One of the most common mistakes organizations make when adopting Zero Trust is assuming that ZTNA is a single tool. ZTNA is not a product, it is a capability delivered through multiple integrated components.
This creates confusion for security teams:
- Do we need multiple tools or one platform?
- How do identity, endpoint security, and access control fit together?
- Are we building a stack or buying a solution?
Understanding the ZTNA tools landscape is critical to avoiding fragmented deployments and tool sprawl.
What are ZTNA Tools?
ZTNA tools are individual technologies that work together to enforce identity-based, policy-driven access to applications. Unlike legacy models where security is enforced at the network perimeter, Zero Trust Network Access relies on multiple layers of control.
These tools collectively:
- Authenticate users
- Validate device security
- Enforce access policies
- Monitor and analyze activity
The key is not just selecting tools but ensuring they work together as a cohesive system.
If you want to understand how these layers interact, our ZTNA framework explains how identity, device trust, and policy enforcement align.
Types of ZTNA Tools
ZTNA environments typically consist of several categories of tools, each responsible for a specific control layer.
Identity-Based Access Tools
Identity is the starting point of Zero Trust. These tools verify who the user is before any access decision is made.
They provide:
- Authentication
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
Without strong identity controls, Zero Trust cannot be enforced effectively.
Device Posture Assessment Tools
A verified user does not automatically mean a secure session. ZTNA requires evaluating the security state of the device.
Device posture tools:
- Check endpoint compliance
- Validate OS updates and patches
- Integrate with EDR/XDR systems
- Detect compromised devices
These tools ensure that access decisions consider device trust not just user identity.
Policy Enforcement Tools
Policy enforcement is where Zero Trust decisions are applied.
These tools:
- Define access rules
- Evaluate risk signals
- Enforce least-privilege access
This layer ensures that users only access what they are authorized to. It is also where organizations often struggle because policy design requires aligning security with business workflows.
Access Broker / ZTNA Platforms
This is the layer most people associate with ZTNA. ZTNA platforms act as secure intermediaries between users and applications.
They:
- Broker access requests
- Hide applications from direct exposure
- Enforce policy decisions
This layer is the execution point of Zero Trust access.
Monitoring & Analytics Tools
ZTNA does not end with access approval. Continuous visibility is critical.
Monitoring tools provide:
- Access logs
- User behavior analytics
- Threat detection signals
Integration with SIEM and XDR platforms allows organizations to:
- Correlate access events
- Detect anomalies
- Respond to threats faster
ZTNA Tools List: Common Tools Used in Zero Trust Environments
When organizations implement Zero Trust, they typically rely on a combination of tools rather than a single product.
A practical ZTNA tools list includes:
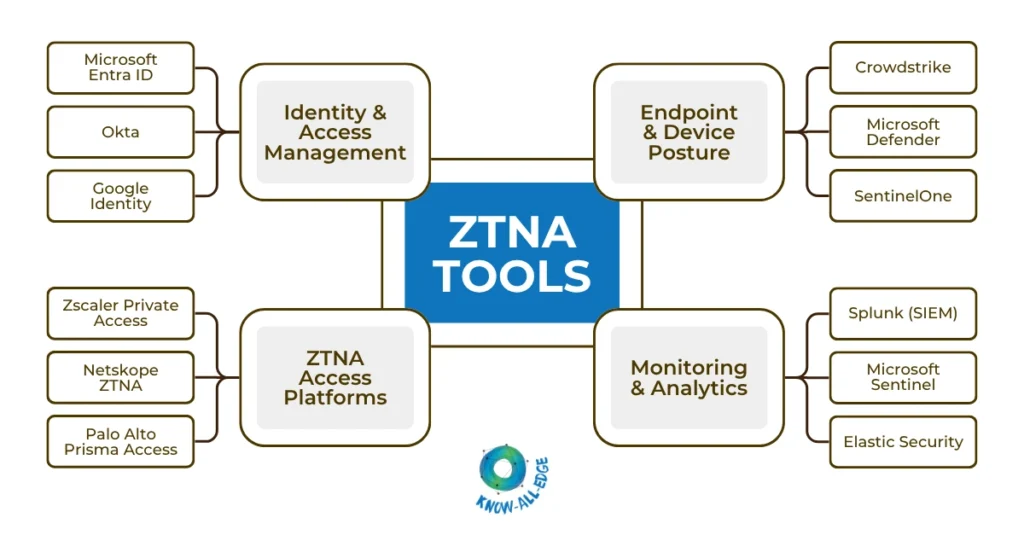
This layered approach ensures that identity, device trust, and access control are enforced consistently.
Choosing the Right ZTNA Tools
The challenge is not identifying tools. It’s avoiding fragmentation. Security leaders should focus on:
- Integration First, Tools Second: Tools must integrate seamlessly across identity, endpoint, and policy layers.
- Avoid Tool Sprawl: More tools do not equal better security.
- Align with Architecture: Tools should support your Zero Trust architecture—not dictate it.
- Platform vs Best-of-Breed: Decide whether to use a unified platform or integrate multiple specialized tools.
Best ZTNA Tools for Enterprise Environments
There is no one-size-fits-all answer to the best ZTNA tools, but certain platforms consistently stand out based on architecture and use case.
(1) Zscaler Private Access
Best for large enterprises with cloud-first architecture and global workforce.
(2) Netskope ZTNA
Best for organizations prioritizing data security and SaaS visibility.
(3) Palo Alto Prisma Access
Best for hybrid environments and organizations with strong network security focus.
(4) Cloudflare Access
Best for cloud-native companies and developer-centric environments.
(5) Cisco Secure Access (Duo + ZTNA)
Best for identity-first security strategies and Cisco-heavy environments.
The “best” tool depends on your architecture, your user base and your existing security stack.
Conclusion
ZTNA is not something you buy, it’s something you build. Organizations that treat ZTNA as a single tool often end up with incomplete implementations. Those that approach it as an integrated system of tools aligned with architecture achieve better security outcomes.
The goal is not to have more tools, but to have the right tools working together effectively. Choosing from the available ZTNA tools list requires focusing on architecture fit rather than simply selecting the most popular or feature-rich platforms.
At Know All Edge we help organizations design and integrate ZTNA tool stacks that work seamlessly across identity, endpoint, and security layers.
Speak with our experts to build a scalable Zero Trust architecture.
Frequently Asked Questions
How do ZTNA tools fit into an existing security stack?
ZTNA tools integrate with identity providers, endpoint security (EDR/XDR), and monitoring platforms like SIEM. Rather than replacing existing tools, they act as an access control layer that connects identity, device trust, and application access policies.
What is the difference between ZTNA tools and ZTNA solutions?
ZTNA tools refer to individual components such as identity systems, device posture tools, and policy engines, while ZTNA solutions are integrated platforms that combine these capabilities into a unified access model.
Should organizations choose a single ZTNA platform or multiple tools?
This depends on architecture. Some organizations prefer unified platforms (like SASE-based solutions) for simplicity, while others adopt best-of-breed tools for flexibility and deeper control across identity, endpoint, and monitoring layers.
What role do endpoint security tools play in ZTNA?
Endpoint tools provide device posture signals such as compliance status, threat detection, and risk levels. ZTNA tools use this data to make dynamic access decisions, ensuring compromised devices cannot access sensitive applications.
How do organizations avoid tool sprawl when implementing ZTNA?
The key is integration. Instead of adding disconnected tools, organizations should align identity, endpoint, and access control systems within a unified architecture or tightly integrated ecosystem.
What challenges arise when integrating multiple tools?
Common challenges include inconsistent policy enforcement, lack of centralized visibility, integration complexity, and increased operational overhead if tools are not properly aligned.
