Many organizations today have started their Zero Trust journey. Some have deployed ZTNA tools, integrated identity providers, or replaced parts of their VPN infrastructure. Yet a common pattern emerges – deployment does not always translate into security outcomes.
Security leaders often find that despite investing in Zero Trust technologies, gaps still exist: over-permissioned access, inconsistent policy enforcement, unmanaged devices slipping through, or lack of visibility into user activity.
This is where Zero Trust best practices become critical. Without the right implementation approach, organizations risk recreating old security problems in a new ZTNA architecture.
Why ZTNA Implementation Fails
Before diving into best practices, it’s important to understand where things typically go wrong.
Treating ZTNA as a VPN Replacement Only
Some organizations approach ZTNA as a direct replacement for VPN without rethinking access models. This limits the value of Zero Trust.
Overlooking Identity and Device Context
ZTNA decisions rely heavily on identity and device posture. Weak identity controls or lack of endpoint visibility undermine the entire model.
Inconsistent Policy Enforcement
If policies vary across applications or environments, security gaps emerge.
Lack of Visibility
Without monitoring user behavior and access patterns, organizations cannot detect anomalies or potential threats.
Ignoring Legacy Dependencies
Certain applications require network-level access. Failing to plan for these scenarios can disrupt operations during migration.
Understanding these challenges helps shape a more effective Zero Trust implementation strategy.
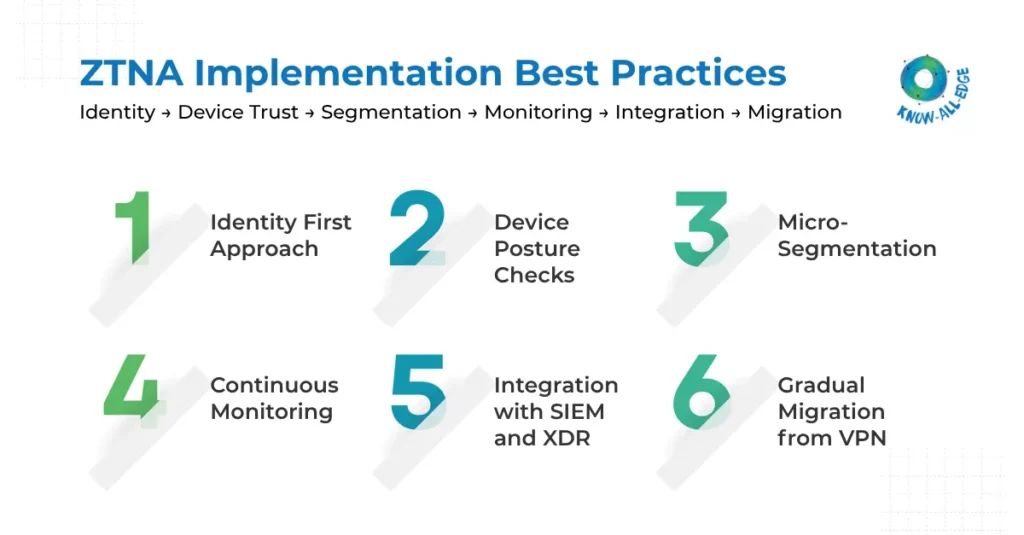
ZTNA Best Practices
Below are the best practices to be followed while implementing ZTNA (the right way).
(1) Identity-First Approach
Identity is the foundation of zero trust best practices. Every access decision should begin with verifying who the user is.
A strong identity-first approach includes:
- Enforcing Multi-Factor Authentication (MFA)
- Implementing Single Sign-On (SSO)
- Integrating with centralized identity providers
- Applying conditional access policies
Access should never be granted based solely on network location. Instead, identity becomes the primary control point for securing application access.
(2) Device Posture Checks
A valid user on a compromised device still represents a security risk. This is why device posture validation is a critical part of ZTNA best practices.
Organizations should evaluate:
- Endpoint protection status
- Patch levels and OS compliance
- Device encryption
- Presence of EDR/XDR agents
Access policies should adapt dynamically based on device trust levels.
For example:
- Fully compliant devices → full access
- Partially compliant devices → restricted access
- Unknown devices → limited or no access
This ensures that security extends beyond identity to the endpoint itself.
(3) Micro-Segmentation
One of the most effective ways to reduce risk in Zero Trust environments is through micro-segmentation. Instead of allowing broad access, applications are segmented so users can only access what they explicitly need.
This approach:
- Limits lateral movement
- Reduces blast radius in case of compromise
- Improves visibility into access patterns
Micro-segmentation works closely with ZTNA by enforcing application-level access controls rather than network-level permissions.
To understand how these controls are enforced technically, refer to our blog on ZTNA components.
(4) Continuous Monitoring
Zero Trust is not a “set and forget” model. Access decisions must be continuously evaluated based on changing risk signals.
Continuous monitoring involves:
- Tracking user behavior
- Detecting anomalies in access patterns
- Monitoring device posture changes
- Identifying suspicious activities
ZTNA platforms can trigger:
- Re-authentication requests
- Session termination
- Access restrictions
This ensures that even after access is granted, security controls remain active.
(5) Integration with SIEM and XDR
ZTNA should not operate in isolation. To gain full visibility and threat detection capabilities, organizations should integrate ZTNA with:
- SIEM (Security Information and Event Management)
- XDR (Extended Detection and Response)
- Endpoint security platforms
This integration enables:
- Correlation of access events with threat signals
- Faster detection of compromised accounts
- Improved incident response
For organizations building a mature security stack, ZTNA becomes one layer within a broader detection and response ecosystem.
(6) Gradual Migration from VPN
One of the most common questions CISOs ask is:
“How do we move from VPN to ZTNA without breaking access?”
The answer is: phased migration.
A typical approach includes:
Step 1: Identify Key Applications
Start with critical or internet-facing applications.
Step 2: Apply ZTNA Controls
Secure these applications using identity-based access.
Step 3: Maintain VPN for Legacy Systems
Continue using VPN for applications that require network-level access.
Step 4: Expand Coverage
Gradually move more applications to ZTNA.
For a deeper understanding of how this transition works, our ZTNA vs VPN comparison explains the architectural differences.
ZTNA Best Practices Checklist
For security leaders planning or refining Zero Trust deployments, this checklist provides a practical reference.
Identity & Access
- Enforce MFA across all users
- Centralize identity management
- Apply conditional access policies
Device Security
- Validate endpoint posture before access
- Integrate endpoint security tools
- Restrict access from unmanaged devices
Access Control
- Enforce least privilege access
- Implement micro-segmentation
- Avoid network-level access where possible
Monitoring & Visibility
- Continuously monitor user behavior
- Integrate with SIEM/XDR
- Analyze access logs regularly
Deployment Strategy
- Start with high-risk applications
- Adopt phased migration from VPN
- Align security policies across environments
Conclusion
Implementing Zero Trust is not just about adopting new technologies, it requires a shift in how access is controlled, monitored, and enforced. These zero trust best practices help organizations move beyond basic ZTNA deployment toward a more mature and resilient security posture.
By focusing on identity, device trust, continuous monitoring, and phased implementation, organizations can reduce risk while enabling secure access across modern environments. As enterprises continue to evolve toward cloud-first and hybrid infrastructures, applying these best practices will be essential for building a scalable Zero Trust strategy.
Know All Edge helps organizations implement ZTNA solutions aligned with Zero Trust best practices, ensuring secure, scalable access across users, devices, and applications. Connect with our experts to strengthen your Zero Trust strategy.
Frequently Asked Questions
What are Zero Trust best practices?
Zero Trust best practices include identity-based access control, device posture validation, least privilege access, continuous monitoring, and integration with security tools like SIEM and XDR.
Why do ZTNA implementations fail?
ZTNA implementations often fail due to weak identity controls, lack of device visibility, inconsistent policy enforcement, and treating ZTNA as a simple VPN replacement.
Is ZTNA enough to implement Zero Trust?
ZTNA is a key component of Zero Trust, but it must be combined with identity management, endpoint security, monitoring, and policy enforcement.
How does micro-segmentation improve Zero Trust?
Micro-segmentation limits access to specific applications, reducing lateral movement and minimizing the impact of security breaches.
What is the role of continuous monitoring in Zero Trust?
Continuous monitoring helps detect anomalies, enforce policies dynamically, and respond to threats in real time.
