The Problem with Traditional VPN
For years, VPNs have been the default way organizations provide remote access to internal applications. When employees worked primarily from corporate offices and most applications lived inside the data center, VPN-based access made sense.
But the modern enterprise looks very different.
Today’s environment includes hybrid workforces, SaaS platforms, cloud workloads, contractors, and third-party partners accessing business systems from anywhere. In this model, extending the corporate network to every user device through a VPN introduces significant security risks.
A compromised endpoint connected through VPN can potentially access large portions of the internal network. This is one reason security leaders are re-evaluating whether traditional VPN architectures are still suitable for today’s threat landscape.
This is where the discussion around ZTNA vs VPN becomes relevant. Organizations are increasingly adopting Zero Trust Network Access (ZTNA) as a more secure and scalable approach to remote access.
What is VPN?
A Virtual Private Network (VPN) allows remote users to securely connect to a corporate network over the internet. Once authenticated, the user’s device essentially becomes part of the internal network.
In a traditional VPN model:
- The user authenticates with credentials.
- A secure tunnel is created between the device and the corporate network.
- The user gains network-level access to internal resources.
While encryption protects data in transit, the architecture assumes that once users are inside the network, they are trusted.
This “trust after authentication” model creates a major problem. If an attacker compromises a user’s credentials or endpoint, they may gain access to multiple internal systems through the VPN connection.
For many organizations, this broad network access significantly increases the potential attack surface.
What is ZTNA?
Zero Trust Network Access (ZTNA) is a modern security model that provides application-level access rather than network-level access.
Instead of connecting users to the entire network, ZTNA connects them only to the specific applications they are authorized to use.
Key principles behind ZTNA include:
- Identity-based authentication
- Device posture verification
- Least-privilege access
- Continuous access validation
When a user requests access to an application, the ZTNA platform verifies identity, device health, and access policies before establishing a secure connection.
Unlike VPNs, the internal network is never exposed to the user.
For a deeper understanding of how this model works, read our breakdown of ZTNA architecture.
Key Differences: ZTNA vs VPN
When comparing ZTNA vs VPN, the difference lies primarily in how access is granted and controlled.
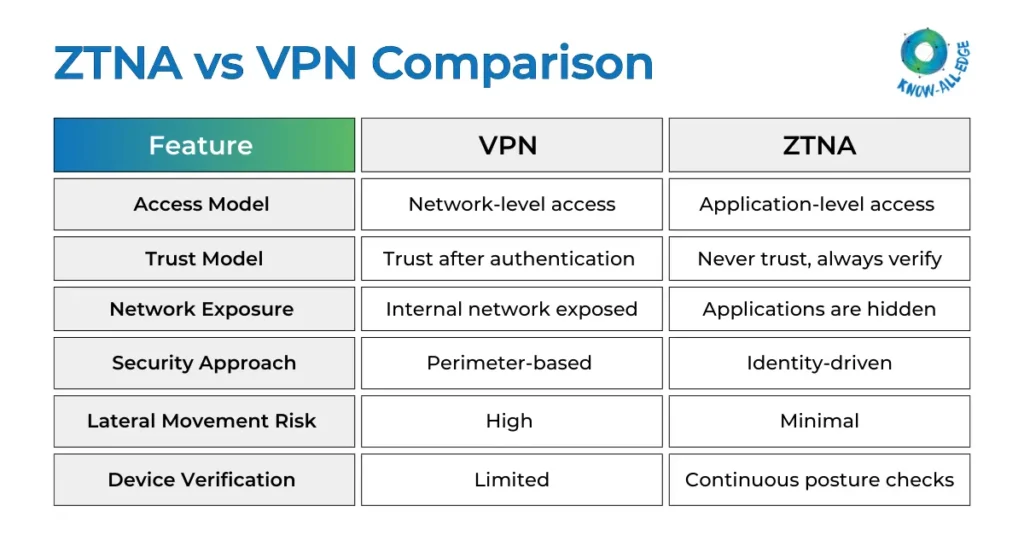
In short, VPNs extend the corporate network outward, while ZTNA keeps the network hidden and brokers secure access to individual applications.
Security Comparison: Does ZTNA Reduce the Attack Surface?
One of the biggest questions security leaders ask is: Is ZTNA actually more secure than VPN?
The key difference lies in the attack surface.
VPN architectures expose the internal network to any authenticated user. If attackers compromise credentials, they may be able to move laterally across systems.
ZTNA reduces this risk by:
- Hiding internal applications from the internet
- Enforcing identity-based access policies
- Restricting users to specific applications
- Continuously verifying device posture
Because users never gain network-level access, attackers have far fewer opportunities to move laterally.
For organizations focused on Zero Trust security models, ZTNA aligns more closely with modern security frameworks.
(1) User Access Experience
Security is important, but usability also matters.
Traditional VPNs often introduce friction for users:
- Manual VPN connections
- Slow performance due to backhauling traffic
- Connectivity issues
- Network congestion during peak usage
ZTNA platforms typically provide a more seamless experience.
Instead of connecting to the corporate network, users simply authenticate and access applications directly through secure gateways. Many solutions also provide agentless access options for third-party users.
This approach often results in faster and more reliable application access for remote users.
(2) Scalability and Cloud Readiness
The rise of SaaS and cloud platforms has further exposed limitations in VPN architectures.
Traditional VPNs were designed primarily for on-premise environments. As organizations adopt multi-cloud infrastructure, routing all traffic through corporate networks becomes inefficient and difficult to scale.
ZTNA platforms are designed with cloud-native environments in mind. Many solutions integrate directly with cloud platforms and identity providers, enabling secure access to SaaS and cloud-hosted applications without requiring network backhauling.
This makes ZTNA particularly attractive for organizations pursuing cloud-first strategies.
Why Organizations Are Moving from VPN to ZTNA
Across industries, security leaders are rethinking remote access strategies. They ask, “Is ZTNA better than VPN?”
Several factors are driving the shift from VPN to ZTNA:
(1) Expanding Attack Surface
VPN-based access exposes internal networks, increasing the risk of lateral movement.
(2) Hybrid Workforce
Remote and distributed teams require secure access without exposing internal infrastructure.
(3) Cloud Adoption
Applications now live across SaaS platforms, public clouds, and hybrid environments.
(4) Zero Trust Security Initiatives
Many organizations are adopting Zero Trust architectures where identity and device posture determine access.
(5) Third-Party Access
ZTNA allows organizations to provide secure access to vendors and partners without exposing internal networks.
Many of these trends align with broader Zero Trust security frameworks and modern access architecture.
When VPN Might Still Be Used
Despite its limitations, VPN is not disappearing overnight.
Many organizations continue to use VPN for specific scenarios:
- Legacy applications that require network-level access
- Administrative access to internal systems
- Environments where Zero Trust architecture has not yet been implemented
- Short-term remote access solutions
In practice, many enterprises operate hybrid models where VPN supports legacy infrastructure while ZTNA secures modern applications. Over time, organizations gradually reduce reliance on VPN as they expand their Zero Trust architecture.
Conclusion
The debate around ZTNA vs VPN ultimately reflects a broader shift in cybersecurity architecture.
VPNs were designed for an era where applications lived inside corporate networks and most users worked within the office perimeter. Today’s environments are far more distributed and dynamic.
ZTNA represents a different approach to secure access: one that focuses on identity, device posture, and application-level connectivity rather than extending network access to remote users.
For many organizations, the transition from VPN to ZTNA is not an immediate replacement but part of a longer journey toward Zero Trust security.
As enterprises modernize their infrastructure and adopt cloud-based applications, ZTNA is increasingly becoming a core component of secure access strategies.
Planning to Replace VPN with a Zero Trust Approach?
Looking to replace legacy VPN with a Zero Trust approach? Know All Edge helps enterprises transition from traditional VPN to secure ZTNA solutions that enable application-level access and stronger identity verification. Connect with our team to evaluate the right Zero Trust architecture.
Frequently Asked Questions ZTNA vs VPN
Is ZTNA actually more secure than VPN?
In most cases, ZTNA offers stronger security because it limits users to application-level access rather than granting network-level access. This significantly reduces the risk of lateral movement if a device or credential is compromised.
Can ZTNA replace VPN for enterprise remote access?
Many organizations are replacing VPN with ZTNA for application access. However, VPN may still be required for certain legacy systems or administrative network access depending on infrastructure design.
Does ZTNA reduce the attack surface compared to VPN?
Yes. ZTNA hides internal applications behind identity-aware access brokers, meaning they are not directly exposed to the internet or accessible through network connections.
How do organizations migrate users from VPN to ZTNA?
Migration typically happens in phases. Organizations start by securing specific applications with ZTNA while continuing to use VPN for legacy workloads. Over time, more applications are moved to the Zero Trust model.
What breaks when moving from VPN to ZTNA?
Applications that rely on network-level connectivity or legacy protocols may require architecture changes. Organizations often need to modernize application access patterns before fully replacing VPN.
Is ZTNA only for remote users?
No. ZTNA can secure access for both remote and internal users by enforcing identity-based access policies regardless of where the user is connected from.
