Data has shifted from being just an operational asset to becoming the primary attack surface. Whether it’s ransomware, insider threats, or misconfigured cloud storage, attackers don’t need to break in; they exploit what’s already exposed.
Yet most organizations still struggle with a fundamental question: Where is our sensitive data, and is it actually secure? Without a clear answer, even the most advanced security stack leaves critical gaps.
This is exactly where DSPM use cases come in.
What Is DSPM and Why It’s Important Now
Data Security Posture Management (DSPM) provides continuous, automated visibility into sensitive data across cloud and hybrid environments. It shows where data resides, who can access it, how it moves, and whether it is properly secured. As defined by Gartner, DSPM delivers visibility into data location, access, usage, and overall security posture.
The urgency around DSPM is growing fast.
According to IBM’s 2024 Cost of a Data Breach Report, the average breach now costs $4.88 million globally. It’s a sharp increase and the highest jump since the pandemic. At the same time, Frost & Sullivan projects the DSPM market to grow at a 37.4% CAGR through 2029, signaling rapid enterprise adoption.
The root problem is clear: lack of visibility. A 2024 DSPM adoption survey found that 83% of security leaders cite limited data visibility as a key reason for weak security posture. Simply put, you can’t secure what you can’t see.
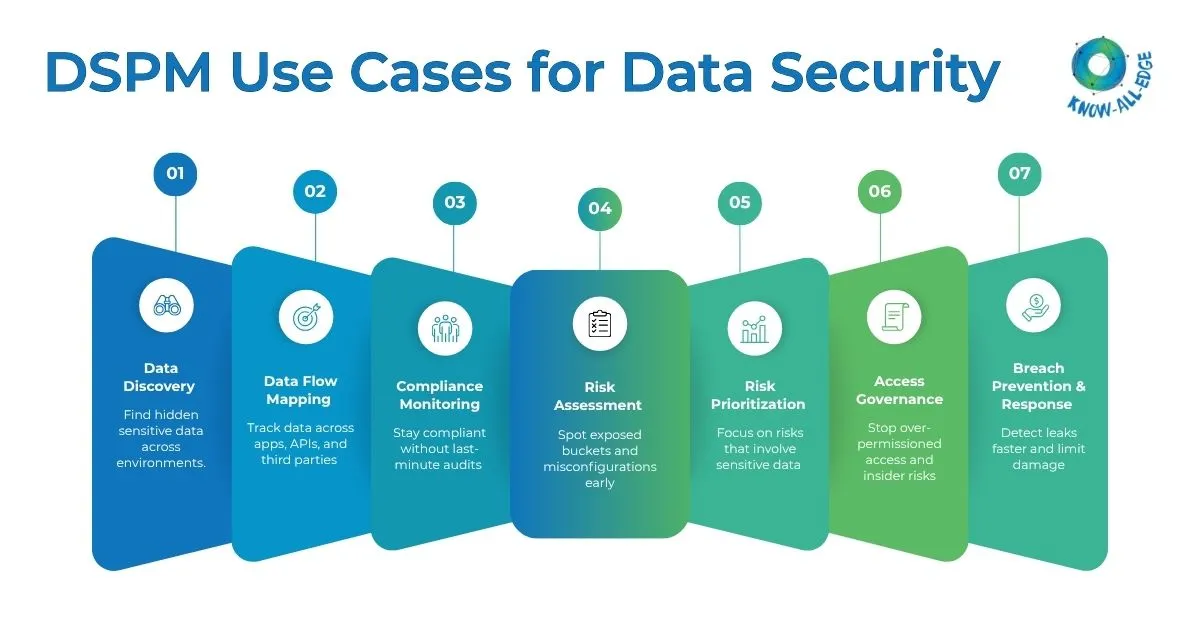
The following sections outline what are the use cases for DSPM, breaking down seven real-world scenarios where it solves critical data security challenges.
DSPM Use Cases: 7 Real-World Scenarios
From unknown data exposure to compliance risks and AI-driven threats, these DSPM use cases highlight where DSPM delivers immediate impact.
(1) You Don’t Know What You Have: Data Discovery and Classification Fixes That
One of the most common problems security teams face isn’t a sophisticated attack. It’s simply not knowing where sensitive data is stored. In large enterprises, data sprawls across dozens of cloud environments, SaaS platforms, and on-premises databases, and a surprising portion of it is unclassified, forgotten, or completely off the radar.
DSPM tools solve this with automated data discovery and classification. They continuously scan datastores – structured and unstructured, and apply sensitivity labels such as public, internal, confidential, or restricted. Beyond simple labeling, modern DSPM platforms use large language models (LLMs) to handle unstructured data like emails, PDFs, and collaboration tools where rules-based classification fails.
Regulatory alignment is built in. Data classified under GDPR, HIPAA, CCPA, or India’s DPDPA is automatically tagged accordingly, giving compliance and security teams a real-time inventory of where regulated data sits.
For industries like healthcare and financial services, where data classification has direct regulatory consequences, this isn’t a nice-to-have. It’s fundamental.
(2) Data Is Moving But Is Anyone Watching? Data Flow Mapping Answers That
Data rarely stays where it’s created. It flows between applications, crosses into third-party tools, and sometimes leaves the organization entirely without anyone noticing.
For security teams, this creates an enormous blind spot.
DSPM platforms address this through data flow mapping, analyzing actual payload data (not just logs) to visualize how sensitive information moves through systems in real time. When something unusual happens, a large batch of customer records moving to an unfamiliar endpoint, or PII suddenly appearing in a test environment, the system flags it immediately.
This matters especially in industries like fintech and e-commerce, where data pipelines are deeply interconnected. A misconfigured API could be quietly exfiltrating customer data for months before anyone notices. DSPM with runtime data flow visibility closes that window dramatically.
When a security team sees – which sensitive data moved, where it went, and who initiated the transfer, they can act decisively instead of spending days piecing together what happened.
(3) Compliance Isn’t a Once-a-Year Audit: Continuous Monitoring Makes It Manageable
For many compliance officers, the annual audit cycle is a fire drill. Teams scramble to generate reports, verify controls, and document practices that should have been monitored all year. The result is stress, gaps, and often costly violations.
DSPM reframes compliance as an ongoing process rather than a periodic event. These tools continuously monitor data handling practices against regulatory frameworks – GDPR, HIPAA, CCPA, PCI-DSS, and increasingly, India’s Digital Personal Data Protection Act (DPDPA), and generate automated audit reports on demand.
The DPDPA, enacted in 2023 and operationalized through the DPDP Rules 2025, represents a significant shift for organizations operating in or serving users in India. It requires demonstrable proof of data governance, not just policy documents.
DSPM closes that gap by providing live data maps, real-time access monitoring, and automated evidence collection that regulators can verify.
The financial stakes of non-compliance have never been higher. Regulatory fines, legal disputes, and post-breach remediation costs have pushed organizations to treat compliance infrastructure as a core security investment rather than an administrative overhead.
(4) You Can’t Fix What You Haven’t Found: Risk Assessment Across Cloud Environments
Cloud environments are dynamic by design. New buckets are spun up, permissions change, APIs get connected, and each of these events creates potential exposure. Static risk assessments done quarterly or annually simply cannot keep pace.
DSPM tools perform continuous risk assessment, scanning cloud storage, databases, SaaS applications, and developer environments to surface misconfigurations, excessive permissions, and unauthorized access patterns. They don’t just report on known datastores; advanced platforms use runtime capabilities to catch data in motion, including workloads that weren’t previously inventoried.
Consider a common scenario: A developer spins up an AWS S3 bucket for a new project, leaves it publicly accessible for a few hours to run tests, and forgets to lock it down. In that window, a scanner could index the bucket contents. A DSPM tool would flag this exposure in real time, before it becomes a news story.
(5) Too Many Alerts, Too Little Signal: Risk Prioritization Reduces Alert Fatigue
Security teams today are overwhelmed by the volume of alerts they need to manage. On any given day, they deal with:
- Cloud misconfiguration alerts
- Vulnerability scanner outputs
- SaaS permission warnings
- Threat intelligence signals
This often adds up to hundreds, or even thousands of alerts daily.
The result is a familiar problem: critical risks get buried in the noise, making it harder to identify what actually matters.
DSPM brings a data-centric lens to prioritization. Rather than treating every exposed resource equally, DSPM correlates risk signals with the actual sensitivity of the data involved.
An exposed S3 bucket containing public marketing assets is not the same risk as an exposed bucket containing employee health records. One needs to be noted; the other needs immediate remediation.
This is especially relevant for teams using third-party packages (like Maven or npm), where a flood of CVE alerts creates noise. DSPM cuts through this by showing which risks actually impact sensitive data in real environments.
The concept Gartner calls “toxic combinations”, where several individually manageable risks converge into a genuine attack path is something DSPM is uniquely equipped to identify. A misconfigured bucket plus excessive permissions plus AI training data access, for instance, is far more dangerous than any single issue on its own.
(6) Not Everyone Should See Everything: Data Access Governance Enforces That
The principle of least privilege sounds straightforward: give people access only to what they need. In practice, it erodes constantly. Permissions accumulate through promotions, project transfers, and forgotten access grants. Former employees sometimes retain access for weeks after their last day.
DSPM tools actively enforce data access governance by monitoring who is accessing sensitive data, when, and from where, and flagging anomalies in real time. This includes enforcing Zero Trust Data Protection (ZTDP) models, which verify every access request regardless of whether it originates from inside or outside the network perimeter.
As generative AI adoption accelerates, this use case has become even more critical.
Employees feeding sensitive customer data into public AI tools, like ChatGPT, Gemini, or similar represents a new and largely invisible data exposure vector. Microsoft’s Purview DSPM for AI is one example of platforms evolving to monitor these AI interactions and enforce data policies around them.
For organizations operating under the DPDPA, which mandates that data be used only for stated purposes and with proper consent, AI governance within a DSPM framework isn’t optional. It’s a requirement.
(7) When Something Goes Wrong, Speed Is Everything: Breach Prevention and Fast Response
Despite best efforts, incidents happen. The difference between a contained incident and a catastrophic breach often comes down to how quickly the organization detects and responds.
DSPM platforms with runtime capabilities enforce data policies based on actual, real-time data transfers. When anomalous behavior is detected, such as unusual data transfers, access from unfamiliar locations, or sensitive data appearing in unexpected environments, the system responds immediately.
It can automatically quarantine the data, revoke permissions, or alert response teams based on severity.
DSPM’s contribution here is two-fold.
- First, it reduces mean time to detect by providing contextual, data-aware alerts rather than infrastructure-level noise.
- Second, it reduces response time by giving teams instant clarity on affected data- no manual investigation is needed.
DSPM for AI: The Emerging Use Case Security Leaders Can’t Ignore
Beyond the seven core use cases above, a newer challenge is reshaping how organizations think about DSPM: generative AI adoption.
Organizations now manage an estimated 175 zettabytes of unstructured data, much of it flowing through AI tools and copilots that sit outside traditional security perimeters. Employees share proprietary documents with AI assistants. Developers use AI coding tools that may inadvertently expose API keys or credentials in model outputs. AI training pipelines pull from data sources that contain sensitive personal information.
DSPM for AI addresses this by extending discovery and classification to AI-specific workflows, monitoring what data enters AI systems, how it’s used, and whether it aligns with stated data governance policies. The EU AI Act’s Article 10 mandates that high-risk AI systems use properly governed training data; DSPM can automate the compliance evidence this requires.
This intersection of DSPM strategy and AI governance is where the next wave of adoption is concentrating.
The Bottom Line
The question is no longer whether organizations need to know where their sensitive data is. The question is how much longer they can afford not to. With breach costs at record highs, regulatory scrutiny intensifying across every major market, and AI adoption creating entirely new exposure vectors, DSPM strategies and DSPM best practices to implement these strategies have moved from optional to foundational.
Understanding the full range of DSPM use cases examples is the first step. Acting on them, through the right platform, the right implementation, and the right ongoing governance is what separates organizations that are genuinely secure from those that only believe they are.
Looking to implement DSPM and gain full visibility into your sensitive data? We can help.
Frequently Asked Questions
What are the use cases for DSPM?
DSPM helps with data discovery, flow tracking, compliance monitoring, risk assessment, alert prioritization, access control, and breach prevention, closing key data visibility gaps.
How does DSPM differ from traditional data loss prevention (DLP)?
DLP focuses on controlling data movement at the perimeter. DSPM provides continuous visibility into where sensitive data resides, how it’s exposed, and who can access it. The two are complementary.
Can DSPM help with India’s DPDPA compliance?
Yes. DSPM enables continuous data discovery, mapping, and monitoring, helping organizations demonstrate compliance with DPDPA requirements.
How? Check out in our blog: Decoding the DPDP Act: What Indian Enterprises Must Do and How DSPM Makes It Manageable
Is DSPM relevant for organizations that primarily use on-premises infrastructure?
Yes. DSPM is particularly valuable in hybrid environments, providing unified visibility across on-premises and cloud data stores.
How does DSPM address the risks of generative AI tools?
DSPM extends visibility to AI workflows, monitoring how sensitive data is used in AI systems, and helping enforce data governance and compliance controls.
