Key Takeaways
- DSPM vs CSPM focuses on different areas- CSPM secures cloud infrastructure, while DSPM secures sensitive data.
- The difference between DSPM and CSPM is that CSPM identifies configuration issues, while DSPM helps understand what data exists and who can access it.
- CSPM is important for maintaining cloud security hygiene, while DSPM is used for managing data risk and governance.
- Using both DSPM and CSPM helps organizations identify and prioritize security risks more effectively.
Introduction
Cloud adoption has fundamentally changed how organizations build and scale systems. But it has also introduced a new class of security challenges. Data is now distributed across cloud platforms, SaaS applications, and internal systems, often without consistent visibility or control.
To manage this complexity, security teams are investing in multiple tools. Two of the most commonly discussed are Cloud Security Posture Management (CSPM) and Data Security Posture Management (DSPM).
These both operate at very different layers of the stack.
This blog explains:
- What is the difference between DSPM and CSPM?
- How do they fit into your overall security strategy?
- How do they work together?
Let’s understand this in detail.
What is CSPM?
CSPM focuses on securing cloud infrastructure by identifying and remediating misconfigurations.
It provides continuous visibility into cloud environments such as AWS, Azure, and GCP, and evaluates configurations against security benchmarks and compliance frameworks.
Typical CSPM capabilities include:
- Detecting publicly exposed storage resources
- Identifying overly permissive IAM policies
- Ensuring encryption settings are enforced
- Monitoring compliance with standards like CIS benchmarks
CSPM plays a foundational role in reducing the attack surface. But it is still limited to infrastructure-level insights.
Why CSPM Alone Is Not Enough for Modern Data Risk
As discussed above, security teams use CSPM to continuously monitor cloud environments for issues like overly permissive IAM roles, publicly exposed storage, or disabled encryption.
Below are some statistics which tells that the scale of this problem is significant.
- 60% of organizations report at least one misconfiguration-related incident every year.
- 70% of cloud environments have at least one publicly exposed resource.
These are not edge cases. They are operational realities in most cloud environments.
However, CSPM operates at the infrastructure layer. It tells you where the exposure exists, but not what is exposed. This distinction matters.
Two misconfigured storage buckets may trigger identical alerts. But from a risk standpoint, they are not equal. One may contain non-sensitive test data, while the other holds regulated customer records.
Without knowing what type of data it is, prioritization becomes inefficient. Security teams end up treating configuration issues uniformly, even when the actual business impact is very different.
This gap between infrastructure visibility and data context is exactly where DSPM comes into play.
What is DSPM?
Data Security Posture Management (DSPM) operates at the data layer. It provides visibility into sensitive data across cloud storage, databases, SaaS platforms, and data lakes.
DSPM tells you:
- Where is sensitive data located?
- What type of data is it?
- Who has access to it?
- Is that access justified?
Knowing about your organization’s data is important because most breaches today are data-centric.
According to IBM’s 2025 report, 72% of data breaches involve data stored in cloud environments.
This reinforces a key point: securing infrastructure alone does not reduce data risk.
DSPM addresses this gap by continuously discovering, classifying, and monitoring sensitive data across environments.
DSPM vs CSPM: Key Differences
Understanding the distinction between DSPM and CSPM requires looking at how each of them defines and prioritizes risk. While both operate in cloud environments, they answer fundamentally different questions.
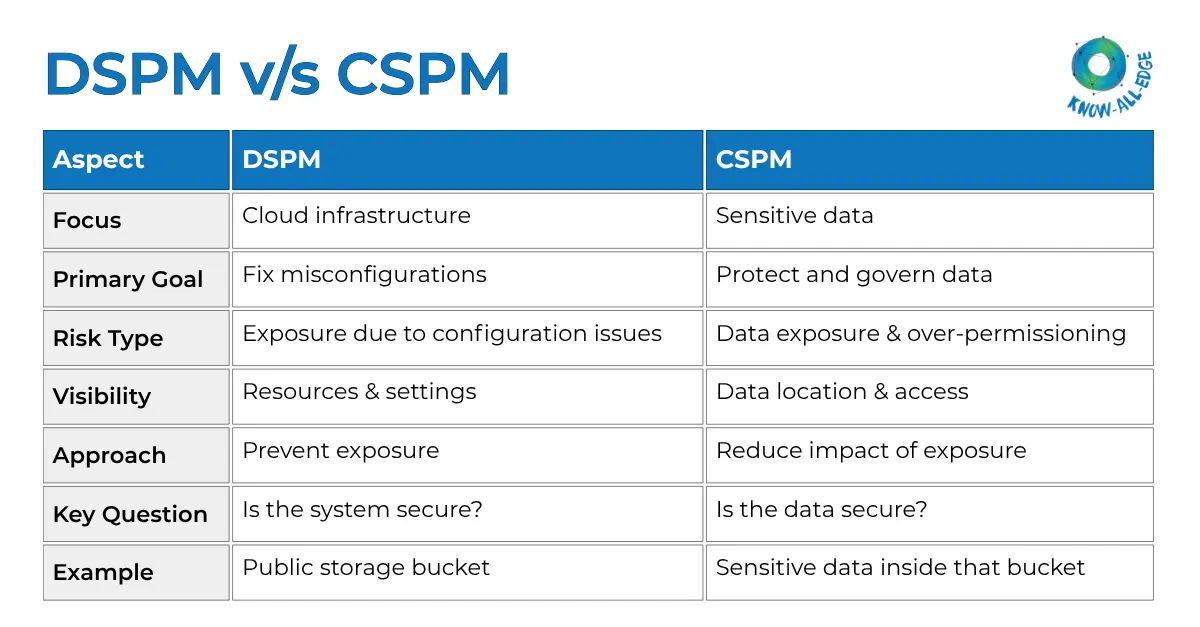
Focus Area
CSPM is focused on securing cloud infrastructure. It looks at configurations, permissions, network exposure, and overall cloud resource hygiene. Its goal is to ensure that the environment itself is not misconfigured in a way that could lead to exposure.
DSPM, on the other hand, is focused on securing data within that infrastructure. It identifies where sensitive data resides, how it is classified, and whether it is being accessed appropriately.
Risk Model
CSPM operates on a configuration-driven risk model. It flags deviations from best practices, such as publicly exposed storage, weak IAM policies, or missing encryption. These are structural risks that increase the likelihood of a breach.
DSPM operates on a data-centric risk model. It evaluates risk based on:
- Sensitivity of data (PII, financial, health, IP)
- Volume and spread of that data
- Who has access and whether that access is justified
This means DSPM helps identify risks like:
- Sensitive data stored in low-security environments
- Excessive access permissions
- Data sprawl across unmanaged systems
Visibility
CSPM provides visibility into cloud resources and their configurations. It shows what services are running, how they are exposed, and whether they comply with security policies.
DSPM provides visibility into data itself. It tells:
- Where sensitive data exists
- How it is distributed across systems
- Who is accessing it and how frequently
Security Approach
CSPM takes a preventive approach. It aims to reduce the chances of a security incident by ensuring that infrastructure is configured correctly.
DSPM takes a risk-reduction approach. It assumes that exposure may happen and focuses on minimizing the impact by:
- Reducing unnecessary data access
- Limiting sensitive data spread
- Ensuring proper classification and governance
Together, they address both probability and impact, which is essential for a complete risk strategy.
Practical Example
Consider a cloud storage bucket that is publicly accessible.
- CSPM will flag this as a misconfiguration because public access increases exposure risk.
- DSPM will analyze the contents of the bucket and determine whether it contains sensitive data such as customer records, financial information, or internal documents.
If the bucket contains non-sensitive data, the risk is relatively low. If it contains regulated data, the risk becomes critical.
This is the difference between a generic alert and a prioritized, actionable risk.
As security architectures evolve, this comparison is often extended beyond just DSPM vs. CSPM. Many organizations today are also evaluating SaaS Security Posture Management (SSPM), especially as critical workflows move to SaaS platforms like Microsoft 365, Salesforce, and Slack.
Together, these three layers provide a more complete view of risk across infrastructure, data, and SaaS environments. To understand how they compare in more detail, you can explore DSPM vs CSPM vs SSPM.
Where DSPM Needs CSPM
DSPM provides deep visibility into sensitive data, but it does not eliminate infrastructure risk.
If cloud resources are misconfigured, sensitive data remains exposed regardless of classification.
For example:
- A database with PII may still be publicly accessible
- IAM roles may allow excessive access
- Encryption policies may not be enforced
These are CSPM problems. DSPM and CSPM address different layers of the same risk surface. One without the other leaves blind spots.
How DSPM and CSPM Work Together
The real value emerges when DSPM and CSPM are used together to provide both infrastructure and data context.
Individually, each tool highlights a part of the problem. Combined, they provide a complete view of risk.
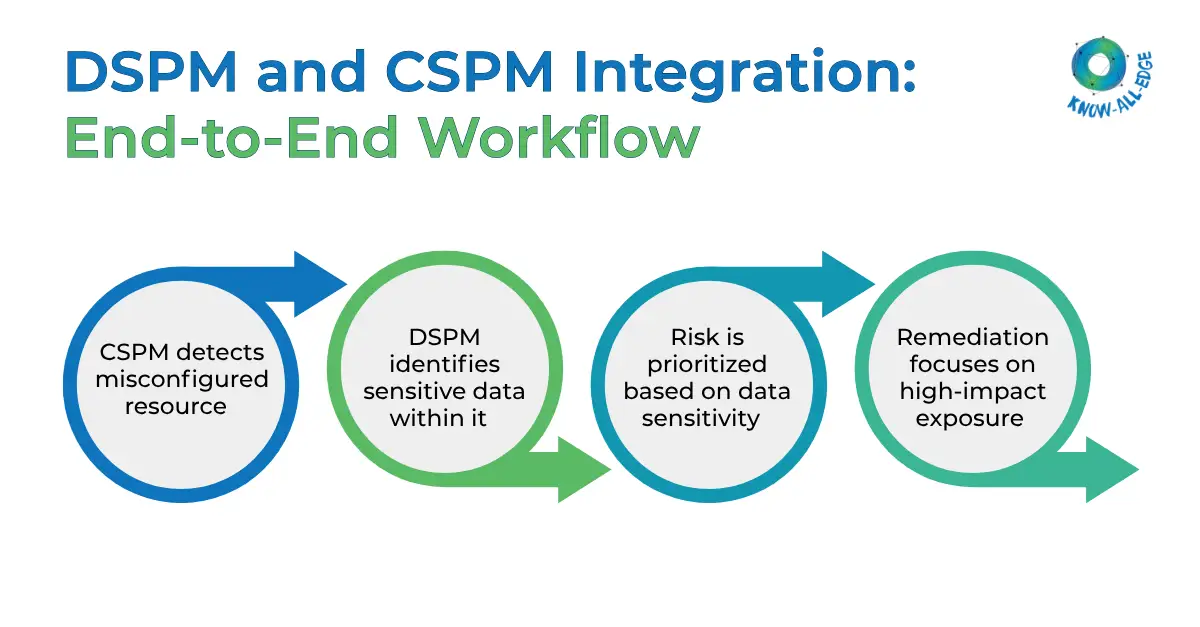
What This Combined Model Enables
When CSPM and DSPM are integrated, security operations become significantly more effective.
- Risk-based prioritization: Instead of treating all misconfigurations equally, teams can focus on issues that involve sensitive data.
- Faster remediation: Clear context reduces analysis time, allowing teams to act quickly on critical risks.
- Reduced alert fatigue: By filtering out low-impact alerts, teams avoid being overwhelmed and can focus on meaningful threats.
- Better alignment with business impact: Security decisions are no longer based solely on technical misconfigurations, but on the actual risk to business-critical data.
DSPM vs CSPM in AI and Data-Driven Environments
AI systems are significantly increasing both the volume and velocity of data usage across organizations. From model training to real-time inference, data is being accessed, processed, and reused at scale.
At the same time, the risk surface is expanding.
By 2027, over 40% of AI-related data breaches are expected to result from improper use of generative AI.
These trends highlight a clear gap between AI adoption and data security readiness.
CSPM ensures that the infrastructure supporting AI systems is securely configured and not exposed due to misconfigurations.
DSPM in AI focuses on governing the data layer, ensuring that sensitive or regulated data is not unintentionally used in training datasets, fine-tuning processes, or inference pipelines.
Without both layers in place, organizations risk scaling AI adoption on top of poorly governed data, increasing exposure instead of delivering value.
DSPM vs CSPM for Compliance
Modern compliance frameworks require both infrastructure security and data governance.
- CSPM supports configuration compliance (CIS benchmarks, cloud policies).
- DSPM supports data-centric regulations (DPDP Act, GDPR).
Check out out blog on how DSPM helps with DPDP Act compliance.
Regulators increasingly expect organizations to demonstrate:
- Data inventory and classification
- Access governance
- Usage control
DSPM provides this visibility. CSPM ensures the environment is secure. Together, they create a defensible compliance posture.
When Do You Need DSPM, CSPM, or Both?
In practice, the choice is not about replacing one with the other. It is about aligning the right capability to the right risk layer.
Use CSPM when your priority is infrastructure security and misconfiguration management.
This includes securing cloud resources, identifying configuration drift, enforcing policies, and maintaining compliance across AWS, Azure, or GCP environments. CSPM is your first line of defense against exposure caused by misconfigured systems.
Use DSPM when your priority is data visibility, classification, and access governance.
Typical DSPM use cases include discovering sensitive data across cloud and SaaS environments, classifying PII or financial data, identifying over-permissioned access, and reducing data sprawl. It is especially relevant when you need to understand where critical data resides and how it is being used.
Use both when:
- You operate in multi-cloud environments
- You handle sensitive or regulated data
- You are building AI or data-driven systems
- You need risk prioritization based on data sensitivity, not just configuration issues
For most enterprise environments today, this is already the case. Infrastructure and data risks are tightly connected, and addressing one without the other leaves gaps in your security posture.
Conclusion
DSPM and CSPM are not interchangeable. They address different layers of risk.
- CSPM secures the infrastructure where your data resides.
- DSPM secures the data itself- its sensitivity, access, and usage.
In modern cloud and AI-driven environments, both are required to build an effective security framework.
Organizations that align these capabilities can move beyond reactive security and toward a more precise, risk-driven approach to protection and compliance.
If you are looking to implement DSPM in your environment, our team can help you assess your current data security posture and guide you on the right approach.
FAQs on DSPM vs CSPM
How does DSPM differ from Cloud Security Posture Management (CSPM)?
DSPM helps you understand where your sensitive data is and who can access it. CSPM helps you find and fix security issues in your cloud setup.
Can CSPM replace DSPM?
No. CSPM does not provide visibility into sensitive data, which is essential for risk prioritization.
Do organizations need both DSPM and CSPM?
Yes. Most modern environments require both infrastructure and data-level security.
What is CSPM and SSPM?
CSPM focuses on securing cloud infrastructure and fixing misconfigurations. SSPM focuses on securing SaaS apps by managing settings, access, and risks.
