India’s data protection landscape changed in August 2023 with the Digital Personal Data Protection (DPDP) Act, creating a clear framework for handling personal data.
For CISOs, compliance heads, and data governance teams, the focus now is simple: how to comply, and how quickly.
The biggest challenge is not legal or technical. It is data visibility.
- Before taking consent
- Before setting retention limits
- Before handling user requests
- Before reporting breaches
You need to know where your personal data exists across cloud systems, SaaS apps, databases, shared drives, and even legacy systems.
Most organizations lack this visibility. Without it, compliance is not possible.
This is where Data Security Posture Management (DSPM) helps by giving that visibility and control. Understanding what DSPM is and how it operates is the starting point for any serious DPDP compliance program.
This blog explains what the DPDP Act requires, why compliance is harder than it seems, and how DSPM for DPDPA helps.
What Is India’s Digital Personal Data Protection (DPDP) Act?
The DPDP Act governs how digital personal data is handled in India. It applies to any entity that collects, stores, processes, or uses personal data of people in India. This includes companies based outside India, as long as they are offering goods or services to individuals in India.
The Act defines two main types of responsibility holders:
- Data Fiduciaries: These are entities that decide why and how personal data is processed. Most businesses fall into this category, including banks, hospitals, e-commerce platforms, IT firms, and manufacturers. They act as Data Fiduciaries for their customers, employees, and partners.
- Data Processors: These entities process personal data on behalf of a Data Fiduciary. Examples include cloud service providers, BPOs, and managed service providers.
The Act also introduces Significant Data Fiduciaries (SDFs). These are organizations identified by the government as handling large amounts of sensitive personal data or engaging in high-risk data processing.
- SDFs have stricter responsibilities
- They must appoint a Data Protection Officer
- They must conduct Data Protection Impact Assessments (DPIAs)
As of 2025, the detailed rules under the Act are still being finalized. However, the main requirements are already clear, so it is wise for organizations to start preparing for compliance instead of waiting for enforcement.
Core Obligations Under the DPDP Act
Lawful Purpose and Consent
Personal data can be processed only for a lawful purpose and with the data principal’s consent. This consent must be free, specific, informed, unconditional, and unambiguous.
- Organizations must clearly show why each piece of data was collected
- They must also prove that valid consent was taken for that exact purpose
This means it is not enough to just have data. You need to know what it is, who it belongs to, and why you are keeping it.
Data Minimization
Organizations can collect only the personal data that is necessary for a defined purpose. Collecting data just in case it may be useful later is not allowed.
- Old or unused data collected over time becomes a risk
- Poorly managed legacy data turns into a liability
Storage Limitation and Retention
Personal data cannot be kept forever. It must be deleted once the purpose is fulfilled.
- Organizations must track what data they have
- When it was collected
- Why it was collected
- Whether that purpose still exists
Without an updated data inventory, managing this at scale becomes very difficult.
Data Accuracy
Data Fiduciaries must take reasonable steps to keep personal data accurate and complete. This is important for customer and employee records. Data is often duplicated, outdated, or inconsistent across systems.
Security Safeguards (Section 8)
Section 8 requires reasonable security safeguards to prevent data breaches. While specific controls are not listed, this usually includes encryption, access controls, monitoring, and proper security practices. This is not a one-time task. Security must be monitored continuously.
DSPM supports this by continuously tracking the security posture of personal data.
Data Principal Rights
Individuals have the right to:
- Access their personal data
- Correct inaccurate data
- Request erasure
- Raise grievances
Organizations must respond to these requests within set timelines. To handle a request, all data related to a person must be found quickly. This includes data across cloud, SaaS, on-premises systems, backups, and archives
Without a searchable data inventory, this becomes slow and error-prone.
Breach Notification
In case of a data breach, organizations must inform both the Data Protection Board and affected individuals. The timeline is expected to be strict.
- Organizations must quickly identify what data was affected
- How sensitive it was
- Which individuals were impacted
Without proper data classification and inventory, this is hard to do under pressure.
The Compliance Challenge: Why It Is Harder Than It Looks
At first glance, the obligations above can feel like a simple checklist. You set up consent mechanisms, define retention policies, build a DSAR process, and prepare breach notification steps.
But all of this depends on one basic thing: you need to know where your personal data actually is. That is where most organizations struggle.
Take a typical mid-sized Indian company. Personal data is spread across many systems like CRM, ERP, HR tools, finance platforms, customer support systems, and email archives. It is also stored in shared SharePoint folders where sales teams keep proposals, in Excel files used for reporting, in data lakes built by analytics teams, and even in old backups from systems that were shut down years ago but never fully cleaned.
All these places may contain personal data. Some are tracked and managed, but many are not. Still, compliance rules apply to all of them.
Trying to find and track this data manually using interviews, spreadsheets, and documentation does not work well at scale. It is slow, often incomplete, and quickly becomes outdated, especially in cloud environments where new data sources keep appearing.
This is where DSPM helps. It automates data discovery and gives ongoing visibility into what personal data exists, where it is stored, how sensitive it is, and who can access it.
How DSPM Directly Addresses DPDP Requirements
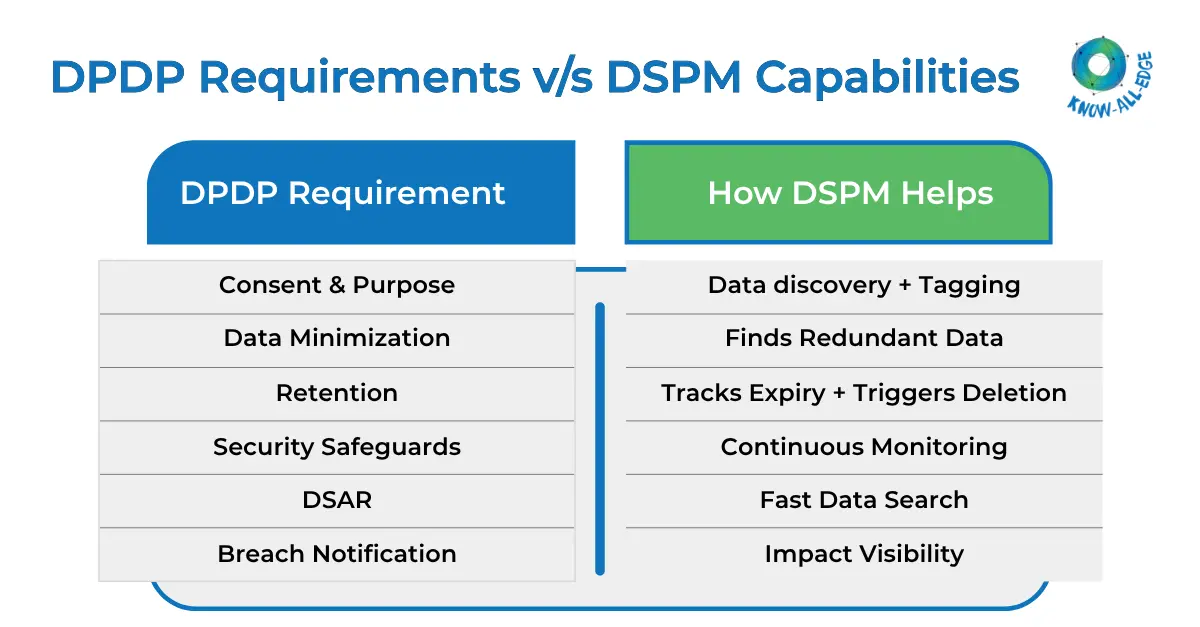
The components of a DSPM solution line up closely with DPDP requirements, which makes it a core part of any serious compliance program.
- For consent and lawful purpose, you first need to know what personal data you have and why it was collected. DSPM’s data discovery engine finds all personal data across your systems. It can also classify and tag data by type, like customer PII, employee data, or payment data, and link it to the system it came from. This helps legal and compliance teams check that proper purpose documentation exists.
- Data minimization means you should not keep data you don’t need. DSPM helps by finding redundant, obsolete, and trivial data, such as duplicate records, old datasets, or forgotten test environments that still contain real personal data, so they can be cleaned up.
- Storage limitation requires you to manage how long data is kept. DSPM tracks personal data that has passed its retention period and connects with workflows to trigger deletion or anonymization.
- Security safeguards are easier to prove with continuous DSPM monitoring. Instead of just saying controls exist, DSPM keeps a live record of the security status of personal data, including encryption, access rights, and exposure risks. This acts as audit-ready evidence for compliance with Section 8.
- DSAR requests can be handled much faster. When someone asks to access or delete their data, DSPM searches for the full data inventory and shows where their data exists, how it is used, and what systems hold it.
- Breach response also improves. If a breach happens, DSPM quickly shows what data was affected, how sensitive it was, and which individuals are impacted, helping you send accurate notifications on time.
Building a DPDP Compliance Program with DSPM
Here is how DSPM for DPDPA is applied in a structured approach, aligned with broader DSPM best practices for data protection:
Phase 1: Personal Data Discovery
Start by deploying DSPM across all your data environments, whether cloud, SaaS, on-premises, or hybrid. This helps you build a complete inventory of personal data. Focus first on areas that are most likely to store regulated data, like customer systems, HR platforms, and financial applications.
Phase 2: Classification by Sensitivity and Category
Next, apply classification policies to tag personal data based on its category under the DPDP Act, its sensitivity, and why it was collected. At this stage, also flag any data that does not have a clear purpose or missing consent records.
Phase 3: Data Flow Mapping
Use DSPM to map how personal data moves across your systems, between regions, and to third parties. Tracking cross-border data transfers is especially important due to DPDP Act requirements on international data movement.
Phase 4: Access Governance and Consent Alignment
Review who has access to personal data using DSPM’s entitlement analysis. Identify excessive permissions, outdated access, and any third-party access that is not backed by a valid Data Processing Agreement.
Phase 5: Continuous Monitoring and Compliance Evidence
Set up continuous monitoring to catch changes in real time, such as new data stores, access updates, or encryption gaps. Use automated reports to create clear compliance evidence for internal checks and regulatory audits.
DSPM for Significant Data Fiduciaries
Organizations classified as Significant Data Fiduciaries have extra responsibilities under the DPDP Act, like conducting DPIAs for high-risk processing and appointing a Data Protection Officer.
DSPM helps with both. For DPIAs, it provides a reliable data inventory and risk insights needed to assess how processing activities impact individual rights. It shows what data is involved, how it flows, who can access it, and what controls exist. Without an updated data inventory, DPIAs become guesswork instead of evidence-based assessments.
For Data Protection Officers, DSPM offers clear visibility into the data environment. It acts as a single source of truth for the organization’s data posture, continuously updated and easy to use for reporting and governance.
What Happens If You Don’t Comply?
The DPDP Act sets strict penalties, with fines up to INR 250 crore per violation for issues like weak security safeguards or mishandling child data. The Data Protection Board of India can investigate complaints, run inquiries, and impose these penalties.
But the real cost goes beyond fines. A personal data breach can damage reputation in ways that are hard to measure and even harder to fix. For BFSI institutions, this risk is higher due to additional expectations from RBI and SEBI.
The cost of non-compliance is not just the penalty. It includes investigations, remediation, customer notifications, reputational damage, and internal disruption. Organizations that already have DSPM for DPDPA in place are far better prepared than those that do not.
DPDP Act vs. GDPR: What Indian Enterprises with Global Operations Need to Know
Many Indian companies, especially in IT services, BFSI, and pharmaceuticals, also handle data of European residents. This means they must comply with the EU’s GDPR as well.
The good news is that DSPM built for DPDP compliance largely supports GDPR too. Both require data discovery, data inventory, classification, access governance, breach notification, and proof of security controls.
There are some differences. GDPR allows multiple lawful bases for processing, while DPDP focuses more on consent. GDPR also differs in scope and regulatory structure. But the core data governance requirements are similar.
This means a DSPM program for DPDP is not limited to one regulation. It becomes a strong data governance foundation that supports multiple frameworks and reduces overall compliance effort across global operations.
Conclusion
The DPDP Act makes it clear that organizations must handle personal data responsibly, secure it properly, and stay accountable at all times. The requirements are defined, the penalties are significant, and enforcement is getting closer.
You cannot meet these requirements without knowing where your personal data is. And you cannot do that across every cloud, system, and data store without automated and continuous data discovery and classification.
That is where DSPM comes in. It is not just a compliance checkbox, but the foundation for a strong, audit-ready, and effective DPDP compliance program.
Know All Edge helps Indian enterprises build DSPM programs from the ground up, covering everything from data discovery to continuous monitoring and compliance reporting. Speak to our team to book a DPDP readiness assessment.
Frequently Asked Questions
How does DSPM help with DPDP compliance?
DSPM helps by discovering where personal data exists, classifying it, tracking its flow, and monitoring access, making it easier to meet DPDP requirements.
How quickly can organizations implement DSPM for DPDPA?
Implementation timelines vary, but many organizations can start seeing visibility into their data within a few weeks. A phased approach is usually followed, beginning with high-risk systems and expanding coverage over time.
How does DSPM support audit readiness?
DSPM creates a continuously updated record of data location, classification, access controls, and security posture. This serves as audit-ready evidence, reducing the effort required to demonstrate compliance during regulatory checks.
