Most organizations exploring Zero Trust eventually reach a critical inflection point:
“Which ZTNA solution should we actually deploy?”
Up until this stage, discussions are largely architectural: Zero Trust principles, identity-first access, replacing VPN. But once organizations move into evaluation mode, the conversation shifts significantly.
Security leaders are no longer asking what is ZTNA. They are asking:
Security leaders stop asking what ZTNA is and start asking harder questions:
- Which platform aligns with our identity and endpoint stack?
- Can it handle our mix of legacy, cloud, and SaaS applications?
- Will it scale across geographies without performance trade-offs?
These are the right questions. But many organizations still make a costly mistake at this stage: choosing a ZTNA platform based on feature counts rather than architectural fit.
The best ZTNA solution isn’t the one with the longest capability list. It’s the one that integrates cleanly with your identity strategy, maps to your application landscape, and supports your long-term Zero Trust roadmap.
What is a ZTNA Solution?
A ZTNA solution is a platform that enables secure, identity-based access to applications without exposing the underlying network.
Traditional VPNs extend network-level access to users, creating broad attack surfaces and lateral movement risk. ZTNA operates on a fundamentally different model:
- Authenticates users through your identity provider before any access is granted
- Validates device posture in real time, not just at login
- Enforces policy-based access decisions per application, not per network segment
- Connects users only to specific applications—never the broader network
The result: applications remain invisible and inaccessible unless explicitly authorized. This isn’t just a security improvement—it’s a structural one.
If you want to understand how these controls are enforced technically, refer to our ZTNA components blog, which breaks down identity, policy, and enforcement layers.
Key Capabilities to Look for in ZTNA Solutions
When evaluating zero trust network access solutions, feature parity matters less than security enforcement consistency. Here’s what to look for:
(1) Identity-Centric Access
ZTNA starts with identity. A solution must deeply integrate with identity providers such as Azure AD or Okta. Look for:
- Native SSO and MFA enforcement
- Conditional access policy support
- Federated identity across environments
Without strong identity integration, Zero Trust becomes ineffective.
(2) Device Posture Enforcement
Valid credentials don’t equal trusted access. A compromised endpoint with a legitimate login is still a critical risk vector.
A mature ZTNA solution should:
- Assess endpoint security posture continuously—not just at session start
- Integrate with EDR/XDR platforms for real-time signals
- Restrict or revoke access based on device health changes
This ensures access decisions factor in both who is connecting and what they’re connecting from.
(3) Application Segmentation
One of ZTNA’s most significant security advantages is granular, application-level access control. Unlike VPNs, ZTNA prevents lateral movement by design.
Your platform should:
- Enforce access to specific applications, not network segments
- Support segmentation across on-prem, cloud, and SaaS environments
- Minimize blast radius in the event of a breach
(4) Continuous Verification
Zero Trust is not a one-time decision. A strong ZTNA platform should continuously evaluate:
- User behavior patterns mid-session
- Device posture changes in real time
- Contextual risk signals from integrated security tools
For example, if a user’s session shows anomalous activity, access should be re-evaluated and restricted dynamically, without waiting for the next authentication cycle.
(5) Visibility and Audit Logging
Security without visibility is incomplete. ZTNA solutions should provide:
- Detailed, queryable access logs
- User and application activity insights
- Anomaly detection and alerting capabilities
- This isn’t just operationally useful—it’s a compliance requirement in most regulated industries.
Cloud-Native ZTNA: Why Architecture Matters
Most modern ZTNA platforms are cloud-delivered—and this isn’t just a deployment preference. It reflects a fundamental architectural shift.
Cloud-native ZTNA solutions:
- Eliminate dependency on on-premises infrastructure and hardware refresh cycles
- Provide globally distributed points of presence, reducing latency for remote and distributed workforces
- Scale dynamically without capacity planning constraints
This model aligns with where applications actually live today—across SaaS, multi-cloud, and hybrid environments. It also forms the technical foundation of SASE architectures, where security enforcement moves closer to the user rather than centralizing in legacy data centers.
ZTNA Within SASE Platforms
In mature security environments, ZTNA is rarely deployed in isolation. Most organizations adopting Zero Trust at scale are doing so within a SASE (Secure Access Service Edge) framework, where ZTNA is one component of a broader, converged security stack.
A full SASE platform typically includes:
- Secure Web Gateway (SWG) for internet traffic control
- Cloud Access Security Broker (CASB) for SaaS visibility and governance
- Firewall-as-a-Service (FWaaS) for network-level threat prevention
- ZTNA for application access control
In this architecture, ZTNA handles who accesses what—while the surrounding components handle how that traffic is inspected and secured.
If you’re evaluating a SASE vs. standalone ZTNA approach, the distinction matters significantly for your long-term security architecture.
ZTNA Integration with Identity and Endpoint Security
ZTNA solutions do not operate as standalone systems. Their effectiveness depends heavily on how well they integrate into your existing security ecosystem.
Key integrations include:
- Identity providers → for authentication and access control
- Endpoint security tools → for device posture validation
- SIEM/XDR platforms → for monitoring and threat detection
Without these integrations, Zero Trust becomes fragmented—and gaps in visibility and enforcement begin to appear.
Integration Requirements: What ZTNA Doesn’t Do Alone
ZTNA solutions don’t operate in isolation. Their effectiveness depends on how well they integrate with your existing security ecosystem.
Critical integrations to evaluate:
- Identity providers (Azure AD, Okta, Ping) → authentication and dynamic access control
- Endpoint security tools (CrowdStrike, SentinelOne, Microsoft Defender) → device posture signals
- SIEM/XDR platforms → centralized monitoring, threat correlation, and incident response
Without these integrations, Zero Trust implementations become fragmented. Gaps in visibility and enforcement emerge—often in exactly the places attackers look for.
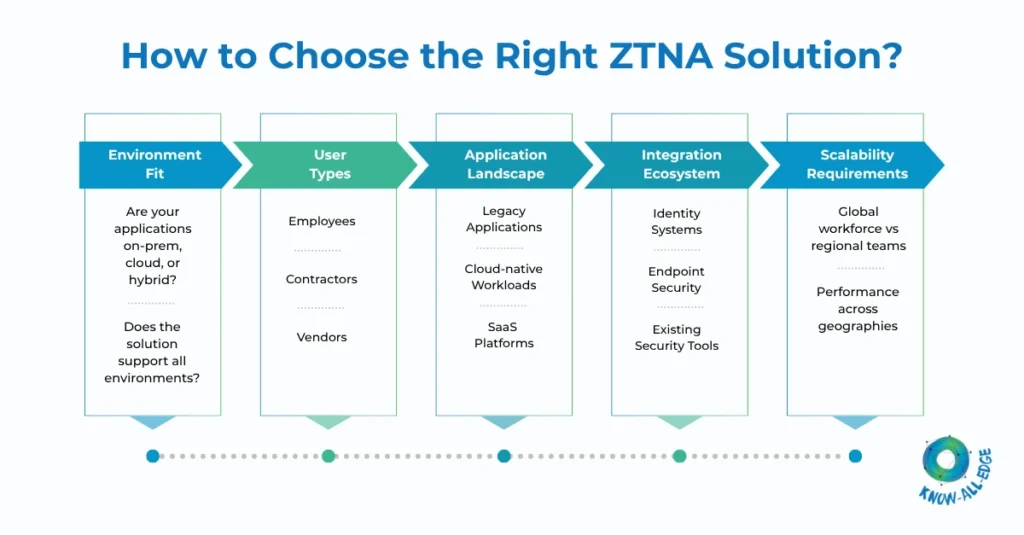
How to Choose the Best ZTNA Solution: A Decision Framework
Choosing a Zero Trust Network Access solution platform is an architectural decision, not a procurement exercise. Align the technology to your environment—not the other way around.
- Environment Fit: Are your applications primarily on-premises, cloud-hosted, or in a hybrid model? Not all ZTNA platforms handle all environments equally.
- User and Access Types: Employees, contractors, and third-party vendors have different risk profiles and access requirements. Your platform needs to handle all three consistently—especially for unmanaged devices.
- Application Landscape: Legacy applications that rely on older network protocols often create friction for ZTNA deployments. Evaluate how each platform handles brownfield environments alongside modern SaaS and cloud-native workloads.
- Integration Ecosystem: Audit your existing identity, endpoint, and security operations stack before vendor selection. ZTNA effectiveness is directly proportional to integration depth.
- Scalability and Global Performance: A solution that performs well for 500 employees in one region may degrade significantly at 50,000 users across multiple geographies. Evaluate PoP coverage, latency benchmarks, and architectural scalability before committing.
ZTNA Deployment Models
ZTNA platforms are typically deployed in one of three models:
| Model | When to Use |
| Cloud-Delivered | Most organizations. Scalable, low overhead, fast deployment. |
| Hybrid | When legacy on-prem applications require connectivity. Combines cloud ZTNA with local connectors. |
| On-Premises | Rare. Applicable in highly regulated environments with strict data residency requirements. |
Most organizations are moving toward cloud-first deployment, with hybrid connectors used selectively for legacy workloads.
Leading ZTNA Solutions Providers
Security leaders typically evaluate a defined shortlist before making an architectural commitment. Commonly evaluated platforms include:
Each platform differs in: Architecture, Integration capabilities, Performance, Deployment flexibility. The right choice depends on your specific environment, not market popularity.
Conclusion: ZTNA Is an Architectural Decision
Organizations that treat ZTNA as a product purchase often end up with fragmented implementations that fail to deliver real Zero Trust enforcement. The checklist gets checked but the architecture doesn’t hold.
Organizations that get it right approach ZTNA as an architectural layer: one that integrates with their identity strategy, maps to their application landscape, and is designed to scale with their security operations.
That’s the difference between Zero Trust as a concept and Zero Trust as a functioning security posture.
How Know All Edge Can Help
At Know All Edge, we help security teams move from Zero Trust strategy to implementation—designing and deploying ZTNA solutions that integrate cleanly with identity, endpoint security, and cloud environments.
Connect with our experts to identify the right Zero Trust access architecture for your organization.
Frequently Asked Questions
What should enterprises evaluate before selecting a ZTNA solution?
Architecture compatibility (cloud, hybrid, on-prem), depth of identity integration, support for both legacy and modern applications, user distribution across regions, and integration fit with existing EDR, SIEM, and IAM platforms.
How do ZTNA solutions handle legacy applications that require network access?
Most modern platforms use application connectors or gateways to securely expose legacy workloads without direct internet exposure. Some legacy protocols may still require hybrid deployment or phased migration. Validate this specifically during vendor evaluation.
What are the most common ZTNA deployment challenges?
Identity integration gaps, incomplete application visibility, inconsistent policy enforcement across hybrid environments, and handling unmanaged or third-party devices. Poor upfront scoping is the leading cause of fragmented rollouts.
Does ZTNA improve or degrade user experience?
Done well, ZTNA improves user experience by enabling direct application access without backhauling through VPN concentrators. Performance depends on vendor PoP coverage, policy design, and integration quality.
Can ZTNA support secure third-party and contractor access?
Yes. This is one of ZTNA’s strongest use cases. Application-level access with identity and device enforcement makes third-party access far more secure than traditional VPN or network-based approaches, without the overhead of managing full network access.
What’s the difference between standalone ZTNA and ZTNA within a SASE platform?
Standalone ZTNA focuses on securing application access. ZTNA within SASE is part of a broader converged architecture that adds web security, SaaS governance, and network-level threat controls. The right choice depends on your current maturity and longer-term security roadmap.
How does ZTNA enforce security continuously during an active session?
ZTNA platforms continuously monitor user behavior, device posture, and contextual signals throughout a session. If risk indicators change (anomalous activity, device compromise signals, or policy violations) access can be dynamically re-evaluated, restricted, or terminated without requiring a new login.
