Introduction
With technology advancements, data is now scattered across cloud platforms, SaaS tools, analytics pipelines, and now AI systems. That shift requires to take security to the next level. Traditional security approaches still focus heavily on infrastructure, but attackers are going straight for the data itself.
This can create difficult problems. You may have strong perimeter controls, yet still lack clear visibility into where sensitive data is present, who can access it, and how it moves across systems. That gap is exactly where most modern breaches happen.
And it’s worth noting that these breaches can cost your organization millions!
This is where you need data security posture management. It thinks in a different way about protecting data in really complex environments. In this complete guide, we will be discussing in detail about what is DSPM, how it works, and why it is quickly becoming a core part of enterprise security strategy.
Let’s begin.
What is Data Security Posture Management?
Data Security Posture Management, is a framework and set of tools that continuously discover, classify, monitor, and protect sensitive data across an organization’s entire ecosystem.
In simple terms, it tells you the trickiest data information that most organizations struggle with:
- Where your sensitive data located
- What type of data is it
- Who has access to it
- Is it exposed or at risk
Instead of focusing only on systems or networks, DSPM puts data at the center of security decisions. That shift sounds small, but it changes everything about how risks are identified and managed.
How it differs from traditional security approaches
Traditional security models were designed for a very different environment. They only used to protect the data under certain set boundaries, like data centers or controlled networks. But now, data being used outside these boundaries, hackers can easily reach there if you continue using traditional security approaches.
In modern world of data, here’s how data security posture management stands apart:
- Infrastructure vs data focus
Older tools secure servers, endpoints, and networks. DSPM focuses directly on the data layer. - Static vs continuous visibility
Traditional audits give periodic snapshots. DSPM provides ongoing, real-time visibility into data risks. - Manual vs automated insights
Legacy processes depend heavily on manual classification and audits. DSPM automates discovery and risk analysis at scale. - Perimeter thinking vs distributed reality
With SaaS and cloud adoption, data moves constantly. DSPM is built for that fluid environment.
In simple terms, it flags risks before they turn into incidents.
The Growing Importance of DSPM
Here are the key reasons why Data Security Posture Management is becoming critical for organizations today:
Explosion of sensitive data across cloud, SaaS, and AI systems
Organizations are generating and storing more data than ever before. Cloud platforms, collaboration tools, and AI pipelines are accelerating this growth at a pace that most security teams cannot manually track.
A recent industry estimate suggests that over 80% of enterprise data is unstructured, which makes it significantly harder to discover and secure using traditional methods. That includes documents, emails, chat logs, and AI training datasets.
This is exactly the type of data DSPM is designed to handle. It does not rely on predefined structures; it scans and understands data in context.
Rise of regulatory pressure and compliance burden
Regulatory expectations are tightening across the globe, and India is no exception. Frameworks and laws are becoming more specific about how sensitive data should be handled, monitored, and reported.
Organizations today must deal with:
- Global regulations like GDPR and PCI requirements
- Industry-specific mandates in finance and healthcare
- India-specific frameworks such as DPDP Act and RBI guidelines
Compliance is no longer a once-a-year activity. It requires continuous visibility and evidence, which is difficult without automation. Data security posture management plays a key role here by maintaining an always-on view of regulated data and its exposure.
Read in detail: How DSPM helps maintain DPDPA compliance.
Increase in data breaches and insider risks
Data breaches are no longer limited to external attacks. Insider risks, whether accidental or intentional, are growing rapidly. Misconfigured storage, excessive access permissions, and shadow datasets are common causes.
Many reports in 2025 indicated that a significant portion of breaches involved internal access misuse or configuration errors, not sophisticated hacking techniques. That is a critical insight.
DSPM helps identify these issues early by:
- Highlighting over-permissioned users
- Detecting exposed datasets
- Tracking unusual data access patterns
It gives security teams the context they need to act before damage occurs.
Shift from infrastructure-centric to data-centric security
The biggest change is philosophical. Security is no longer about protecting systems first and assuming data is safe within them. That assumption breaks in cloud-first environments.
Instead, organizations are moving toward a data-first model where:
- Data is continuously tracked regardless of location
- Access is tightly controlled and monitored
- Risk is evaluated based on data sensitivity, not just system exposure
DSPM is at the center of this shift. It aligns security efforts with what actually matters most, the data itself.
How Data Security Posture Management Works?

To really understand data security posture management, you need to look at how it operates day to day. DSPM is not a one-time scan or audit, it is a continuous lifecycle that keeps running in the background. DSPM is not a one-time scan or audit; it is a continuous lifecycle made up of key DSPM components that keep running in the background.
Think of it as a loop. Data is discovered, understood, analyzed for risk, and then protected, all while being constantly monitored. Each stage builds on the previous one.
1. Discover
The first step is visibility. You cannot secure what you cannot see, and most organizations underestimate how much unknown data they actually have.
DSPM tools scan across environments to identify both structured and unstructured data, including:
- Databases and data warehouses
- Cloud storage buckets
- SaaS applications
- File systems and collaboration tools
It also uncovers shadow data, which refers to datasets that exist outside formal governance processes. These are often the highest-risk assets because they are unmanaged and frequently exposed.
2. Classify
Once data is discovered, the next step is to understand what it actually is. Not all data carries the same level of risk.
DSPM classifies data into categories such as:
- Personally identifiable information (PII)
- Financial records
- Health data
- Intellectual property
Modern DSPM systems go beyond simple tagging. They use context-aware classification, meaning they consider how data is used, where it is stored, and who interacts with it. This reduces noise and improves accuracy.
3. Map & Analyze
At this stage, DSPM builds a deeper understanding of how data flows through the organization. This is where things become more strategic.
It maps:
- Data lineage, where the data originates and how it evolves
- Data flows between systems, teams, and third-party tools
- Dependencies across applications and platforms
For example, if a dataset is exposed, where else could that data have traveled, and what systems might be affected.
4. Assess Risk
With full context in place, DSPM evaluates risk. This is not just about identifying vulnerabilities, it is about prioritizing what actually matters.
Key risk factors include:
- Misconfigured storage or public exposure
- Excessive or unnecessary access permissions
- Sensitive data stored in insecure locations
DSPM assigns risk scores based on sensitivity, exposure level, and potential business impact. This allows security teams to focus on high-impact issues instead of chasing low-priority alerts.
5. Remediate
Identifying risks is only useful if you can act on them. DSPM enables both automated and manual remediation workflows.
Common actions include:
- Restricting or revoking access permissions
- Applying encryption or masking policies
- Fixing misconfigurations in cloud storage
Automation plays a big role here. Instead of waiting for manual intervention, certain issues can be resolved instantly based on predefined policies.
6. Monitor Continuously
The lifecycle does not end after remediation. Data environments are dynamic, new risks appear constantly as systems change and data moves.
DSPM continuously monitors for:
- Real-time anomalies in data access
- Behavioral patterns that indicate insider threats
- New data exposures or policy violations
This continuous monitoring ensures that security posture does not degrade over time. It also provides ongoing visibility for compliance and audit purposes.
Key Capabilities of Data Security Posture Management
While the lifecycle explains how DSPM works, the capabilities define what it actually delivers to your organization. These are the functions that matter most when evaluating a solution.
Data discovery and classification engines
At the core of any DSPM solution is its ability to discover and classify data accurately. Without this, everything else falls apart.
Strong DSPM platforms can:
- Scan across multi-cloud and hybrid environments
- Identify structured and unstructured data at scale
- Apply intelligent classification with minimal manual input
Accuracy is critical here. Poor classification leads to false positives, which quickly reduce trust in the system.
Risk detection and prioritization
DSPM does not just list issues, it helps you understand which ones actually need attention first.
It evaluates risk based on multiple factors such as:
- Data sensitivity
- Exposure level
- Access patterns
- Business impact
This prioritization is essential for large enterprises where thousands of potential issues can exist at any given time.
Policy enforcement and access governance
Another key capability is enforcing security policies directly at the data level.
This includes:
- Implementing least-privilege access controls
- Continuously validating user permissions
- Automatically adjusting access based on risk
Instead of relying on static roles, DSPM enables dynamic access governance that adapts to real-world usage.
Integrations with cloud, SaaS, and data platforms
DSPM does not operate in isolation. It integrates with the broader technology stack to provide complete coverage.
Typical integrations include:
- Cloud providers like AWS, Azure, and GCP
- SaaS platforms such as CRM and collaboration tools
- Data platforms like Snowflake, BigQuery, and data lakes
These integrations allow DSPM to maintain visibility across all environments where data exists.
Visualization and reporting dashboards
Finally, DSPM provides dashboards that translate complex data risks into clear insights for leadership teams.
Effective dashboards help with:
- Understanding overall data security posture
- Tracking risk trends over time
- Generating reports for audits and compliance
This visibility is crucial for security individuals. It bridges the gap between technical risk and business impact, making it easier to drive informed decisions.
Data Security Posture Management Use Cases
Understanding DSPM conceptually is useful, but its real value shows up in day-to-day operations. These DSPM use cases highlight how data security posture management reduces risk and improves control in real environments.
Sensitive data exposure detection
One of the most immediate benefits of DSPM security is identifying exposed data before it becomes a breach.
This includes:
- Publicly accessible cloud storage containing sensitive files
- Misconfigured databases, which happens more often than teams admit
- Forgotten backups or datasets sitting outside governance
Instead of relying on periodic audits, DSPM continuously scans and flags exposures in real time. That speed often makes the difference between a fix and an incident.
Data access governance
Access is one of the biggest hidden risks in any organization. Over time, permissions accumulate, and very few teams actively clean them up.
DSPM helps by:
- Identifying users with excessive or unnecessary access
- Highlighting dormant accounts with sensitive permissions
- Enforcing least-privilege policies across systems
Insider threat detection
Not all threats come from outside. In fact, many incidents involve internal users, sometimes unintentionally.
DSPM detects unusual patterns such as:
- Large data downloads outside normal behavior
- Access to datasets unrelated to a user’s role
- Sudden spikes in data movement across systems
These signals help teams respond early, instead of reacting after damage is already done.
Compliance monitoring and audit readiness
Compliance has shifted from static reporting to continuous validation. Auditors increasingly expect proof that controls are working at all times.
DSPM supports this by:
- Continuously tracking regulated data
- Detecting violations in real time
- Generating audit-ready reports with minimal manual effort
This significantly reduces the operational burden on security and compliance teams.
Cloud and SaaS data security
Modern enterprises rely heavily on SaaS platforms and multi-cloud environments. Each of these introduces its own risks and visibility challenges.
DSPM provides a unified view across:
- Cloud storage and compute environments
- SaaS applications handling sensitive data
- Third-party integrations and data flows
Without this layer, security teams are often working with fragmented insights.
M&A and data due diligence
During mergers or acquisitions, understanding data risk becomes a high-priority task. However, most organizations lack a clear picture of what data they actually hold.
DSPM helps accelerate due diligence by:
- Discovering sensitive data across the acquired environment
- Identifying compliance gaps and exposures
- Providing a clear risk posture within a short timeframe
This reduces uncertainty and helps leadership make informed decisions faster.
AI and ML data protection
AI adoption is introducing new categories of risk, especially around training data and model inputs.
DSPM in AI helps in:
- Protecting sensitive datasets used for training models
- Monitoring data exposure in AI pipelines
- Preventing leakage of regulated data through AI systems
As AI usage grows, this use case is becoming less optional and more foundational.
How DSPM Secures Data Across Industries
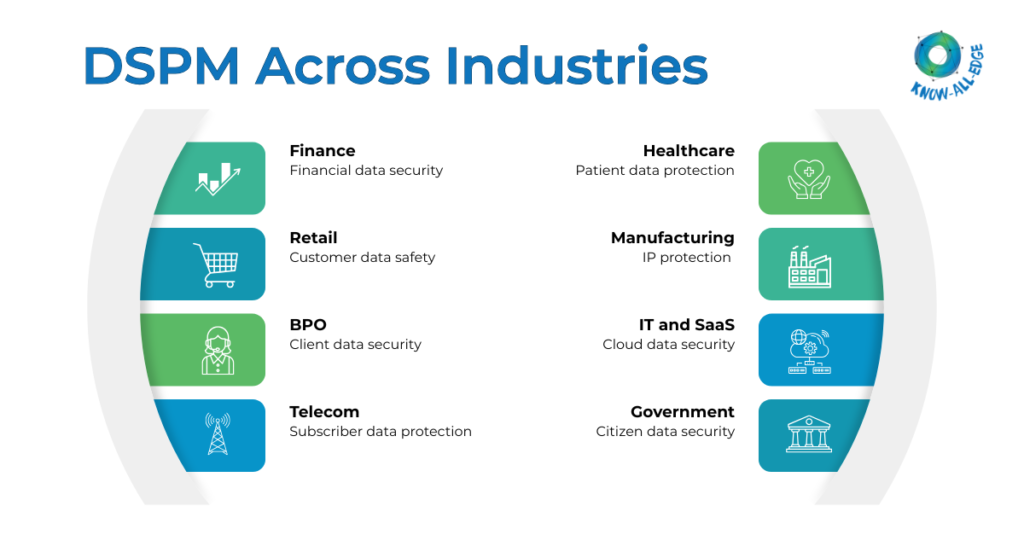
While DSPM is broadly applicable, its impact varies slightly across industries based on the type of data and regulatory pressure involved.
Finance and fintech
Financial institutions deal with highly sensitive data, including transaction records, customer identities, and payment details.
DSPM helps by:
- Securing financial and transactional data across systems
- Monitoring access to high-value datasets
- Supporting compliance with strict regulatory frameworks
Given the risk profile, even small gaps in visibility can have significant consequences.
Healthcare
Healthcare organizations manage some of the most sensitive data categories, including patient records and diagnostic information.
DSPM enables:
- Protection of electronic health records
- Detection of unauthorized access to patient data
- Continuous compliance with healthcare regulations
In this sector, data exposure is not just a financial risk, it directly impacts patient trust and safety.
Retail and e-commerce
Retailers handle large volumes of customer data, payment information, and behavioral insights. Much of this data is spread across platforms and partners.
DSPM helps organizations:
- Track customer data across multiple systems
- Identify exposed payment or personal information
- Secure integrations with third-party vendors
This becomes especially important during peak seasons when data activity spikes.
Manufacturing
Manufacturing firms increasingly rely on digital systems and connected environments. Along with operational data, they also manage valuable intellectual property.
DSPM supports:
- Protection of design files and proprietary data
- Monitoring data flows across supply chains
- Reducing exposure risks in hybrid IT environments
For many manufacturers, protecting IP is just as critical as securing operational systems.
BPO and data-driven enterprises
Business process outsourcing firms and data-driven organizations handle large volumes of client data, often across geographies.
DSPM helps by:
- Ensuring client data is properly isolated and protected
- Monitoring access across distributed teams
- Supporting compliance with multiple regulatory frameworks
In these environments, even a small lapse can impact multiple clients at once.
DSPM for Compliance & Regulations
Compliance has become a continuous function, not a periodic checklist. For most people, the challenge is not understanding regulations; it is maintaining consistent control over data in dynamic environments. This is where data security posture management plays a practical role.
Key Regulations (Global and India)
Organizations today operate under a mix of global standards and region-specific mandates. The complexity increases when data flows across borders and platforms.
Some of the most relevant frameworks include:
- GDPR, HIPAA, and PCI-DSS for global operations
- ISO 27001 and SOC 2 for security and governance standards
- India-specific regulations such as DPDP Act, RBI guidelines, SEBI CSCRF, IRDAI, and CERT-In requirements
Each of these frameworks expects clear visibility into sensitive data, strict access control, and the ability to demonstrate compliance at any time. That is easier said than done without automation.
How DSPM Enables Compliance
DSPM does not replace compliance frameworks, it makes them achievable at scale. Instead of preparing for audits manually, organizations can maintain an always-ready posture.
Here is how DSPM security supports compliance in real environments:
- Continuous discovery of regulated data
DSPM constantly identifies where regulated data resides, even as it moves across systems. This eliminates blind spots that often lead to violations. - Detection of misconfigured and exposed data stores
Misconfigurations are one of the most common causes of compliance failures. It flags these issues early, before they escalate. - Risk prioritization aligned with regulations
Not all risks carry the same compliance impact. It helps prioritize issues based on regulatory sensitivity and business context. - Real-time monitoring and alerts
Instead of discovering issues during audits, teams receive immediate alerts when policy violations occur. - Access governance and least-privilege enforcement
It ensures that only the right users have access to sensitive data, and that access is continuously validated. - Audit-ready reporting and evidence generation
Generating reports for auditors becomes significantly easier, as DSPM maintains logs, access records, and risk history automatically. - Reduced manual audit effort
Security and compliance teams spend less time collecting evidence and more time improving controls.
DSPM for AI & Generative Systems
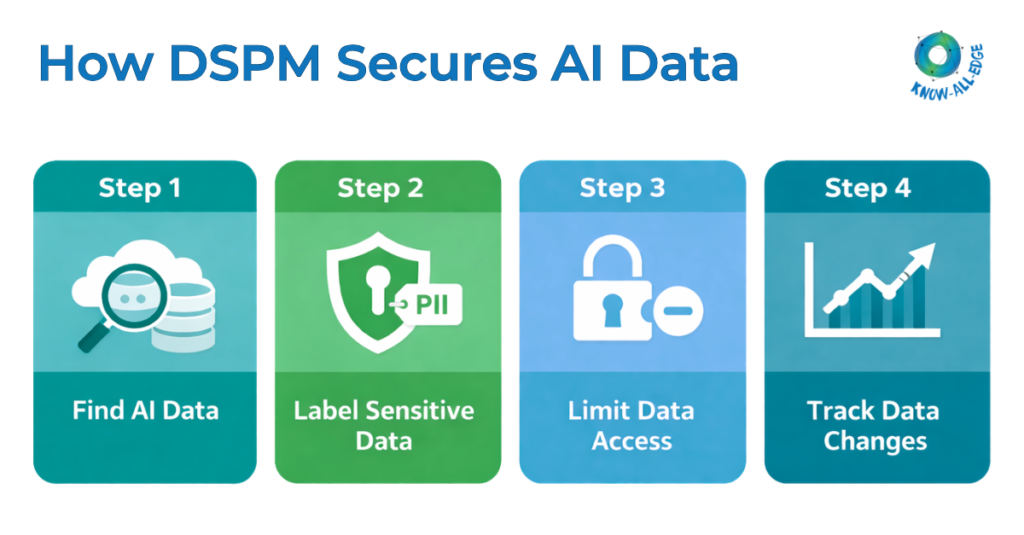
AI adoption is accelerating across industries, but it is also introducing a new category of data risk. Most organizations are still figuring out how to secure data used in AI pipelines.
This is where DSPM becomes highly relevant, not as an add-on, but as a foundational control layer.
Key risks in AI pipelines
AI systems depend heavily on data, and that creates multiple points of exposure. Common risks include:
- Data leakage through training datasets
- Prompt injection attacks that expose sensitive information
- Shadow datasets used without proper governance
These risks are often overlooked because AI development moves faster than traditional security processes.
Protection of sensitive training and inference data
Training data often includes sensitive information, sometimes without teams realizing it. Once that data is used in a model, controlling its exposure becomes more complex.
DSPM helps by:
- Identifying sensitive data before it is used in training
- Classifying and tagging datasets based on risk
- Ensuring regulated data is handled according to policy
This reduces the chances of sensitive information being embedded into models unintentionally.
Monitoring data exposure in AI and LLM systems
Large language models and AI applications can inadvertently expose data through outputs or integrations. This is a growing concern for enterprises.
Data security posture management provides visibility into what data is being accessed by AI systems, how that data is being used or processed, and whether any sensitive information is being exposed externally.
This level of monitoring is critical as AI systems become more integrated into business workflows.
Data governance across AI pipelines
AI pipelines often involve multiple stages, data ingestion, preprocessing, training, and inference. Each stage introduces its own risks.
DSPM ensures governance across the entire pipeline by:
- Tracking data lineage from source to model
- Enforcing policies at each stage of processing
- Maintaining consistency in how data is handled
This prevents gaps where sensitive data could slip through controls.
Preventing unauthorized access and data leakage
AI environments often involve multiple teams, tools, and integrations. Without proper control, access can quickly become fragmented.
DSPM addresses this by:
- Enforcing strict access controls on AI datasets
- Monitoring unusual access patterns
- Detecting potential data exfiltration attempts
These controls help reduce both accidental and intentional data leakage.
Ensuring compliance when using regulated data
Using regulated data in AI systems adds another layer of complexity. Organizations must ensure that data usage aligns with legal and regulatory requirements.
DSPM supports this by:
- Identifying regulated data within AI workflows
- Applying compliance policies automatically
- Providing audit trails for how data is used in models
This is particularly important in sectors like finance and healthcare, where misuse of data can lead to serious regulatory consequences.
DSPM vs Other Security Solutions
There is often confusion around where data security posture management fits within the broader security stack. It is not a replacement for existing tools, but it does fill a critical gap that most solutions do not address directly.
Here is a quick comparison to clarify:
| Solution | Primary Focus | Limitation | Where DSPM Fits |
| CSPM | Cloud infrastructure misconfigurations | Does not understand data sensitivity | Adds data-level visibility and risk context |
| SSPM | SaaS application security posture | Limited insight into actual data inside apps | Identifies and protects sensitive data within SaaS |
| DLP | Prevents data exfiltration | Reactive and policy-heavy | Provides continuous visibility and risk prioritization |
| CASB | Controls SaaS access and usage | Focuses on access, not deep data context | Enhances with data discovery and classification |
| Traditional data governance tools | Data organization and compliance workflows | Not built for real-time security risk detection | Adds real-time monitoring and risk analysis |
Read more: DSPM vs CSPM: The Key Difference Security Teams Overlook
Challenges in DSPM Implementation
While DSPM security brings strong advantages, implementing it is not always straightforward. Most DSPM challenges are not technical alone, they are operational and organizational as well.
Data sprawl across multi-cloud and hybrid environments
Data today is distributed across multiple cloud providers, on-prem systems, and SaaS platforms. This makes unified visibility difficult.
DSPM tools need to integrate deeply across environments, which can take time and planning. Without proper coverage, blind spots can still exist.
Limited visibility into unstructured data
A large portion of enterprise data is unstructured, documents, emails, logs, and more. This type of data is harder to classify and analyze accurately.
Even with DSPM, achieving high classification accuracy requires tuning and continuous improvement.
Integration complexity with existing systems
DSPM does not operate in isolation. It needs to connect with cloud platforms, identity systems, data warehouses, and security tools.
These integrations can become complex, especially in large enterprises with legacy systems. Poor integration can limit the effectiveness of DSPM.
False positives and alert fatigue
If not configured properly, DSPM tools can generate excessive alerts. Over time, this leads to alert fatigue, where teams start ignoring notifications.
This is why tuning, prioritization, and context-aware analysis are critical for success.
Organizational silos and ownership gaps
Data ownership is often unclear. Different teams manage different systems, and no single team has complete visibility.
Data security posture management requires collaboration between security, data, and engineering teams. Without clear ownership, implementation can slow down.
Skill and resource constraints
Deploying and managing DSPM requires skilled resources who understand both security and data environments.
Many organizations face gaps in:
- Data security expertise
- Cloud and SaaS architecture understanding
- Ongoing monitoring and optimization capabilities
Addressing these gaps is essential to fully realize the value of DSPM.
DSPM Best Practices
Implementing data security posture management does not need to be overly complex, but it does require the right priorities from the start. Many organizations fail because they try to cover everything at once. That approach rarely works.
Here are a few practical DSPM best practices that actually make a difference:
- Start with high-risk data: Focus on sensitive datasets first, PII, financial data, and critical business information. Trying to secure everything equally will slow you down.
- Prioritize classification accuracy: If your classification is wrong, everything built on top of it will be unreliable. Spend time tuning this early.
- Implement least-privilege access: Reduce access to only what is necessary. Most environments today have far more access than required.
- Automate wherever possible: Manual processes do not scale. Use automation for discovery, risk detection, and even remediation where feasible.
- Align DSPM with DevSecOps: Integrate DSPM into development and data workflows. Security should not be an afterthought once data is already exposed.
- Continuously monitor and improve: DSPM is not a one-time deployment. It needs regular tuning based on new data, systems, and risk patterns.
Implementation Roadmap
The key is to approach DSPM framework in phases instead of a single rollout. This keeps the process controlled and measurable.
Phase 1: Assessment
Start by understanding where your data resides across systems and define clear security and compliance goals. This step builds the foundation, without it, tool selection becomes guesswork.
Phase 2: Tooling and Setup
Choose a DSPM solution that fits your environment, then integrate it with cloud, SaaS, and data platforms. Keep the setup focused and avoid overcomplicating integrations early on.
Phase 3: Deployment
Run data discovery and classification, and apply initial security policies. Some noise is expected at this stage as the system starts learning your environment.
Phase 4: Optimization
Refine the system by tuning alerts and reducing false positives. Automate common remediation actions to make DSPM practical for daily use.
Phase 5: Scale
Expand DSPM across AI systems, SaaS tools, and new environments. Strengthen governance and monitoring so it becomes part of your core security strategy.
DSPM Tools & Market Landscape
The data security posture management market is evolving quickly, with several vendors offering strong capabilities across discovery, classification, and risk analysis. The right choice of DSPM vendor depends on your data environment, integration needs, and level of automation required.
Here is a quick overview of some leading DSPM-focused and adjacent vendors:
- Forcepoint
Known for its data-first security approach, Forcepoint combines DSPM with DLP and insider risk capabilities, making it suitable for enterprises looking for unified data protection. - Fortra
Offers strong data protection and classification capabilities, with DSPM elements integrated into its broader security portfolio. - Palo Alto Networks
Provides DSPM through its cloud security platform, focusing on deep integration with cloud workloads and real-time risk visibility. - Proofpoint
Strong in data protection and insider threat management, with DSPM capabilities aligned around data visibility and user behavior. - SentinelOne
Expanding into data security with AI-driven insights, combining endpoint, cloud, and data visibility into a unified platform.
Key evaluation criteria
When evaluating a DSPM solution, keep it simple and focused on what matters:
- Coverage across cloud, SaaS, and data platforms
- Accuracy of data discovery and classification
- Integration with existing security and data tools
- Level of automation in risk detection and remediation
Future of Data Security Posture Management
Data security posture management is not a short-term trend, it is becoming a core layer in modern security architecture. As data environments grow more complex, the role of DSPM will continue to expand.
Here are a few clear directions shaping its future:
- AI-driven and autonomous data security
DSPM solutions are moving toward automated decision-making, where risks are identified and resolved with minimal human intervention. - Real-time posture scoring and risk visibility
Organizations will increasingly rely on live risk scores to understand their data security posture at any moment, not just during audits. - Convergence with data governance and privacy tools
The line between security, privacy, and governance is blurring. DSPM will act as a bridge across these functions. - Integration with Zero Trust architectures
Data-level visibility will play a key role in enforcing Zero Trust principles, especially around access control and verification.
- Expansion across multi-cloud and hybrid ecosystems
As environments become more distributed, DSPM will need to provide consistent visibility across all data locations.
Conclusion
Data is now the primary target, and protecting it requires more than traditional controls. DSPM moves security focus from systems to data, and it is much needed in modern tech stack.
It brings continuous visibility, context-driven risk analysis, and automated protection into one framework. It helps organizations move from reactive security to a more proactive and data-centric approach.
At the same time, implementation needs to be practical. Start small, focus on high-risk data, and scale gradually. The goal is not perfection from day one, but consistent improvement in visibility and control.
We help organizations implement DSPM solutions that align with their existing infrastructure and compliance needs. From tool selection to deployment and optimization, we ensure DSPM delivers real business value, not just technical capability.
If you are evaluating DSPM or planning your next step in data security, this is the right time to act.
Get in touch with our team to assess your current data security posture and build a DSPM strategy tailored to your environment.
FAQs on Data Security Posture Management (DSPM)
What is DSPM in simple terms?
DSPM, or data security posture management, is a way to continuously discover, classify, and protect sensitive data across all your systems. Instead of focusing only on infrastructure, it focuses directly on the data, where it is present, who can access it, and whether it is exposed. In simple terms, it gives you a live view of your data risk at any point in time.
Why do organizations need DSPM today?
Organizations are dealing with massive data growth across cloud, SaaS, and AI environments. Traditional tools were not designed for this level of complexity.
DSPM helps by:
- Providing continuous visibility into sensitive data
- Identifying exposures like misconfigurations and over-permissioned access
- Supporting compliance with evolving regulations
Without DSPM, most teams are operating with partial visibility, which increases both security and compliance risks.
Is DSPM suitable for small and mid-sized businesses?
Yes, but the approach may differ from large enterprises. SMBs often have fewer resources, so they benefit from DSPM solutions that are easier to deploy and manage.
If your business handles customer data, financial records, or any regulated information, DSPM can add value by reducing risk and simplifying compliance. The key is to start focused, rather than trying to implement everything at once.
What should you look for in a DSPM solution?
Choosing the right DSPM solution depends on your environment, but a few factors matter consistently:
- Strong data discovery and classification accuracy
- Coverage across cloud, SaaS, and data platforms
- Integration with existing security and data tools
- Clear risk prioritization, not just raw alerts
- Automation for detection and remediation
A good DSPM solution should reduce complexity, not add to it. If it requires heavy manual effort, adoption will likely struggle.
Is DSPM a replacement for DLP or CASB?
No, DSPM is not a replacement for tools like DLP or CASB. It works alongside them.
- DLP focuses on preventing data loss and enforcing policies
- CASB controls access and usage of SaaS applications
- DSPM provides deep visibility into where sensitive data exists and what risks are associated with it
Together, they create a more complete data security strategy. DSPM fills the visibility and context gap that other tools typically miss.
