Data is no longer just a business asset. It has become a growing liability if left unmanaged. As organizations adopt multi-cloud environments, SaaS platforms, and AI-driven workflows, sensitive data is spreading faster than most security teams can track or secure.
This rapid expansion has exposed a critical gap: organizations don’t just need better tools; they need better control over where their data exists and how it is protected.
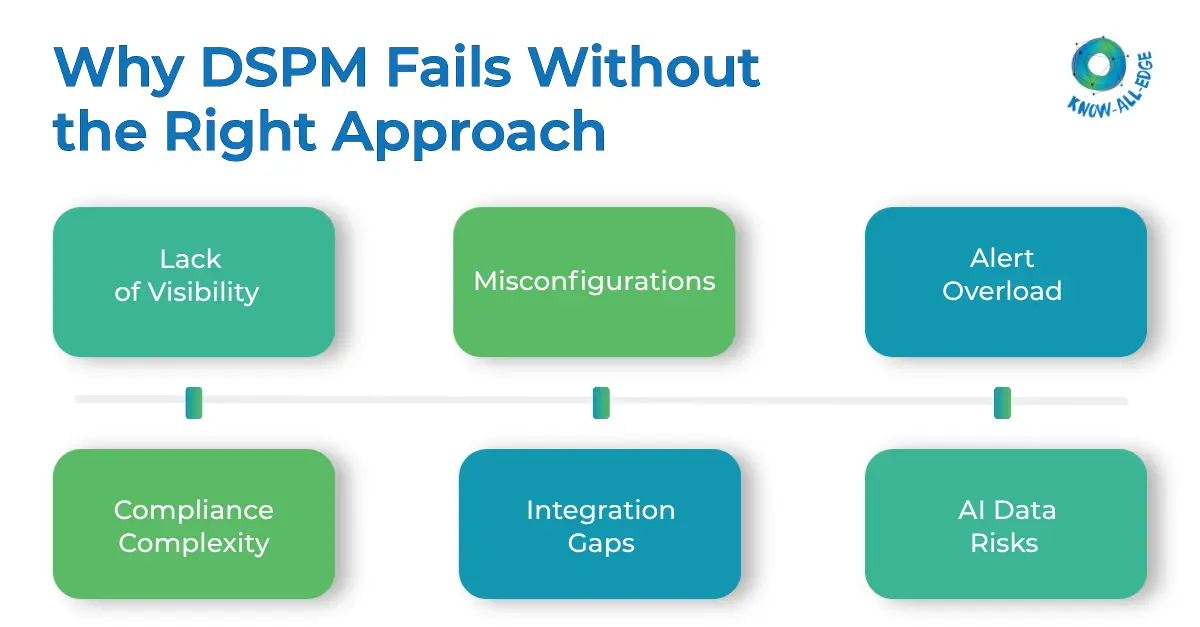
This is where Data Security Posture Management (DSPM) comes in. But despite its promise, many organizations struggle with challenges in DSPM that prevent them from getting real value out of their investments.
In this blog, we break down the most critical DSPM challenges, how they impact organizations, and the practical ways to fix them before they turn into serious security incidents.
Let’s first have a short understanding of DSPM.
What is DSPM?
Data Security Posture Management is a security framework, and a set of tools, that continuously discovers, classifies, and monitors sensitive data across cloud, on-premises, and hybrid environments.
It tells you where your data is present, who can access it, whether it is properly protected, and what risks exist right now.
Gartner coined the term in 2022 and predicted that by 2026, over 20% of businesses will prioritize DSPM technologies to discover and secure both known and unknown data repositories.
However, implementing DSPM is not simple. The challenges in DSPM often stem from real-world complexities like data sprawl, lack of visibility, compliance pressure, and evolving AI risks. Let’s move on to challenges.
Key Challenges in DSPM That Security Teams Struggle With
Even with the right tools in place, most organizations face recurring challenges in DSPM that limit visibility, slow down response, and increase overall data risk.
Challenge #1: The Data Visibility Problem
The most foundational challenge in DSPM is also the most frustrating one. You simply cannot secure data you do not know exists.
Most security leaders are flying partially blind, every single day.
Modern enterprises move fast. Teams spin up cloud storage buckets, SaaS tools, test environments, and developer sandboxes constantly. Data proliferates. Backups get created. Analytics pipelines pull copies of production data into places nobody thought to document. This is the “shadow data” problem, and it is relentless.
Traditional security tools were built around the network perimeter. They are not designed to follow data as it moves across AWS, Azure, Google Cloud, SaaS platforms, and legacy on-premise servers simultaneously.
DSPM fills that gap by providing automated discovery across all of these environments.
But the challenge is deployment scope. Many organizations implement DSPM narrowly, covering only their primary cloud provider, and miss the full picture.
The fix: Deploy DSPM with a mandate to cover every environment from day one, not just the ones you think matter. Integrate with all cloud service providers, SaaS tools, and any internal data store. Use automated classification, not manual tagging, because manual processes do not scale when data is growing as fast as it is today.
Challenge #2: Alert Overload is Quietly Killing Your Security Program
Here is a problem that does not get enough attention: DSPM tools are very good at finding problems.
A single DSPM scan can surface thousands of risk flags across an enterprise environment like:
- Misconfigured S3 buckets
- Over-permissioned access roles
- Unencrypted sensitive files in shared drives
- Stale data sitting in forgotten test environments.
The list goes on. And for a security team that is already stretched thin, receiving thousands of alerts without clear prioritization is the same as receiving no alerts at all.
This is what the industry calls the “context gap.” A tool flags a file as sensitive, but without understanding the business context around that file, engineers cannot determine whether to delete it, encrypt it, restrict access to it, or simply ignore it. The result is alert fatigue, and it is one of the most significant restraints on DSPM effectiveness right now.
The fix: Prioritization is everything. DSPM best practices strategies layer risk scoring on top of raw alerts, surfacing the issues most likely to result in a breach or compliance violation first.
Integrate threat intelligence feeds so your DSPM platform understands not just what is exposed, but what attackers are actively targeting. Automated remediation for high-confidence, low-complexity issues, like revoking unnecessary read permissions on a public bucket, should be standard.
Challenge #3: Compliance Is a Moving Target, and DSPM Needs to Keep Up
Regulatory pressure is not easing up. If anything, it is compounding. Organizations operating globally now have to manage GDPR in Europe, CCPA in California, HIPAA for health data, PCI-DSS for payment data, and increasingly, regional frameworks in emerging markets.
For Indian enterprises, this is especially relevant right now.
India’s Digital Personal Data Protection Act (DPDPA), which came into partial effect on November 13, 2025, introduces a comprehensive set of obligations around how personal data is collected, stored, and processed. Non-compliance carries penalties of up to Rs. 250 crore (approximately $28 million per violation).
DSPM for DPDPA is not optional for Indian businesses anymore. It is the mechanism by which they prove compliance to regulators, on demand.
The fix: Use DSPM as a live compliance dashboard, not a point-in-time audit tool. Map your data posture continuously against applicable regulatory benchmarks. Automated reporting and policy enforcement dramatically reduce the manual burden of audit preparation.
For DPDPA specifically, DSPM’s data discovery and classification capabilities directly support the Act’s requirements around data mapping, consent, and breach notification.
Challenge #4: When DSPM Meets AI: A Growing Security Gap
AI is changing everything about how data is used inside organizations. And it is creating a new class of challenges in DSPM that most existing tools are not equipped to handle.
Large language models need training data. RAG pipelines pull from enterprise data stores. AI agents autonomously access files, databases, and APIs. Each of these patterns introduces new risks around what sensitive data is being ingested, processed, or potentially leaked through AI outputs.
DSPM for AI is an emerging capability category.
Most existing DSPM tools provide minimal visibility into how AI systems are actually using sensitive data. Shadow AI is a real and growing problem. Employees adopt AI tools that IT has not approved, and those tools may be processing confidential customer data, financial records, or intellectual property without any governance in place.
The fix: Next-generation DSPM strategies need to explicitly scope AI systems as data access entities. That means
- discovering sanctioned and unsanctioned AI tools in use across the environment,
- monitoring what data those tools are accessing,
- and applying controls that prevent sensitive or regulated data from flowing into unvetted AI pipelines.
Challenge #5: DSPM Integration Complexity
Security stacks are not simple. Most enterprises already run SIEM platforms, endpoint detection tools, identity and access management solutions, and cloud-native security services.
DSPM solutions that operate in isolation provide incomplete protection. A tool that discovers sensitive data but cannot feed that context into your SIEM, or your IAM platform, or your DLP policy engine, forces analysts to context-switch constantly and leaves response gaps.
The fix: Evaluate DSPM solutions specifically on their integration ecosystem. Native connectors to major SIEM and XDR platforms are table stakes. Look for API-first architectures that allow custom integrations. And build a unified data risk workflow, from discovery in DSPM through to investigation in SIEM through to response via automation. Siloed tools create siloed thinking.
Conclusion
The challenges in DSPM are real, and they are not going away on their own. Visibility gaps, alert fatigue, regulatory complexity, AI-driven data risks, and integration friction all compound each other. But the organizations that take a structured, continuous approach to data security posture management, rather than treating it as a compliance checkbox, are building something more durable: actual confidence in where their data is and how it is protected.
The stakes have never been higher. With the DPDPA now in effect in India, GDPR enforcement tightening in Europe, and AI reshaping how data flows inside every enterprise, DSPM strategies are no longer optional. They are the foundation.
If you’re struggling with challenges in DSPM or unsure where to start, now is the time to act. Talk to our experts today to assess your data security posture and build a DSPM strategy that actually works for your environment.
Frequently Asked Questions
What is the difference between DSPM and traditional DLP?
DLP focuses on preventing data leaks using predefined rules. DSPM goes further by discovering, classifying, and continuously monitoring sensitive data across all environments.
How does DSPM handle unstructured data like emails, documents, and images?
Modern DSPM uses AI/ML to automatically identify and classify sensitive data across unstructured formats like emails, documents, and images.
What should organizations prioritize when starting their DSPM journey?
Start with data discovery and classification in high-risk environments, then build visibility into access and layer in risk scoring and compliance monitoring.
How does DSPM support incident response when a breach actually occurs?
DSPM provides instant visibility into affected data, access, and data flow, helping teams quickly assess impact and meet breach notification timelines.
