Most zero trust initiatives stall. Not because technology is flawed, but because organizations approach it as a technology project rather than an architecture transformation. They try to do everything simultaneously, or they purchase a platform expecting it to deliver zero trust automatically, or they treat the rollout as a one-time effort rather than an evolving program.
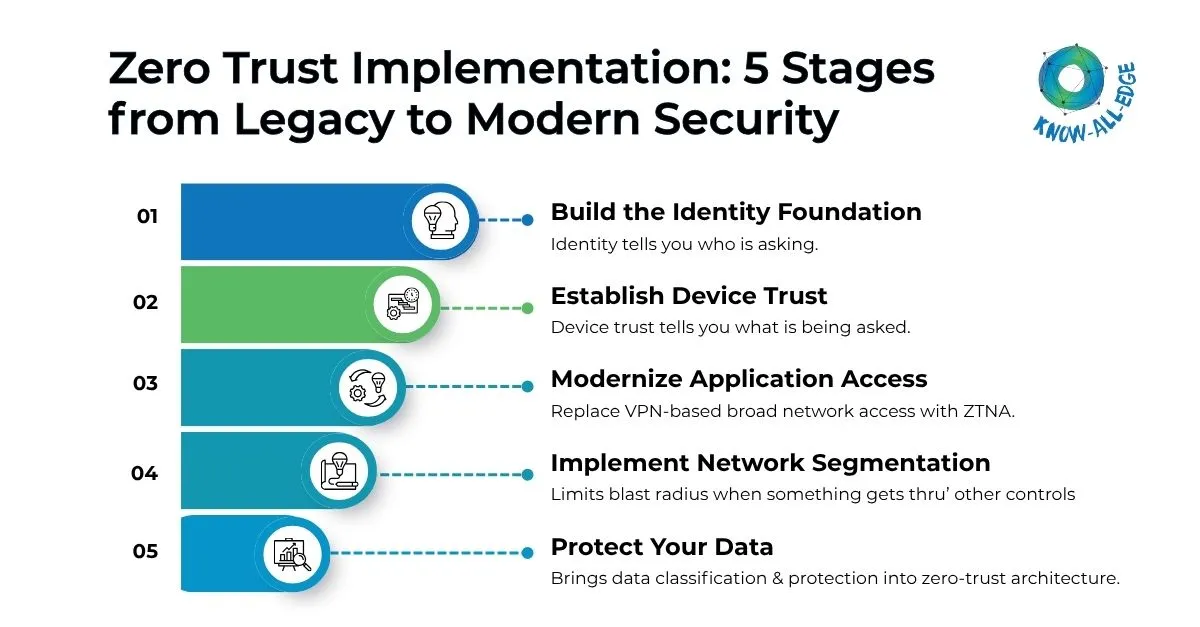
This zero trust implementation roadmap presents the five stages that organizations follow when they succeed and build momentum with clear milestones at each phase.
Why Sequence Matters
Zero trust is not a single technology. It is an architecture built from layered controls across identity, devices, networks, applications, and data. Each layer builds on the previous one. Skipping stages, or implementing them out of order, creates gaps that attackers exploit.
By the end of 2026, Gartner projects only 10% of large enterprises will have a mature and measurable zero trust program (up from less than 1% in 2023). The gap between ambition and execution is the sequencing problem. This roadmap solves it.
Here we go to the zero trust implementation phases.
The Assessment Phase: Before Any Stage Begins
The most common mistake in zero trust implementation is treating discovery as optional. It is not. Before any control is deployed, organizations must map four things:
- All identities — human users, service accounts, API keys, and machine identities
- Data locations — where sensitive and regulated data reside across the environment
- Traffic flows — what is actually communicating with what, not what diagrams suggest
- Current control gaps — where authentication is weak, monitoring is absent, or access is unconstrained
Plan 4 to 8 weeks for a serious discovery phase. Everything else in the zero trust implementation roadmap builds on this foundation.
Stage 1: Identity Foundation
Core principle: You cannot build zero trust on identity you cannot trust.
Every zero-trust roadmap should begin with identity. Identity is where the majority of breaches originate — credential theft, password spray attacks, and compromised service accounts account for most initial access events. Establishing identity as the new perimeter is both the highest-value starting point and the prerequisite for every downstream control.
Key actions in Stage 1
- Consolidate identity providers into a unified platform covering all users and applications
- Enforce MFA universally — no exceptions for executives, legacy apps, or on-call engineers
- Audit all privileged accounts and implement just-in-time access with PAM
- Automate account lifecycle management tied to HR system events
- Inventory and govern all service accounts: assign ownership, rotate credentials, apply least privilege
Stage 1 milestone criteria
- MFA enforced for 100% of users
- Inactive accounts (60+ days) disabled or documented
- All privileged accounts under PAM
- Service account ownership documented
Organizations often underestimate service account work. In most enterprises, machine and service identities outnumber human users. Leaving them unmanaged while focusing on human MFA creates a significant blind spot.
Stage 2: Device Trust
Core principle: Identity tells you who is asking. Device trust tells you from what.
A valid credential on a compromised device is still a threat. Stage 2 in zero trust implementation roadmap builds the device trust layer so that device health becomes a factor in every access decision. Stages 2 and 3 can run in parallel. They are independent enough that progress in one does not block the other.
Key actions in Stage 2
- Deploy MDM or UEM to achieve a complete, current inventory of corporate devices
- Define device compliance policy explicitly: OS version, patch level, encryption, endpoint protection
- Implement conditional access policies that evaluate device compliance at authentication time
- Make a deliberate BYOD policy decision — implicit or undefined policies create risk
- Deploy device certificates via PKI for managed devices, enabling stronger authentication than device IDs alone
Stage 2 milestone criteria
- 95%+ of corporate devices enrolled in endpoint management
- Device compliance policy defined and enforced
- Non-compliant devices denied or restricted
- BYOD policy documented and implemented
Stage 3: Application Access Modernization
Core principle: Replace network access with application-specific access.
Stage 3 replaces VPN-based broad network access with Zero Trust Network Access (ZTNA). Instead of connecting to the corporate network and then navigating to an application, users authenticate directly to the specific application they need – no network access is granted at all.
This stage is often the most operationally complex because it directly changes the user experience for remote access and requires per-application configuration. Prioritize applications by risk and usage, not alphabetically.
Key actions in Stage 3
- Deploy ZTNA for high-priority applications first — those currently VPN-accessed with sensitive data
- Define per-application access policies: who can access it, under what conditions, with what restrictions
- Implement SSO for every application that supports SAML or OIDC
- Establish service-to-service authentication using mTLS or short-lived tokens — stop trusting network location
Stage 3 milestone criteria
- VPN eliminated or heavily restricted for externally accessible applications
- SSO covering 80%+ of applications by usage
- Per-application access policies active
- Service-to-service authentication implemented for critical internal APIs
Stage 4: Network Segmentation
Core principle: Limit the blast radius when something gets through.
Network segmentation is sequenced at Stage 4 because effective implementation requires the identity and visibility foundation from earlier stages. You need to know what should be communicating with what before you can enforce it.
Segmentation is often technically complex and operationally disruptive. Done correctly, it prevents the lateral movement that turns a single compromised endpoint into an enterprise-wide breach.
Key actions in Stage 4
- Analyze actual east-west traffic flows using network flow analysis tools
- Design segmentation boundaries — macro zones for broad control, micro-segmentation for critical systems
- Deploy network access control (NAC) to enforce policy at the access layer
- Validate each new boundary with penetration testing before expanding
- Monitor for anomalous inter-segment traffic continuously
Stage 4 milestone criteria
- Network segmented into logical zones with defined inter-zone policies
- Micro-segmentation applied to critical system environments
- Lateral movement monitoring active across all segments
Stage 5: Data Protection
Core principle: Protect the asset that matters most.
All previous stages of zero trust implementation roadmap reduce the likelihood of unauthorized access. Stage 5 protects the data itself — ensuring that even if an attacker navigates through identity, device, and network controls, sensitive data remains classified, monitored, and defensible.
Key actions in Stage 5
- Classify data systematically across file storage, databases, email, and cloud platforms
- Apply DLP policies to enforce rules about how classified data can be shared or transmitted
- Implement rights management for highly sensitive documents
- Log all access to sensitive data with sufficient context for forensic reconstruction
- Continuously monitor data access patterns for anomalies
Stage 5 milestone criteria
- Sensitive data classified across primary storage systems
- DLP policies active at endpoint, email, and cloud layers
- Data access logging operational with alerting for anomalous behavior
After Zero Trust Implementation Roadmap: Maturation is Not Optional
Completing five stages does not complete zero trust implementation roadmap. The CISA Zero Trust Maturity Model defines four maturity levels: Traditional, Initial, Advanced, and Optimal. Most organizations that reach Stage 5 are at the Initial or early Advanced level. Reaching Advanced across all pillars is a realistic 2 to 3 year goal for organizations that commit resources and executive sponsorship.
What changes at higher maturity levels:
- Policy management becomes automated rather than manual
- Access decisions incorporate behavioral signals and risk scoring, not just identity and device compliance
- Monitoring becomes continuous and correlated across all pillars
- Compliance reporting becomes automated from existing telemetry
The most persistent zero trust myth is that once implemented, it maintains itself. Zero trust requires continuous investment: environments change, threats evolve, and controls drift over time. Build ongoing governance into your program from Stage 1.
Building the Business Case
Zero trust has a measurable ROI. According to IBM’s Cost of a Data Breach Report, organizations with a mature zero trust approach experienced average breach costs of $3.31 million, compared to $5.04 million for those without—saving approximately $1.73 million per breach.
For the business case, frame the investment across three dimensions:
- Risk reduction — fewer breaches, smaller blast radius when incidents occur
- Operational efficiency — automated policy management, reduced manual access reviews, streamlined compliance
- Regulatory compliance — alignment with NIST 800-207, CISA ZT maturity model, and sector-specific requirements including CMMC and HIPAA
Conclusion
Zero trust is not something you implement all at once. It’s a step-by-step process that works best when you follow the right sequence and build gradually. Organizations that succeed start with identity and then expand controls across devices, applications, networks, and data.
This zero trust implementation roadmap gives you a clear path, but the real impact comes from execution. The sooner you start, the sooner you reduce risk and gain better control over your environment.
Want to see how this works in practice? Connect with us to explore how we help organizations implement zero trust step by step.
FAQs on Zero Trust Implementation Roadmap
What are the 5 stages of zero trust implementation?
The five stages, in recommended sequence, are:
(1) Identity Foundation: MFA, unified IdP, privileged account management
(2) Device Trust: Endpoint management, compliance policies, conditional access
(3) Application Access Modernization: ZTNA deployment, SSO, service-to-service authentication
(4) Network Segmentation: Micro and macro segmentation, NAC
(5) Data Protection: Classification, DLP, access monitoring.
Each stage has defined milestone criteria before the next begins.
How to implement Zero Trust Network Access (ZTNA) in my organization?
If you want to implement Zero Trust Network Access (ZTNA) in your organization, start by identifying which users need access to which applications and devices. Then apply identity-based controls like MFA, device posture checks, and least-privilege access policies. Most organizations roll out ZTNA gradually by starting with a few applications first and then expanding deployment over time while monitoring user access and security policies.
Why does the zero trust roadmap start with identity, not the network?
Identity is where the majority of breaches begin: credential theft, password spray attacks, and compromised service accounts account for most initial access events. Identity controls also deliver immediate, measurable security value before any network changes are made. Architecturally, every downstream zero trust control (device compliance, conditional access, ZTNA policies) references identity as its primary input, making identity the logical foundation.
What is the CISA zero trust maturity model?
The CISA Zero Trust Maturity Model defines four maturity levels — Traditional, Initial, Advanced, and Optimal — across the five zero trust pillars. Most organizations beginning implementation are at the Traditional level. Reaching Advanced across all pillars is a realistic 2–3 year goal with committed resources. The model provides a structured way to assess where you are, prioritize investments, and demonstrate progress to leadership and auditors.
How do I build a business case for a zero trust roadmap?
Frame the investment across three dimensions: risk reduction (fewer breaches, smaller blast radius), operational efficiency (automated policy management, streamlined access reviews), and regulatory compliance (NIST 800-207, CMMC, HIPAA alignment). The IBM Cost of a Data Breach Report found that mature zero trust deployments save an average of $1.73 million per breach for most organizations, that figure alone justifies the program cost.
Can stages of the zero trust roadmap run in parallel?
Yes, partially. Stages 2 (device trust) and 3 (application access) can run concurrently because they are independent of each other. However, Stage 1 (identity foundation) must be substantially complete before Stage 3 begins, since ZTNA access policies reference identity as their primary input. Stage 4 (network segmentation) requires the visibility and traffic mapping built in earlier stages and should not be started prematurely.
What does zero trust maturity look like at the Advanced level?
At the Advanced maturity level, policy management is largely automated rather than manual, access decisions incorporate behavioral risk signals beyond just identity and device compliance, monitoring is continuous and correlated across all five pillars, and compliance reporting is generated automatically from existing security telemetry rather than assembled manually for audits.
