Zero Trust Network Access (ZTNA) has become a critical component of modern secure access strategies. As organizations move away from VPN-based architectures, ZTNA provides a more secure approach by enforcing identity-based access to applications rather than exposing the entire network.
However, as adoption grows, many security leaders are discovering an important distinction: not all ZTNA architectures are built the same.
Early ZTNA implementations (often referred to as traditional ZTNA) focused primarily on securing access to specific applications. While this model improved security compared to VPNs, it still left gaps when organizations needed to secure broader network traffic, unmanaged devices, and complex hybrid environments.
This is where the conversation around Traditional ZTNA vs Universal ZTNA becomes relevant. Universal ZTNA expands the Zero Trust model to provide consistent security across applications, networks, users, and devices.
What is Traditional ZTNA?
Traditional ZTNA was designed primarily to replace VPN-based access for internal applications.
Instead of granting users network-level access, traditional ZTNA brokers a secure connection between the user and a specific application. Access is typically granted after verifying identity and enforcing policy-based controls.
In a typical traditional ZTNA model:
- Users authenticate through an identity provider
- The ZTNA broker validates identity and access policy
- The user receives access only to specific applications
- Internal networks remain hidden from the user
This architecture significantly improves security compared to VPNs because users are never directly connected to the internal network.
For a deeper look at how secure access models evolved, see our comparison of ZTNA vs VPN.
Limitations of Traditional ZTNA
While traditional ZTNA is a major improvement over VPN-based remote access, organizations often encounter limitations as their environments become more complex.
Application-Focused Access
Traditional ZTNA primarily protects web-based applications, which means it may not secure all types of network traffic.
This can leave gaps when organizations need to secure:
- Non-web applications
- Legacy protocols
- Full network connectivity for certain workloads
Limited Coverage for Managed Devices
Many traditional ZTNA deployments rely on endpoint agents or browser-based access, which may not cover unmanaged devices or certain remote environments effectively.
Fragmented Security Controls
In some implementations, ZTNA only covers specific applications while other security tools handle network access, device posture checks, and traffic inspection. This fragmented approach can create operational complexity.
Incomplete Zero Trust Enforcement
Traditional ZTNA secures access to applications but may not enforce consistent Zero Trust policies across all users, devices, and network traffic.
As organizations scale Zero Trust architectures, these limitations often lead them to explore Universal ZTNA.
What is Universal ZTNA?
Universal ZTNA extends the Zero Trust model beyond application access to secure all user-to-resource connections, regardless of device type, location, or application protocol.
Unlike traditional ZTNA, which typically focuses on application-level access, Universal ZTNA applies Zero Trust policies across:
- SaaS applications
- On-premise applications
- Private cloud environments
- Internal network services
- Managed and unmanaged devices
In Universal ZTNA architecture, every connection is continuously verified based on identity, device posture, context, and access policies.
This allows organizations to apply consistent Zero Trust enforcement across the entire environment rather than protecting only specific applications.
To understand how this fits into the overall design, explore how modern ZTNA architecture supports identity-driven security.
Key Differences Between Traditional ZTNA and Universal ZTNA
When comparing Traditional ZTNA vs Universal ZTNA, the primary difference lies in the scope of security enforcement.
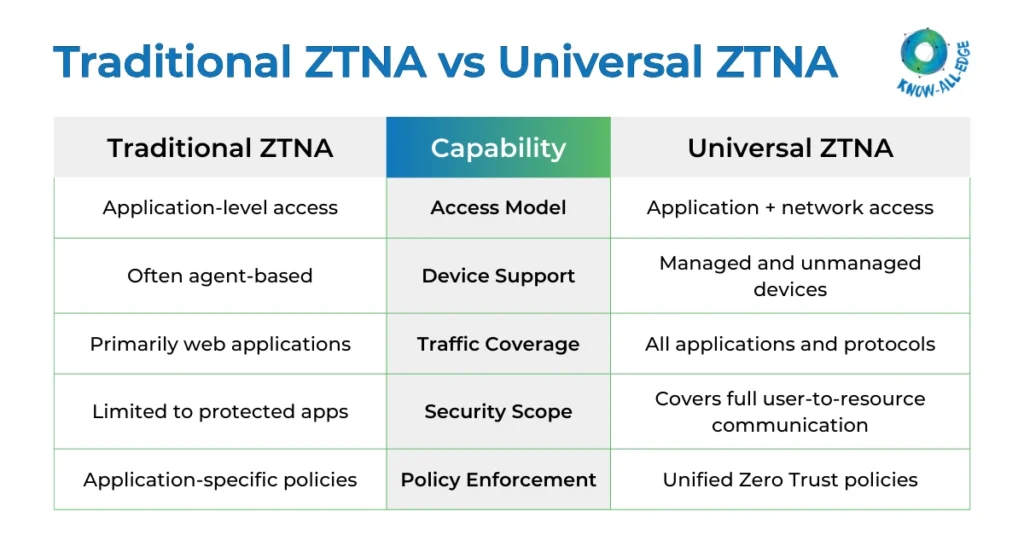
In short, traditional ZTNA protects access to applications, while Universal ZTNA enforces Zero Trust across the entire access layer.
Why Universal ZTNA is Emerging
As enterprise environments become more distributed, organizations are recognizing that securing individual applications is only part of the challenge.
Several factors are driving the emergence of Universal ZTNA.
Hybrid Workforce
Employees, contractors, and partners access applications from multiple devices and networks. Security models must enforce policies regardless of user location.
SaaS and Multi-Cloud Environments
Applications now live across multiple cloud platforms. Universal ZTNA allows organizations to apply consistent access policies across these environments.
Unmanaged Devices
Traditional ZTNA may struggle to secure unmanaged endpoints, whereas Universal ZTNA can apply security controls even for device-agnostic access scenarios.
Security Consolidation
Many organizations are moving toward unified security platforms where Zero Trust access, network inspection, and policy enforcement operate together.
Conclusion
As organizations adopt Zero Trust architectures, the conversation around Traditional ZTNA vs Universal ZTNA highlights an important shift in how secure access is implemented.
Traditional ZTNA introduced the concept of application-level access and significantly improved security compared to VPN-based models. However, modern enterprise environments require broader protection that covers users, devices, and applications across hybrid infrastructures.
Universal ZTNA expands the Zero Trust model to address these challenges by enforcing consistent policies across all connections.
For many organizations, this represents the next stage in the evolution of secure access architectures.
Evaluating the shift from traditional to Universal ZTNA?
Know All Edge helps organizations design scalable Zero Trust architectures that secure access for both managed and unmanaged devices. Talk to our experts to explore Universal ZTNA solutions tailored to your environment.
Frequently Asked Questions
What is the difference between ZTNA and Universal ZTNA?
Traditional ZTNA focuses on providing secure access to specific applications, while Universal ZTNA extends Zero Trust principles to all user-to-resource connections, including network services and multiple device types.
Is Universal ZTNA replacing traditional ZTNA?
In many cases, Universal ZTNA builds on the foundation of traditional ZTNA. Instead of replacing it entirely, it expands the scope of Zero Trust enforcement across more environments and connection types.
Can Universal ZTNA secure unmanaged devices?
Yes. Many Universal ZTNA platforms can enforce identity-based policies even for unmanaged or contractor devices while still limiting access to authorized applications.
Does Universal ZTNA eliminate the need for VPN?
In many environments, Universal ZTNA can replace VPN for application access. However, some legacy use cases may still require VPN connectivity depending on infrastructure design.
Is Universal ZTNA part of SASE architecture?
Yes. Many Universal ZTNA solutions are integrated into broader Secure Access Service Edge (SASE) platforms that combine networking and security capabilities.
How does Universal ZTNA support Zero Trust architecture?
Universal ZTNA enforces continuous verification of identity, device posture, and context before granting access to resources, which aligns closely with Zero Trust security principles.
