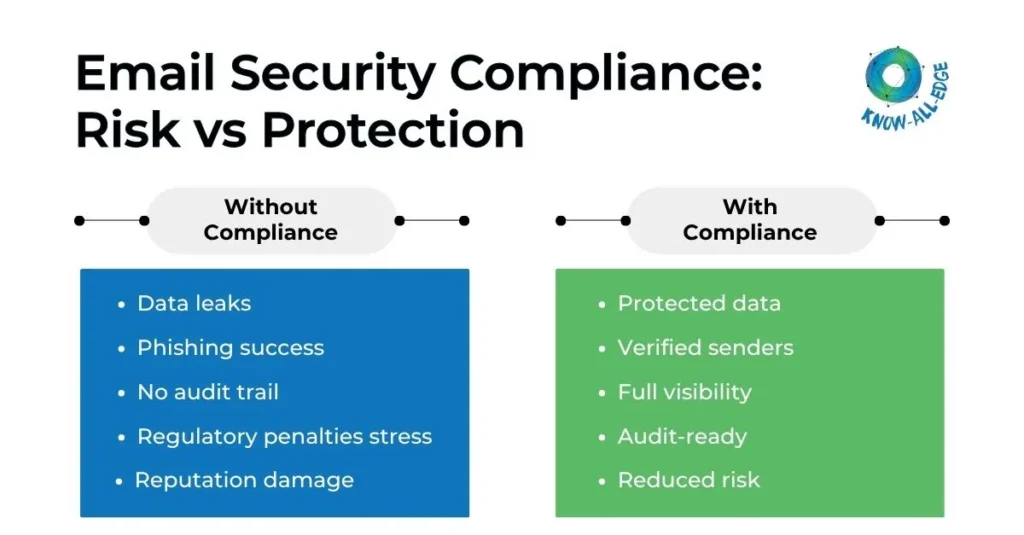
If you are managing a growing organization, handling hundreds of thousands of emails every year, and somewhere in the back of your mind, there is always that one question: are we actually compliant? Because when it comes to email security compliance, “we think so” is simply not good enough anymore.
Email is still the most used communication channel in any organization. It carries contracts, financial data, customer information, and internal discussions. That makes it both critical and risky at the same time.
Email security compliance nowadays is not just about passing audits. It is about reducing real business risk. Regulations are tightening, threats are getting smarter, and the margin for error is shrinking fast.
This blog breaks down ‘what is email security compliance’, ‘why it has become so critical in 2026’, and ‘what practical steps organizations can take to strengthen their position’.
What Is Email Security Compliance?
Email security compliance refers to how well an organization meets regulatory and internal requirements for protecting email data. This includes how emails are stored, transmitted, accessed, and secured.
It is not just one control or one tool. It is a combination of policies, technologies, and processes working together.
To stay compliant, organizations typically need to:
- Protect sensitive email data using encryption
- Ensure proper authentication of senders and domains
- Retain email records for defined time periods
- Maintain audit trails of access and activity
- Prevent data leaks through outbound monitoring
Different industries are governed by different frameworks. Healthcare organizations must align with HIPAA. Financial firms deal with FINRA, MiFID II, and SEC rules. Companies handling EU resident data must follow GDPR.
Indian organizations must comply with the DPDP and IT Acts, ensuring secure handling of personal data shared via email. And with regulations like NIS2, DORA, and AI oversight laws now firmly in effect across multiple regions, the compliance landscape in 2026 is more demanding than ever.
It needs the right tools, clear email security policies, and a security culture that runs from the boardroom all the way to the service desk.
Also read: Email Security Guide: Protecting Your Organization from Modern Email Threats
Why Email Security Compliance Is So Critical in 2026
The numbers make a compelling case. As per Market Research Future, the global email security market is projected to grow from $6.83 billion in 2025 to $23.37 billion by 2035. That kind of investment reflects the scale of the problem.
And the threat environment in 2026 explains the urgency. As per Kaspersky reports, 45% of global email traffic in 2025 was spam, with malicious email threats rising by 15% year over year.
The most damaging and hardest-to-detect threats organizations face are:
- Business email compromise,
- AI-generated phishing
- Deepfake-based impersonation attacks
This convergence of threat and regulation means there is no comfortable middle ground. You either have a structured, enforceable email security compliance programme, or you are exposed.
Email Security Compliance Examples Across Industries
Understanding compliance in the abstract is one thing. Seeing how it plays out in practice makes it easier to identify what your organization actually needs.
Healthcare (HIPAA/HITECH)
- Emails containing protected health information (PHI) must be encrypted in transit and at rest.
- Access controls must be in place.
- Audit logs must show who accessed what and when.
A single unencrypted email with patient data sent to the wrong recipient can trigger a federal investigation. Financial institutions that serve healthcare clients can also become HIPAA business associates without realizing it, which brings its own compliance obligations.
Financial Services (FINRA, SEC, MiFID II)
Banks and financial institutions operate under strict communication rules.
- All business emails must be archived
- Records must be stored in non-editable formats
- Communications may require supervisory review
For example: Under SEC Rule 204-2, registered investment advisors must maintain client communications, including off-channel emails, for no less than five years, with the most recent two years immediately accessible. FINRA Rule 4511 requires records to be preserved in WORM (write once, read many) format for a minimum of six years.
SaaS and Technology Companies
These companies often handle global customer data.
- Must comply with GDPR if serving EU users
- Need strong authentication to prevent spoofing
- Must detect and prevent data leaks
Even one phishing attack can expose thousands of users.
India (DPDP and Sector Regulations)
Organizations in India must ensure that personal data shared via email is protected under the DPDP Act. In regulated sectors like banking and financial services, guidelines from RBI and SEBI also require secure communication, audit trails, and controlled access to email records.
All Industries (GDPR, CCPA)
Any organization handling data belonging to EU residents must protect that data in email, obtain proper consent, and report breaches within 72 hours.
CCPA adds similar obligations for California residents. Both laws apply based on where your customers are located, not where your organization is based.
New in 2026 – AI Oversight Laws
A fast-emerging area of compliance involves AI-generated email. Organizations using AI to draft or send emails at scale are now expected to apply explicit labelling, maintain human review processes, and keep logged records of AI-generated content. This is not optional in jurisdictions where AI transparency laws are in effect.
These examples show that email security compliance is not a single standard. It is a layered set of obligations that vary by sector, geography, and how your organization uses technology.
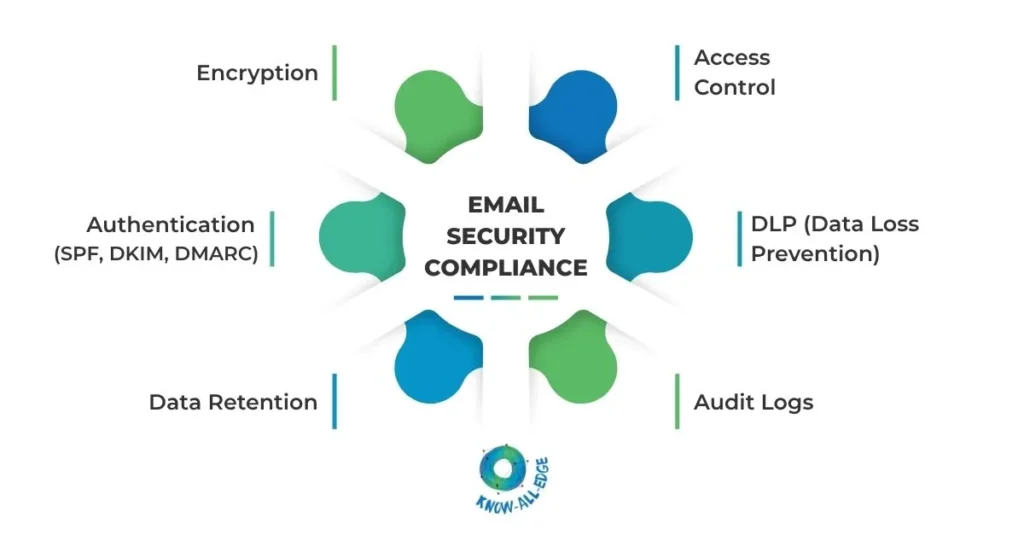
The Building Blocks of a Strong Email Security Compliance Program
Getting compliant, and staying compliant, requires more than a single tool or a written policy. It demands a coordinated approach across several areas.
1. Email Authentication Protocols
SPF, DKIM, and DMARC form the foundational layer of email authentication.
- SPF tells receiving servers which IP addresses are authorized to send email on your behalf.
- DKIM adds a cryptographic signature to outgoing messages.
- DMARC ties them together and tells servers what to do when authentication fails.
Beyond these three, newer protocols like Authenticated Received Chain (ARC) are gaining traction to handle complex mail flows where forwarded emails might otherwise fail authentication checks.
Without proper authentication, your domain is vulnerable to spoofing. Attackers can send emails that appear to come from your organization and use them to defraud customers, partners, or your own employees.
2. Encryption
Emails containing sensitive data must be encrypted. TLS handles encryption in transit between servers. S/MIME or PGP can be used for end-to-end encryption where required by regulation.
For regulated industries, encryption is a baseline compliance requirement under GDPR, HIPAA, and PCI DSS.
3. Email Archiving and Retention
A compliant system must store emails securely for defined periods. These vary by framework. For example, financial records may need to be held for five to seven years, and healthcare communications should be held for six years.
A proper archiving solution should store records in an immutable format, allow fast and accurate search, and support legal export when records are required for an investigation or audit.
There are many modern email security solutions that offer cloud-based archiving that is scalable and easy to manage.
4. Data Loss Prevention (DLP)
A strong email security policy must include controls that stop sensitive data from leaving the organization unintentionally. DLP tools scan outbound emails for patterns matching credit card numbers, personal health information, or other regulated data, and either block or flag them before delivery.
As insider risk grows, outbound DLP is getting more attention from compliance teams and regulators alike.
5. Access Controls and Audit Logging
Knowing who accessed what is fundamental to any compliance posture. Role-based access controls ensure that only authorized individuals can view archived email records or sensitive information.
Detailed audit logs create an evidence trail that can withstand scrutiny during a regulatory review or legal proceeding.
6. Employee Awareness and Training
This is consistently underestimated. As per Zivver Email Security Trends Report covering 400 IT decision-makers and 2,000 employees, 73% of staff are aware of their organization’s email security policies, but only 52% actually follow them.
That gap is dangerous. Training must be continuous, contextual, and directly tied to real behavioral change. Annual refreshers alone are not enough in an environment where AI-generated phishing emails now closely mimic executive writing styles.
Email Security Tools and Solutions
The market for email security solutions has matured considerably, and so has what organizations expect from a platform. When evaluating tools, the key is finding solutions that bring together multiple capabilities rather than requiring your team to manage five separate products.
Look for solutions that offer:
- Threat detection for phishing, malware, and impersonation
- Built-in email authentication management
- Cloud-native archiving and backup
- DLP integration
- eDiscovery and legal hold capabilities
- Real-time compliance dashboards
Modern email security tools are moving towards API-based integration instead of traditional gateways.
Building and Enforcing an Email Security Policy
An email security policy is the governance document that ties everything together. It defines acceptable use, required security behaviors, data handling rules, and the consequences of violations. Without it, even good technology becomes hard to enforce.
A strong policy should clearly define:
- Who can send emails on behalf of the organization
- What type of data can be shared over email
- When encryption is mandatory
- How long emails must be retained
- How to report suspicious emails
It must be supported by technical controls, communicated clearly to every team, and reviewed at least annually to stay current with changes in regulation and the threat landscape.
Final Verdict
Email security compliance is not a project you finish. It is an ongoing responsibility that demands the right combination of technology, policy, and people working together, consistently.
Currently, the challenge is not just keeping pace with regulations. It is building a compliance posture that is resilient enough to handle what comes next-
- whether that is a new enforcement mandate,
- a more sophisticated attack vector,
- or an AI-generated threat that bypasses traditional filters.
For this, we are here to help organizations like yours implement email security solutions end to end, aligning with global standards as well as Indian compliance requirements and sector-specific guidelines. We work with leading platforms to design, deploy, and manage the right combination of tools for your industry, your risk profile, and your compliance obligations.
If you are ready to build an email security compliance posture, let’s start a conversation.
FAQs on Email Security Compliance
How long should organizations retain emails for compliance purposes?
Retention depends on the regulation and industry.
- SEC requires up to 5 years of retention
- FINRA mandates 6 years in WORM format
- HIPAA requires 6 years for healthcare data
- GDPR follows a “retain only as needed” approach
The best approach is to map requirements to your business and automate retention using a centralized archiving system.
What is the difference between email security and email compliance?
Email security focuses on protecting email systems and data from threats like phishing, malware, and unauthorized access. Email compliance refers to meeting the regulatory, legal, and policy requirements that govern how email data is handled, stored, and protected.
The two are closely linked. Strong security supports compliance, and managing both together avoids gaps and duplication of effort.
Does email encryption make an organization fully compliant?
No. Encryption is an important part of email security compliance, but it covers only one layer of a much larger set of requirements. Organizations also need authentication (SPF, DKIM, DMARC), archiving, access controls, DLP, and audit logging. Encryption helps, but it does not cover retention, monitoring, or reporting requirements.
What are the financial penalties for email compliance failures in 2026?
Penalties can be significant, especially with stricter enforcement in India and globally.
- In India, under the IT Act and DPDP Act, penalties can go up to ₹250 crore for data protection failures
- GDPR fines can reach €20 million or 4% of global revenue
- HIPAA penalties can go up to $1.9 million annually
- CAN-SPAM fines apply per non-compliant email
Beyond fines, organizations also face reputational damage, customer trust loss, and investigation costs.
How often should an email security compliance audit be conducted?
At least once a year, but more frequent reviews are recommended.
- Quarterly internal checks help catch gaps early
- Annual third-party audits add validation
- Major changes like migrations should trigger reviews
Regular audits ensure controls are working, not just documented.
