In January 2024, Russian state-sponsored hackers breached Microsoft’s corporate email systems, not through a sophisticated zero-day, but via a password spray on a legacy test account without multi-factor authentication. The attackers moved laterally for weeks before detection, accessing senior leadership communications and source code repositories. Microsoft, a company that sells security products, was compromised because one account operated outside their zero-trust perimeter.
That incident illustrates the core argument for zero trust: perimeter-based security fails in environments where the perimeter no longer exists. This guide walks through exactly how to implement zero trust security in your organization, from the discovery phase through full maturation, using a practical, sequenced approach that security teams can actually execute.
What is Zero Trust Security?
Zero trust is a security framework built on one principle: “never trust, always verify.”
Unlike traditional models that assume traffic inside the network is trustworthy, zero trust treats every access request as potentially hostile, regardless of whether it originates inside or outside the network.
The model has five core pillars, as defined by CISA’s Zero Trust Maturity Model:
- Identity: Users, service accounts, and machine identities all require continuous verification
- Devices: Device health and compliance are evaluated at every access attempt
- Networks: Traffic is segmented and inspected; broad access is replaced with application-specific access
- Applications: Access is granted per-application, not per-network zone
- Data: Sensitive data is classified, monitored, and protected regardless of where it lives
Zero trust is not a product you buy. It is an architecture you build incrementally. No single vendor delivers it. Organizations that implement it successfully do so by following a deliberate sequence – starting with identity, not the network.
Before You Begin: The Discovery Phase You Cannot Skip
Most zero trust implementations fail not because the technology is wrong, but because organizations skip the assessment phase and try to deploy controls before they understand what they are protecting. The NSA’s 2026 Zero Trust Implementation Guidelines (ZIGs) identify discovery as the foundational prerequisite, and it is.
Four things you must map before writing a single policy:
(1) Identity Inventory
Map every identity in your environment: employees, contractors, service accounts, API keys, and machine identities. As per Gartner, in a typical mid-size enterprise, human users represent less than 40% of total identities. The rest are service accounts and machine identities, and they are almost always the most neglected.
(2) Data Inventory
Where does sensitive data live? What is your most critical intellectual property? Which systems contain regulated data (PII, PHI, and financial records)? Zero trust controls should be densest around your most valuable assets.
(3) Traffic Flow Mapping
What applications do users access? Which services communicate with each other? Network flow analysis tools can automate much of this, but the goal is to identify which connections are necessary versus merely convenient.
(4) Current Control Inventory
Where is MFA already enforced? Where are the authentication gaps? What monitoring capabilities exist? Document what you have before planning what you need.
Plan for 4 to 8 weeks for a thorough discovery phase. This is not a time that can be compressed. Everything else in your zero-trust implementation roadmap builds on this foundation.
Also Read: Zero Trust Implementation Roadmap: 5 Stages from Legacy to Modern Security
How to Implement Zero Trust: Step-by-Step Approach?
This section outlines how to implement zero trust step by step, focusing on the controls that deliver the most impact first.
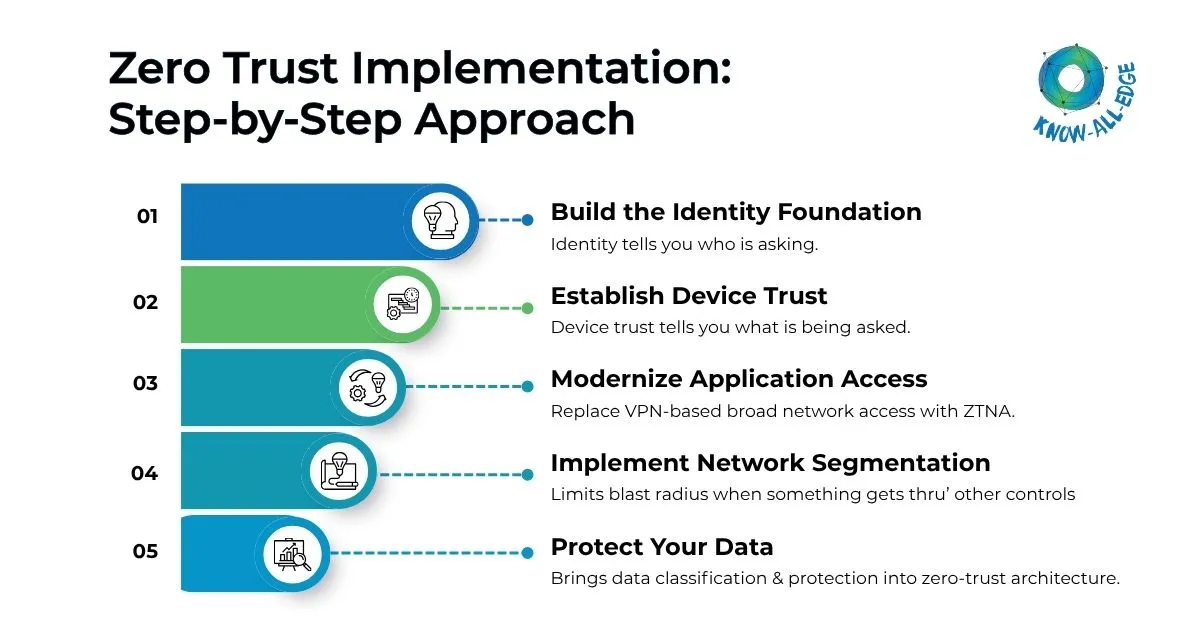
Step 1: Build the Identity Foundation
Every zero-trust implementation should start with identity. Not the network. Not the applications. Identity.
The practical reason: Identity controls deliver immediate security value and stop credential-based attacks that account for the majority of breaches. The architectural reason: every other zero trust control references identity as its primary input. A weak identity layer makes every downstream control less reliable.
Consolidate identity providers
Fragmented identity systems, like multiple directories, Active Directory not synced with cloud IdPs, departmental identity systems, create gaps that attackers exploit. Work toward a unified identity platform that authenticates all users across all applications.
Enforce MFA universally
No exceptions. Not for executives who find it inconvenient. Not for legacy applications that “do not support it” if a legacy application cannot support MFA directly, implement it at the proxy layer. MFA enforcement is the single highest-ROI control in any zero-trust implementation.
Audit privileged accounts
Every administrative account should be reviewed. Accounts not actively used should be disabled. Privileged access should require just-in-time approval, no standing admin access outside a break-glass emergency process.
Implement lifecycle management
Inactive accounts are one of the most persistent security gaps in most organizations. Employees who left years ago often still have active access. Automated deprovisioning triggered by HR system events closes this gap systematically.
Govern service accounts
Service accounts are the most neglected identity class.
- Inventory them all.
- Assign ownership.
- Rotate credentials on a schedule.
- Apply least-privilege access.
This is tedious work but essential for implementing zero trust effectively.
Stage 1 completion criteria: MFA enforced for 100% of users, inactive accounts identified and disabled, all privileged accounts under PAM, service account ownership documented.
Step 2: Establish Device Trust
Identity tells you who is asking. Device trust tells you what. A valid credential on a compromised device is still a threat vector.
Deploy endpoint management
If MDM or UEM does not cover your managed devices, deploy it now. Your goal is a complete, current inventory of corporate devices with real-time visibility into their compliance state.
Define device compliance policy
What does a “healthy” device look like in your environment? Minimum OS version, required patch level, endpoint protection installed and current, full-disk encryption enabled. Define these criteria explicitly, not generally.
Implement conditional access
Conditional access policies evaluate device compliance at authentication time. Devices that do not meet policy are denied access, required to complete step-up MFA, or limited to a restricted application set. This is where device trust begins influencing access decisions in real time.
Handle BYOD deliberately
Personal devices require a deliberate policy decision. Options range from no personal device access through a managed browser to full access for enrolled personal devices. Make an explicit choice and document it.
Stage 2 completion criteria: 95%+ of corporate devices enrolled in endpoint management, compliance policies enforced in conditional access, non-compliant devices restricted.
Step 3: Modernize Application Access
Stage 3 addresses one of the most consequential shifts in a ZTNA implementation: replacing VPN-based broad network access with Zero Trust Network Access (ZTNA) that grants access to specific applications only.
Prioritize your application portfolio
Start with the highest-risk, most-accessed applications typically those currently requiring VPN access that also contain sensitive data. Full migration does not happen at once.
Deploy ZTNA for high-priority applications
Instead of connecting to the corporate network and then accessing an application, users authenticate directly to the application via a ZTNA broker. No network access is granted at all. The application is invisible to users who are not authorized to access it.
Implement Single Sign-On
SSO improves security by centralizing credential management and visibility, while reducing friction for users. Every application that supports SAML, OIDC, or similar standards should be integrated with your identity provider.
Secure service-to-service communication
Internal service calls are often entirely unauthenticated – a major blind spot. Define service-to-service authentication using mutual TLS or short-lived token-based approaches. Every internal API should require caller identity, not just network location.
Stage 3 completion criteria: VPN access eliminated for externally accessible applications, SSO covering 80%+ of applications by usage, service-to-service authentication active for critical APIs.
Learn more: How to Implement Zero Trust Network Access (ZTNA) Without Killing Productivity
Step 4: Implement Network Segmentation
Network segmentation limits the blast radius when something gets through your other controls. It is sequenced at Stage 4 because it requires the visibility and identity foundation built in earlier stages.
Map actual traffic flows
By Stage 4, you have better data than you did in discovery. Use network flow analysis to map east-west traffic in your environment – what is actually talking to what, not what your architecture diagrams suggest.
Design a segmentation model
Three broad approaches are common: macro-segmentation divides the environment into broad zones; micro-segmentation creates application-to-application controls; and a hybrid approach applies micro-segmentation only to your most sensitive systems and macro-segmentation elsewhere.
Implement and validate
Deploy segments incrementally. Validate each new boundary with penetration testing before expanding. Network segmentation done incorrectly can break business-critical workflows, validation at each step is not optional.
Stage 4 completion criteria: Network segments implemented for critical systems, traffic between systems clearly visible, and unnecessary access between segments restricted.
Step 5: Protect Your Data
Stage 5 brings data classification and protection into the zero-trust architecture. Controls at the identity, device, and application layers reduce risk, but they do not eliminate the need for data-level protection particularly for sensitive data that users legitimately access.
Classify data systematically
Deploy data classification tooling to identify and label sensitive data across file storage, databases, email, and cloud platforms. Classification is the prerequisite for applying proportional controls.
Apply data loss prevention controls
DLP policies enforce rules about how classified data can be shared, copied, or transmitted. Apply them at the endpoint, in email, and in cloud platforms.
Implement monitoring and logging
All access to sensitive data should be logged with sufficient context to reconstruct events. This supports both threat detection and compliance reporting.
Stage 5 completion criteria: Sensitive data identified and classified, DLP policies in place, and access to sensitive data logged and monitored.
Common Mistakes That Sink Zero Trust Implementations
- Starting with the network instead of identity – the most common and most costly mistake
- Purchasing a single “zero trust product” and expecting it to do the work
- Treating zero trust as a one-time project rather than an ongoing architecture
- Skipping the discovery phase and deploying controls without understanding the environment
- Neglecting service accounts and machine identities while focusing only on human users
- Failing to align with HR and legal during identity lifecycle management deployment
Measuring Progress
Zero trust implementations require ongoing measurement. Track these metrics to evaluate effectiveness:
- MFA adoption rate – target 100% for all users and service accounts
- Mean time to revoke access – target under 15 minutes for automated response
- Percentage of applications behind ZTNA – track migration progress from VPN
- Number of lateral movement incidents detected – should decrease as segmentation matures
- Percentage of sensitive data classified – measures data layer progress
According to IBM’s Cost of a Data Breach Report, organizations with a mature zero trust strategy reduce breach costs significantly compared to those without it. Combined with strong identity controls like MFA, which can prevent over 99.9% of account compromise attacks – zero trust investments are both measurable and impactful.
Final Thoughts
Implementing zero trust security is not a quick project. It is a multi-year architecture transformation that, done correctly, fundamentally changes how your organization thinks about trust, access, and verification. The organizations that succeed share one characteristic: they implement incrementally, in a deliberate sequence, with clear milestones at each stage.
Start with identity. Build the foundation before adding layers. Measure everything. And revisit your architecture continuously as threats, users, and applications evolve.
Ready to implement zero trust? We help you assess your environment, prioritize the right controls, and execute a practical roadmap, so you can move from strategy to a working architecture, faster. Get in touch to start your zero trust implementation.
FAQs on Zero Trust Implementation
What is the first step to implement zero trust security?
The first step is identity — specifically, enforcing MFA across all users and conducting a full inventory of every identity in your environment, including service accounts and machine identities. Most guides suggest starting with the network, but identity is where the majority of breaches originate and where zero trust controls deliver the fastest security ROI.
How long does zero trust implementation take?
A realistic zero trust implementation takes 2–3 years to reach a mature, measurable state across all five pillars (identity, devices, networks, applications, data). The first stage (identity foundation with universal MFA) can be completed in 3–6 months. Discovery and assessment alone typically require 4–8 weeks before any controls are deployed.
Can a small business implement zero trust security?
Yes, but the approach should be scaled to resources. Small businesses should prioritize identity (MFA, SSO, account lifecycle management) and application access (cloud-native ZTNA tools are increasingly affordable) before tackling network segmentation, which is more complex and costly. Many SMBs achieve strong zero trust posture using a combination of Microsoft Entra, Cloudflare Access, or similar platforms without enterprise-level spend.
Do I need to replace all my existing security tools to implement zero trust?
No. Zero trust is an architecture, not a product replacement. Most organizations already have MFA, EDR, and some form of IAM that can be integrated and orchestrated into a zero-trust model. The approach is to extend and connect existing investments before buying new tools. New purchases, typically a ZTNA solution and possibly a PAM platform are additive, not replacements.
What are the biggest mistakes in zero trust implementation?
The three most common mistakes are: starting with the network instead of identity, purchasing a single “zero trust product” expecting it to deliver the full model, and treating implementation as a one-time project rather than an ongoing architecture. A fourth frequent mistake is neglecting service accounts and machine identities while focusing exclusively on human users which leaves a significant blind spot.
What is the cost to implement Zero Trust?
The cost of implementing Zero Trust depends on factors like organization size, existing infrastructure, number of users, and security requirements. Costs typically include IAM, MFA, ZTNA, endpoint security, monitoring tools, and deployment services. Organizations with modern security infrastructure may require lower investment compared to complex legacy environments.
