Data breaches bring regulatory fines, broken customer trust, and sometimes, years of legal battles. And yet, most organizations still don’t have a clear understanding of where their sensitive data is present, who has access to it, or whether it is being protected in the way it should be.
There’s a huge gap between what security teams think they know and what’s actually happening inside their cloud environments. This is exactly what makes data security and compliance risks with DSPM a critical conversation today.
According to IBM, the average cost of a data breach in India reached ₹220 million (approximately $2.6 million) in 2025.
Organizations with poor data visibility consistently paid more and took longer to respond.
The cloud has complicated data visibility more. Before cloud computing became the norm, your data more or less stayed in one place. Now it is scattered across AWS, Azure, Google Cloud, SaaS tools, containerized environments, and a dozen other services, often without anyone keeping track.
This is where DSPM, or Data Security Posture Management, comes in.
What Exactly Is DSPM and Why Is It Needed?
DSPM is a category of cybersecurity that understands data context at scale.
It clearly tells what organizations struggle with:
- Where is sensitive data stored right now
- Who has access to it, and should they
- How risky is that data in its current state
- Whether it complies with relevant regulations
Think of it as a live map of your data estate, one that flags risks in real time. That matters enormously when compliance frameworks like GDPR, HIPAA, PCI-DSS, and India’s newly enforced DPDPA demand not just that you protect data but that you can prove you are doing so, all the time.
DSPM strategies typically follow a four-step loop: discover, classify, assess risk, and remediate. What makes modern DSPM solutions especially valuable is automation. Instead of spending analyst hours manually cataloging data stores, DSPM does it continuously and at scale.
Can DSPM Help with Data Compliance?
Yes, but not in the way most vendors oversimplify it.
Different regulations have different definitions of sensitive data, different retention requirements, different access control expectations. Managing this across a multi-cloud environment, manually, is essentially impossible at scale.
DSPM solutions map discovered data directly against applicable regulatory obligations.
For example, regulations like GDPR, PCI-DSS, and HIPAA all require organizations to:
- Know what sensitive data they hold
- Limit access to authorized users
- Ensure proper storage and encryption
- Maintain audit trails
Here is how you can manage data security and compliance risks with DSPM support.
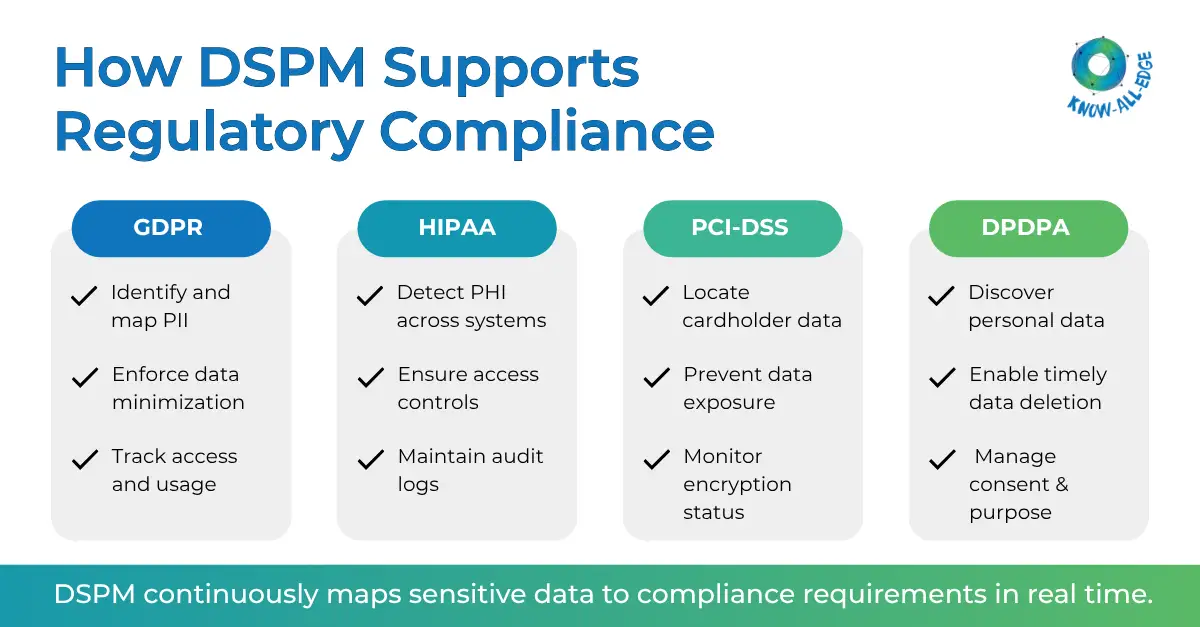
How DSPM Helps Manage Regulatory Compliance
You can reduce data security and compliance risks with DSPM by mapping sensitive data and staying compliant across key regulations discussed below.
PCI-DSS: Protecting Payment Data
PCI-DSS exists because credit card data is enormously attractive to attackers. The standard requires companies to ensure cardholder data is encrypted, masked, and kept only where it belongs.
In practice, PCI data has a way of wandering.
- Primary Account Numbers end up in log files.
- Encryption keys get stored in the wrong place.
- Development environments get spun up from production databases that nobody bothered to sanitize first.
DSPM proactively identifies these scenarios. It detects when PANs appear in log files, flags unencrypted card data at rest, pinpoints where encryption keys are stored, and alerts on unauthorized access patterns. The goal is not just to fix issues after they appear. It is to prevent them from becoming audit findings or, worse, breach incidents.
GDPR: Know Where European Data is Present
GDPR compliance is not a one-time project. It is an ongoing obligation to know exactly what personal data you hold, why you hold it, who can see it, and when it needs to be deleted.
That is a tall order for any organization with significant cloud infrastructure. Data flows across accounts, SaaS platforms, and third-party processors.
The “data minimization principle” sounds easy until you realize that sensitive EU citizen data is often replicated across dozens of environments for analytics, testing, and backup purposes.
- DSPM detects PII across cloud accounts, SaaS providers, and managed services.
- It identifies where data is being held beyond its intended retention period
- It flags unauthorized access
- And it surfaces gaps in the organization’s ability to prove data protection.
HIPAA: Healthcare Data Has No Room for Error
Protected Health Information is one of the most regulated and most targeted categories of data in existence. HIPAA requires strict access controls, audit logging, backup procedures, and transmission security for all electronic PHI. That includes patient names, addresses, birthdates, Social Security Numbers, test results, insurance records, and more.
The challenge is that PHI doesn’t stay neatly in one database. It shows up in scanned images, unstructured documents, structured files, and backup repositories that nobody has looked at in years.
DSPM scans all of these. It identifies PHI at the most granular level, checks whether proper access controls and encryption are in place, and flags any gaps in logging or backup coverage.
For healthcare organizations moving toward cloud-based Electronic Health Record systems, DSPM is an urgent requirement. It’s the only scalable way to maintain a defensible HIPAA compliance posture as data volumes grow.
DPDPA: Why India’s New Privacy Law Demands a DSPM Approach
India’s Digital Personal Data Protection Act, commonly called DPDPA, came into partial force on November 13, 2025, with full enforcement phased through to May 2027. For organizations operating in India or handling data of Indian residents, the compliance clock is already ticking.
DPDPA readiness looks a lot like GDPR compliance, but with some important differences. DPDPA requires organizations to know where personal data is present, enforce purpose limitations, manage consent, delete data when it’s no longer needed, and report breaches to both affected individuals and the Data Protection Board without delay.
DSPM for DPDPA help organizations
- discover and classify Indian personal data across hybrid and cloud environments,
- map it against DPDPA obligations,
- and maintain the continuous audit-ready posture that the law demands.
Organizations can’t prove compliance once a year. DPDPA, like GDPR, expects continuous proof. DSPM makes that feasible.
DSPM in AI: A Growing and Underappreciated Risk
Most organizations understand that sensitive data in production databases needs to be protected. Fewer are thinking about what happens when that same data flows into a generative AI pipeline.
Large language models rely on organizational data for training and fine-tuning. RAG systems pull from internal data stores. Employees use AI assistants that process files containing sensitive information. Traditional data security tools, designed for structured databases, were not built for this environment.
DSPM in AI contexts means
- discovering sanctioned and shadow AI tools across the environment,
- monitoring what sensitive data those tools can access,
- and enforcing controls before sensitive information ends up in a model training dataset it was never meant to enter.
DSPM Strategies That Actually Help Reduce Risk and Stay Compliant
Many organizations adopt DSPM but fail to extract value. The difference usually comes down to strategy.
Effective DSPM strategies include:
- Prioritizing high-risk data first instead of scanning everything equally
- Focusing on access control issues, which are often the biggest risk factor
- Using risk scoring to guide remediation efforts
- Aligning DSPM outputs with audit requirements to reduce compliance workload
“DSPM is only useful if it helps us fix things faster, not just find them.”
That mindset is key. Detection without action does not reduce risk.
Conclusion
The regulatory landscape is evolving at a relentless pace, with frameworks like GDPR, HIPAA, PCI-DSS 4.0, and India’s DPDPA raising the bar for accountability. At the same time, data has become fluid, scattered, and difficult to track, making reactive security approaches ineffective.
This is exactly why addressing data security and compliance risks with DSPM in cybersecurity has become critical for modern organizations. DSPM brings much-needed clarity by offering continuous visibility, precise classification, and actionable risk insights. It works alongside existing security tools, focusing on what truly matters, the data itself. For organizations facing growing compliance complexity, DSPM is really essential.
Want to get started with DSPM? Contact our experts to implement the right DSPM solution for your environment.
Frequently Asked Questions
Can DSPM help with data compliance?
Yes, DSPM helps by discovering, classifying, and monitoring sensitive data while aligning it with regulatory requirements, making compliance easier and continuous.
How does DSPM help with regulatory compliance?
DSPM maps data to regulations, identifies risks, and provides audit-ready visibility to support compliance efforts.
What are the biggest data security and compliance risks with DSPM in cyber security?
Key risks include incomplete data discovery, misclassification, and over-reliance on automation without proper oversight.
How quickly can DSPM improve compliance posture?
Organizations often see improvements quickly, as DSPM provides immediate visibility into sensitive data and highlights urgent risks.
