The traditional network perimeter is disappearing.
Applications now run across cloud platforms, SaaS services, and hybrid environments. Employees connect from home networks, airports, and personal devices. Vendors and contractors need access to internal systems. In this reality, the old assumption that users inside the network can be trusted no longer holds.
This is why many organizations are moving toward Zero Trust architecture.
Zero Trust changes the security model by assuming that no user, device, or application should be trusted by default-even if it originates from inside the corporate network. Instead, every access request must be verified based on identity, device posture, and contextual risk.
A key technology enabling this model is Zero Trust Network Access (ZTNA), which provides secure, identity-based access to applications without exposing internal networks.
If you’re evaluating secure access strategies, our comparison of ZTNA vs VPN explains why many enterprises are replacing traditional VPN architectures.
What is Zero Trust Architecture?
Zero Trust architecture is a security framework that enforces strict identity verification and least-privilege access for every connection to enterprise resources.
In a zero trust security architecture, access decisions are based on multiple signals such as:
- User identity
- Device posture
- Location and context
- Application sensitivity
- Risk indicators
Rather than granting broad network access, Zero Trust ensures users only receive access to the specific resources they are authorized to use.
ZTNA is often the enforcement mechanism that implements this model for application access. It acts as a secure intermediary between users and applications.
This is why discussions around ZTNA architecture are central to modern Zero Trust deployments.
Core Principles of Zero Trust Architecture
A well-designed zero trust network architecture follows several core principles.
Verify Explicitly
Every access request must be authenticated and authorized using identity, device posture, and contextual signals.
Least Privilege Access
Users receive access only to the resources they require to perform their tasks.
Assume Breach
Security architectures should assume attackers may already be inside the network. This requires minimizing lateral movement opportunities.
Continuous Verification
Access is not granted once and trusted indefinitely. Access decisions are continuously evaluated throughout the session.
These principles guide the design of Zero Trust network access architecture.
Components of ZTNA Architecture
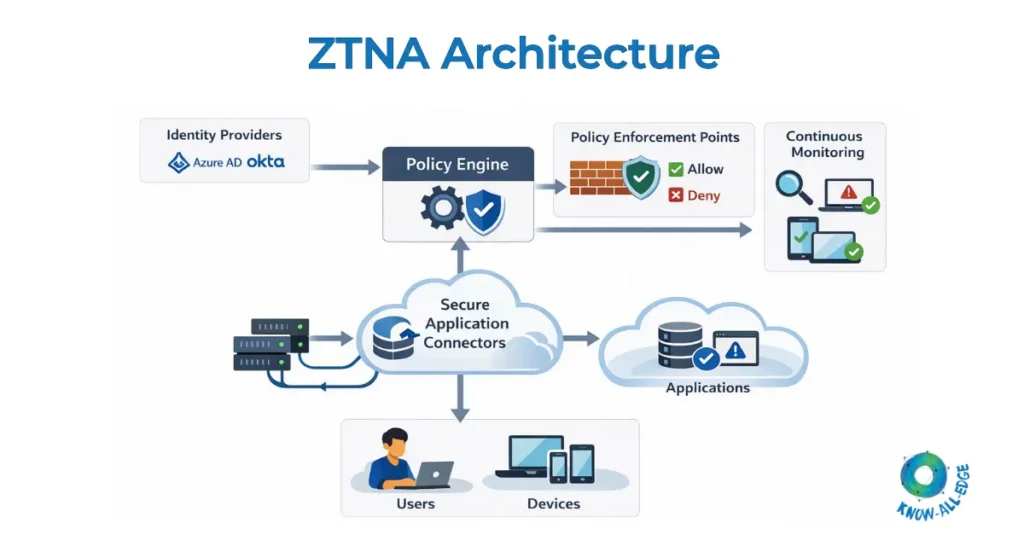
A typical ZTNA architecture includes several key components that work together to enforce Zero Trust access policies.
(1) Identity Provider: The identity provider authenticates users before they access applications. Examples include:
- Microsoft Entra ID
- Okta
- Google Identity
(2) Device Posture Verification: ZTNA platforms evaluate whether a device meets security requirements before granting access. Checks may include:
- Endpoint security status
- Operating system version
- Device compliance policies
(3) Policy Engine: The policy engine evaluates access requests using predefined security policies. Policies may consider:
- User identity
- Device trust level
- Location
- Application sensitivity
(4) Policy Enforcement Point: This component enforces the decision made by the policy engine, allowing or blocking access.
(5) Application Connectors: Secure connectors create outbound connections from internal applications to the ZTNA platform, ensuring applications are never directly exposed to the internet.
Also read: ZTNA Components: The Building Blocks of Secure Zero Trust Access
Identity Provider Integration
Identity plays a central role in Zero Trust architecture.
ZTNA platforms integrate with enterprise identity providers to authenticate users before granting access to applications.
Common integrations include:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Identity federation
Identity-based access ensures that security decisions are tied to who the user is, rather than where they are connecting from.
This approach significantly reduces reliance on network-based trust.
Policy Engine
The policy engine acts as the decision-making brain of ZTNA architecture.
When a user attempts to access an application, the policy engine evaluates the request against security policies.
For example:
- Is the user authenticated through MFA?
- Is the device compliant with security policies?
- Is the request coming from an unusual location?
Only when all policy conditions are satisfied does the system grant access.
Secure Access Broker
The secure access broker sits between users and applications.
Instead of allowing direct connections to internal resources, the broker mediates every request.
This provides several security benefits:
- Internal applications remain hidden from the internet
- Attackers cannot directly scan internal services
- Access can be tightly controlled at the application level
This broker model is one of the core differences between ZTNA and traditional VPN architectures.
Traffic Flow in ZTNA
Understanding traffic flow is critical to understanding ZTNA architecture.
A typical connection works like this:
- A user attempts to access an application.
- The request is routed through the ZTNA access broker.
- The user is authenticated through the identity provider.
- Device posture is evaluated.
- The policy engine evaluates the access request.
- If approved, a secure connection is established between the user and the application.
Importantly, the application itself remains hidden behind the ZTNA platform.
This reduces the attack surface significantly compared to traditional remote access architectures.
ZTNA Deployment Models
Organizations can deploy zero trust network access architecture in several ways.
Cloud-Delivered ZTNA
Most modern ZTNA solutions are delivered as cloud services.
Advantages include:
- Scalability
- Global access points
- Reduced infrastructure overhead
Hybrid ZTNA
Some organizations combine cloud-based ZTNA with on-premise connectors to support legacy applications.
Private ZTNA
Large enterprises with strict compliance requirements may deploy ZTNA platforms within private infrastructure.
Each model depends on factors such as application location, compliance requirements, and network architecture.
Architecture Best Practices
Implementing Zero Trust architecture requires careful planning.
Security leaders often follow several best practices.
(1) Start with High-Risk Applications: Begin by protecting sensitive applications before expanding coverage across the environment.
(2) Integrate Identity and Device Security: Strong identity verification and endpoint security are essential for Zero Trust access.
(3) Reduce Network-Level Access: Shift from network-based access controls to application-level access wherever possible.
(4) Monitor and Analyze Access Patterns: Continuous monitoring helps detect anomalies and potential threats.
Organizations pursuing Zero Trust strategies often combine ZTNA with other security technologies such as SWG, CASB, and endpoint security platforms.
If you’re exploring the broader evolution of secure access models, our guide on Traditional ZTNA vs Universal ZTNA explains how these architectures are evolving.
Conclusion
The move toward Zero Trust architecture represents a fundamental shift in how organizations secure access to applications and services.
Rather than relying on network perimeters, Zero Trust architectures enforce identity-based access and continuous verification for every connection.
ZTNA plays a critical role in implementing this model by providing secure, application-level access without exposing internal networks.
For organizations navigating hybrid environments, cloud platforms, and distributed workforces, designing the right ZTNA architecture is an essential step toward building a resilient security strategy.
Designing Zero Trust architecture for secure application access?
Know All Edge works with organizations to build and implement robust ZTNA architectures aligned with their security and compliance requirements. Connect with our experts to plan your ZTNA deployment.
Frequently Asked Questions
What is Zero Trust architecture?
Zero Trust architecture is a security framework that requires continuous verification of users, devices, and access requests before granting access to resources.
What is ZTNA architecture?
ZTNA architecture refers to the infrastructure and components that enforce Zero Trust Network Access policies, including identity providers, policy engines, and secure access brokers.
How does Zero Trust architecture work?
Zero Trust architecture works by verifying identity, device posture, and contextual signals before granting access to specific applications instead of granting network-level access.
What is an example of Zero Trust architecture?
A typical Zero Trust architecture example involves users accessing applications through a ZTNA broker that verifies identity through an identity provider and enforces policy-based access controls.
Is Zero Trust architecture the same as ZTNA?
ZTNA is one of the technologies used to implement Zero Trust architecture. While Zero Trust is a security strategy, ZTNA is the mechanism that enforces secure access to applications.
Does Zero Trust architecture replace VPN?
In many environments, ZTNA-based Zero Trust architectures can replace VPN for application access. However, some legacy environments may still require VPN connectivity.
