For many security leaders, adopting Zero Trust has moved from concept to priority. The traditional model of trusting users inside the network no longer works when employees access applications from anywhere, workloads run across multiple clouds, and third-party vendors require controlled access to internal systems.
This shift is why organizations are implementing Zero Trust Network Access (ZTNA) as part of their broader security architecture. But deploying a ZTNA tool alone does not create Zero Trust. What organizations actually need is a ZTNA framework that defines how identity, device posture, policy enforcement, and access controls work together.
CISOs evaluating Zero Trust often ask questions like:
- What is the ZTNA framework?
- How do we design a Zero Trust access model that actually works?
- What should the implementation roadmap look like?
This article breaks down the ZTNA framework, the principles behind it, and how organizations can implement it effectively.
If you’re exploring the architectural side of Zero Trust, our guide on Zero Trust architecture explains how identity-driven security replaces traditional network trust models.
What is a ZTNA Framework?
A ZTNA framework is the structured model organizations follow to implement Zero Trust Network Access across users, devices, and applications.
Instead of granting broad network connectivity, the framework ensures that access to applications is granted only after verifying identity, device trust, and security policies.
A well-designed framework includes several key elements:
- Identity verification
- Device trust validation
- Policy-based access control
- Continuous monitoring
- Application-level access enforcement
In practical terms, it defines how access decisions are made and enforced within the organization.
Rather than relying on network location as a trust signal, the framework ensures that every access request is evaluated based on identity and context.
To understand the technical building blocks behind this framework, our guide on ZTNA components explains the infrastructure required to enforce these policies.
Identity-Based Access
Identity is the foundation of the ZTNA framework.
Before a user can access an application, their identity must be verified through an enterprise identity provider.
Common authentication mechanisms include:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Identity federation
ZTNA platforms integrate with identity providers such as Microsoft Entra ID, Okta, or Active Directory to verify users before granting access.
Instead of trusting users based on network location, access decisions are tied directly to who the user is and what they are allowed to access.
Device Trust
Identity alone is not sufficient in a Zero Trust model.
Security teams must also verify whether the device attempting to access applications meets organizational security standards.
Device trust checks may include:
- Endpoint security agent status
- OS patch compliance
- Device encryption
- Presence of endpoint detection and response tools
If a device does not meet these security requirements, access may be restricted or additional verification may be required.
This ensures that compromised or unmanaged devices cannot easily access sensitive resources.
Least Privilege Access
One of the most important elements of the ZTNA framework is enforcing least privilege access.
Traditional remote access models often grant users broad network connectivity. Once connected, users may have access to multiple systems beyond what they actually need.
ZTNA takes a different approach.
Instead of network access, users receive application-level access based on policy.
This reduces the risk of attackers moving laterally across systems if credentials are compromised.
Organizations implementing Zero Trust often begin by identifying high-risk applications and applying least privilege access policies to those resources first.
Continuous Verification
Security environments are dynamic. User behavior, device posture, and threat signals can change during an active session.
This is why continuous verification is a critical component of the ZTNA framework.
ZTNA platforms monitor factors such as:
- Changes in device security posture
- Unusual login locations
- Suspicious user activity
- Anomalous application access patterns
If risk indicators appear, the system can trigger additional authentication steps or terminate the session.
Continuous verification helps ensure that access remains secure throughout the user session.
Principles of Zero Trust
At the core of any ZTNA framework are the principles of Zero Trust security.
Never Trust, Always Verify
Users and devices are never trusted automatically. Every access request must be authenticated and validated.
Assume Breach
Zero Trust assumes that attackers may already be present inside the network. Security controls are designed to prevent lateral movement.
Enforce Least Privilege
Users only receive the minimum access required to perform their tasks.
Continuous Security Evaluation
Access decisions are not made once. They are continuously evaluated throughout the session.
These principles ensure that the framework enforces security consistently across the environment.
ZTNA Implementation Framework
Implementing ZTNA requires a phased approach rather than a single deployment.
A practical ZTNA implementation framework often follows these stages.
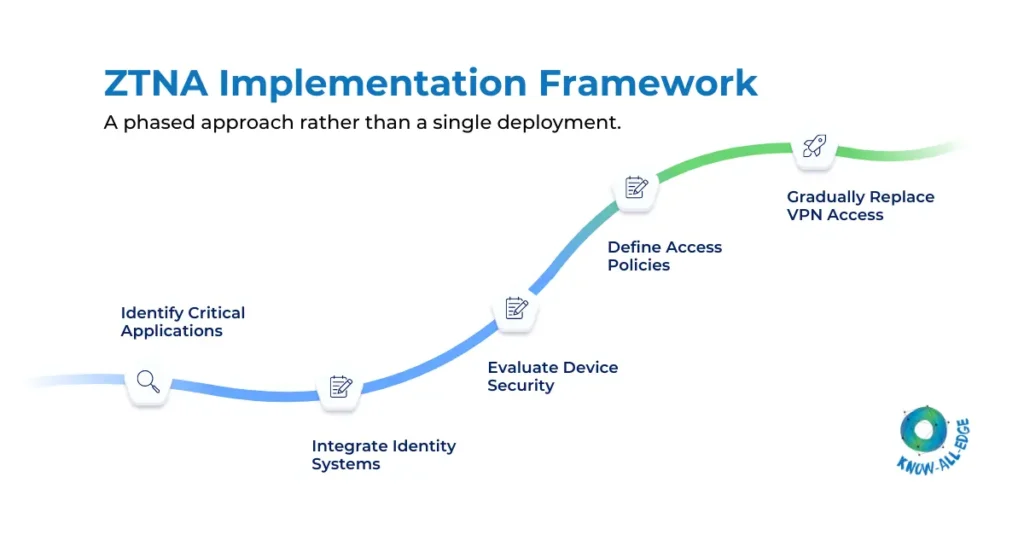
(1) Identify Critical Applications
Begin by identifying applications that contain sensitive data or require strong access controls.
(2) Integrate Identity Systems
Ensure identity providers and authentication mechanisms are integrated with the ZTNA platform.
(3) Evaluate Device Security
Establish policies that verify endpoint compliance before granting access.
(4) Define Access Policies
Create policies that enforce least privilege access based on user roles and application sensitivity.
(5) Gradually Replace VPN Access
Organizations often transition from VPN to ZTNA by securing specific applications first.
Understanding the broader transition from legacy access models can help. Our comparison of ZTNA vs VPN explores how this shift is happening across enterprises.
Conclusion
Adopting Zero Trust is not simply about deploying new security tools. It requires a structured approach to how access decisions are made across the organization.
A well-designed ZTNA framework provides that structure.
By combining identity verification, device trust, least privilege access, and continuous monitoring, organizations can create a secure access model that protects applications without relying on traditional network perimeters.
As hybrid workforces and cloud environments continue to expand, implementing a strong framework will become an essential part of modern cybersecurity strategies.
Ready to implement a Zero Trust framework in your organization?
Building a Zero Trust strategy requires more than deploying new tools. It requires designing the right framework aligned with your identity systems, security policies, and application architecture.
Know All Edge helps enterprises translate Zero Trust principles into practical ZTNA deployments that secure access to applications and services. Speak with our experts to begin your Zero Trust journey.
Frequently Asked Questions
What is the ZTNA framework?
It is the structured approach used to implement Zero Trust Network Access, combining identity verification, device trust, policy enforcement, and continuous monitoring.
How is ZTNA different from traditional remote access?
ZTNA provides application-level access based on identity and device posture, while traditional remote access methods such as VPN grant network-level connectivity.
Why is identity important in the ZTNA framework?
Identity verification ensures that access decisions are tied to the user rather than the network location, which strengthens security in distributed environments.
What are the key steps in implementing a ZTNA framework?
Key steps include identifying critical applications, integrating identity providers, verifying device posture, defining access policies, and gradually replacing legacy access methods.
