
- Visibility into device posture is limited
- Malware or compromised endpoints can enter the network
ZTNA mitigates this risk by:
- Verifying device posture before granting access
- Restricting access based on device trust level
- Providing application-level access instead of network access
This allows organizations to support flexible work models without compromising security.
(6) ZTNA for Securing DevOps Environments
Development and DevOps environments often require access to:
- Code repositories
- CI/CD pipelines
- Cloud infrastructure
- Internal APIs
These environments are high-value targets because they often provide access to critical systems and data.
ZTNA enables secure access by:
- Enforcing identity-based access to development tools
- Restricting access to specific resources
- Monitoring developer activity
This helps organizations secure DevOps workflows without introducing friction for engineering teams.
(7) ZTNA for Secure Remote Branch Access
Branch offices and remote locations often rely on network-based connectivity models.
Traditionally, this involves:
- MPLS connections
- Site-to-site VPNs
- Complex network configurations
ZTNA offers an alternative approach.
Instead of connecting entire networks, ZTNA enables secure access at the application level.
Benefits include:
- Reduced reliance on network infrastructure
- Simplified access management
- Improved scalability for distributed locations
For organizations with multiple branch offices, this use case can significantly simplify access architecture.
Conclusion
ZTNA is often introduced as a replacement for VPN, but its real value lies in how it enables organizations to rethink access control across the entire environment. From remote workforce access to cloud security, third-party access, and DevOps protection, these ZTNA use cases demonstrate how Zero Trust can be applied in real-world scenarios.
Every organization has different access challenges—remote users, third-party vendors, cloud workloads, or legacy systems. The key is identifying where ZTNA delivers the most impact in your environment.
For security leaders, the goal is not just to deploy ZTNA, but to identify where it delivers the most impact. As organizations continue to adopt hybrid work models and cloud-first strategies, ZTNA will play a central role in securing access without relying on traditional network boundaries.
Know All Edge helps organizations map real-world ZTNA use cases to their infrastructure and implement ZTNA solutions that align with security, performance, and scalability requirements.
Speak with our experts to explore how Zero Trust can be applied to your environment.
Frequently Asked Questions
What are the main ZTNA use cases?
Common ZTNA use cases include remote workforce access, third-party vendor access, secure cloud application access, multi-cloud environments, BYOD security, and DevOps protection.
How does ZTNA improve remote access security?
ZTNA provides application-level access instead of network-level access, reducing the attack surface and limiting lateral movement.
Can ZTNA secure cloud applications?
Yes. ZTNA enables secure access to SaaS and cloud-hosted applications by enforcing identity-based access policies.
Is ZTNA useful for third-party access?
Yes. ZTNA allows organizations to grant vendors and partners access to specific applications without exposing internal networks.
How does ZTNA support BYOD environments?
ZTNA verifies device posture and restricts access based on device trust, allowing secure access even from unmanaged devices.
