Data keeps growing and regulations keep tightening. And somewhere in the middle, security teams are expected to hold everything together with tools that were built for a very different era.
If you’re running security or technology at a large organization today, you already know this tension. The question isn’t whether you need a DSPM framework. The question is whether the one you have – or plan to build – is actually doing the job.
This blog breaks down
- what a practical DSPM framework looks like,
- why it is important for compliance,
- and how organizations are using DSPM strategies to stay ahead of regulatory requirements.
Let’s begin.
Why Compliance is Breaking in Modern Data Environments
Compliance used to be treated as a checkbox exercise. Conduct the audit, update the policy document, pass the assessment, and move on. That model doesn’t hold up anymore.
The global average cost of a data breach reached $4.44 million in 2025, a number that reflects more than just financial loss. It signals how unprepared many organizations still are when it comes to data visibility and control.
The problem isn’t that companies are ignoring compliance. It’s that they’re trying to stay compliant in environments that are far more complex than the regulations anticipated. Data is now present across cloud services, SaaS platforms, employee devices, third-party systems, and AI tools.
It is found that lack of visibility into data is a major contributor to a weak security posture.
This is the gap the DSPM framework is designed to close.
Also read: What is Data Security Posture Management (DSPM): Explained in Detail
What is the DSPM Governance Framework?
The DSPM governance framework is the policy and control layer that ensures data is handled responsibly across its lifecycle. It defines who owns the data, who can access it, and how it should be protected.
It is a bridge between security operations and compliance requirements. It aligns technical controls with legal obligations.
A strong governance framework typically includes:
- Clear data ownership and accountability
- Defined access control policies
- Continuous compliance monitoring
- Risk-based data handling rules
- Audit-ready reporting mechanisms
Without governance, even the best DSPM solutions fall short. You may discover data, but you cannot enforce how it is used.
Core Components of a Working DSPM Framework
A compliance-driven DSPM framework is not just about visibility. It is about action. Below are the key components that make it effective.
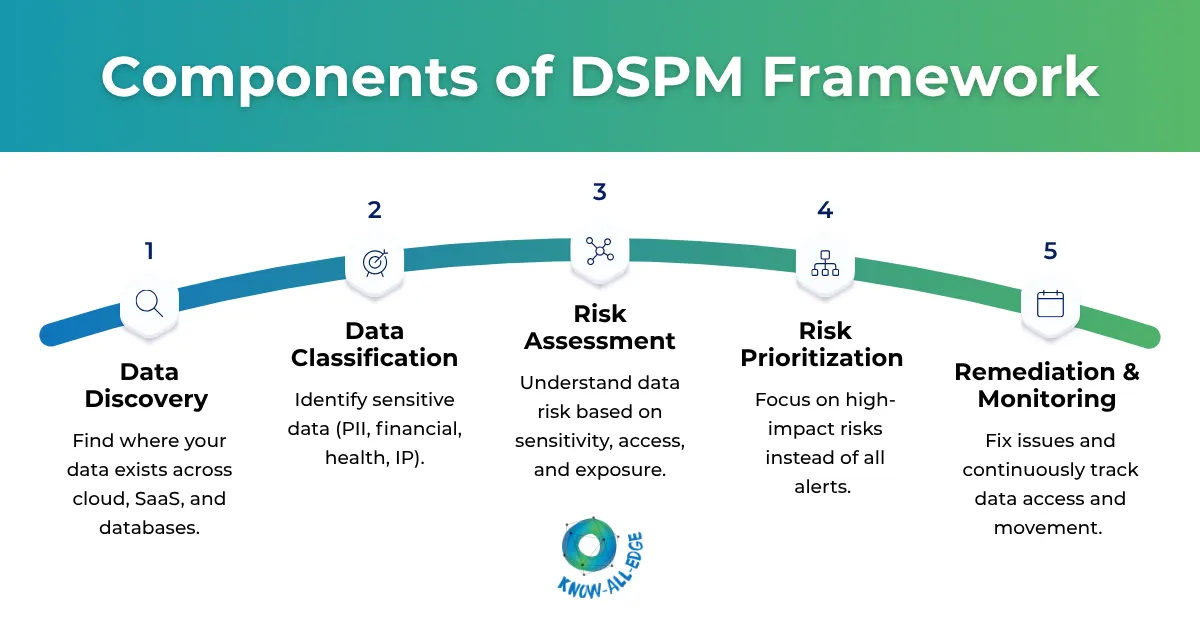
Data Discovery
You cannot protect what you cannot see. Data discovery is the foundation of DSPM. It involves automatically scanning and cataloging all sensitive data across endpoints, cloud environments, SaaS applications, and on-premises infrastructure.
This includes the obvious places – CRM systems, HR databases, finance platforms, chats, email archives, shared drives, and backup repositories. Gartner data says, by 2026, over 20% of organizations are expected to deploy DSPM solutions specifically to address shadow data (unmonitored or unmanaged data) risks.
Data Classification
Data needs to be categorized, once you discover it. Not everything carries the same risk. A company logo and a patient’s health record are both “files,” but they demand completely different levels of protection.
Classification based on sensitivity levels, regulatory affiliation (such as GDPR, HIPAA, or DPDPA), and business context gives security teams the ability to apply proportionate controls.
It also makes it easier to generate audit-ready reports without scrambling at the last minute.
Risk Identification and Prioritization
A striking 67% of organizations have former employees who still retain access to Google Workspace assets for more than five years after leaving. Excessive and outdated permissions are one of the most consistent sources of data exposure, and they rarely show up in standard audits.
DSPM identifies risks like:
- Overexposed data
- Misconfigured cloud storage
- Excessive user permissions
- Shadow data repositories
According to a Gartner survey, misconfigurations contribute to 80% of all data security breaches.
DSPM tools detect these gaps and, in many cases, automate their remediation.
Policy Enforcement and Governance Controls
This is where compliance becomes real.
Policies define how data should be accessed, stored, and shared. DSPM enforces these policies automatically.
For example:
- Restricting access to sensitive data based on roles
- Blocking data sharing outside approved environments
- Enforcing encryption requirements
These controls ensure that compliance is not just documented, but actively maintained.
Real-Time Monitoring and Incident Response
Compliance is not a one-time effort. It is continuous. DSPM solutions monitor data activity in real time. They track who accessed what data, when, and why.
If something unusual happens, such as unauthorized access, alerts are triggered immediately. Some systems even automate responses, reducing the time to contain threats.
This is crucial because delayed responses often lead to regulatory penalties.
Practical DSPM Strategies That Actually Work
Many organizations fail because they overcomplicate their approach. A practical DSPM approach focuses on execution, not theory.
Here are some proven strategies:
- Start with High-Risk Data: Do not try to secure everything at once. Focus on sensitive data first, such as customer records or financial information.
- Integrate with Existing Security Tools: DSPM should not operate in isolation. It should work alongside SIEM, DLP, and identity management systems.
- Automate Wherever Possible: Manual processes slow down compliance. Automation ensures consistency and reduces human error.
- Build Cross-Functional Ownership: Data security is not just an IT problem. Legal, compliance, and business teams must be involved.
- Measure and Improve Continuously: Use metrics like risk reduction, incident response time, and compliance coverage to track progress.
Also Read: DSPM Best Practices: Secure Unstructured, and Unmanageable Data
How DSPM Solutions Strengthen Compliance Posture
Modern DSPM solutions go beyond visibility. They actively improve compliance with readiness.
Here is how:
- Unified Data View: They provide a single dashboard for all sensitive data across environments
- Automated Compliance Mapping: They align data controls with frameworks like GDPR, HIPAA, and DPDPA
- Audit Readiness: They generate reports that simplify audits and reduce preparation time
- Proactive Risk Management: They identify issues before they become compliance violations
Building Your DSPM Framework: 7 Practical Steps
Getting a DSPM program off the ground doesn’t require starting from scratch. Most organizations already have pieces of the puzzle. The goal is to connect them.
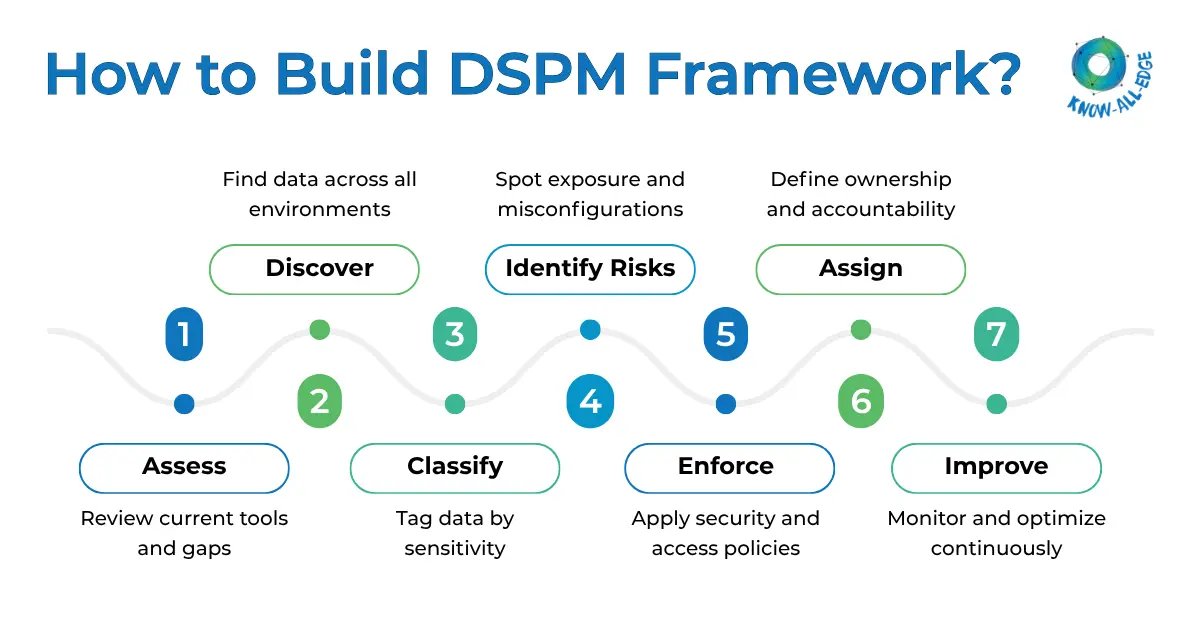
- Step 1: Assess your current data management state. Understand what tools you already have and what gaps exist in discovery and visibility.
- Step 2: Discover and classify data across endpoints, cloud services, SaaS applications, and on-premises systems.
- Step 3: Categorize by sensitivity. PHI, PII, financial records, and internal documents all carry different risk profiles. Security configurations should reflect that difference.
- Step 4: Assess risks tied to each data category – excessive permissions, misconfigurations, shadow data, and compliance gaps.
- Step 5: Create and enforce policies based on identified risks. For example, a rule that prevents Indian citizen data from being uploaded to unsanctioned AI tools, or DLP policies that restrict sensitive records from being shared outside approved systems.
- Step 6: Make sure everyone understands their role in data protection. Clear ownership reduces confusion during critical situations like audits or data breaches.
- Step 7: Regularly review to identify gaps and improve the overall effectiveness of your DSPM strategy.
Why DSPM Is the Fastest-Growing Security Category Right Now
DSPM is currently the fastest-growing category in enterprise security. Traditional tools simply cannot scale to the environments organizations operate in today.
Manual audits, periodic scans, and legacy DLP solutions were not designed for multi-cloud, hybrid, and AI-powered data environments.
DSPM solutions with AI-driven classification and continuous monitoring are replacing the patchwork approach. Audit preparation time has dropped by 60 to 70% in organizations using unified compliance monitoring across infrastructure and data layers. That’s not a marginal improvement. It changes what security teams can actually accomplish.
Final Thoughts
Data is now the most valuable asset, and the most vulnerable one. Compliance is no longer just about ticking boxes. It requires continuous awareness and control over how data moves and is used.
A well-structured DSPM framework provides that control. It brings together visibility, governance, and automation in a way that aligns with modern compliance demands.
Don’t wait to adopt DSPM. You need to quickly implement it before the next audit, or the next breach.
If you are looking to strengthen your data security posture, now is the right time to act. We can be the right partner who can help you design and implement effective DSPM solutions that fit your environment, simplify compliance, and reduce risk without slowing down your business. Talk to our experts today!
Frequently Asked Questions
How often should a DSPM framework be reviewed or updated?
At a minimum, a quarterly review of data classifications, access policies, and risk findings is good practice. That said, DSPM frameworks work best when they run continuously in the background, automatically surfacing changes rather than relying solely on scheduled reviews.
How long does it take to implement a DSPM framework?
Initial deployment can take a few weeks, but building a mature framework is an ongoing process that evolves with your data environment.
Does adopting DSPM solutions require replacing existing security tools?
Not necessarily. Most DSPM solutions are designed to integrate with existing SIEM, SOAR, CSPM, and identity management platforms. They add a data-centric layer on top of existing infrastructure rather than replacing it, feeding richer context into tools teams already use.
